For a startup founder or CTO, the world of compliance often feels like a bowl of alphabet soup. You hear about SOC 2 from your enterprise prospects and HIPAA from your healthcare partners. You know they are important. You know that lacking them can kill a deal or result in a hefty fine. However, understanding the nuance between the two,and how to tackle them efficiently, is a different challenge entirely.
This guide breaks down SOC 2 and HIPAA specifically for the startup ecosystem. We will explore what they are, how they differ, and how you can implement them without slowing down your product velocity.
Part 1: What is SOC 2? The Gold Standard for SaaS
Service Organization Control 2 (SOC 2) is an auditing procedure developed by the American Institute of Certified Public Accountants (AICPA). SOC 2 is a compliance framework designed specifically for service organizations, such as SaaS providers, data centers, and IT services, to ensure they securely manage your data to protect the interests of your organization and the privacy of its clients.
Unlike many other frameworks, SOC 2 is a voluntary framework, not a strict set of rules that applies to everyone in the same way. Instead, it is a reporting framework. You define your controls, and an independent auditor verifies that those controls are designed appropriately and operating effectively.
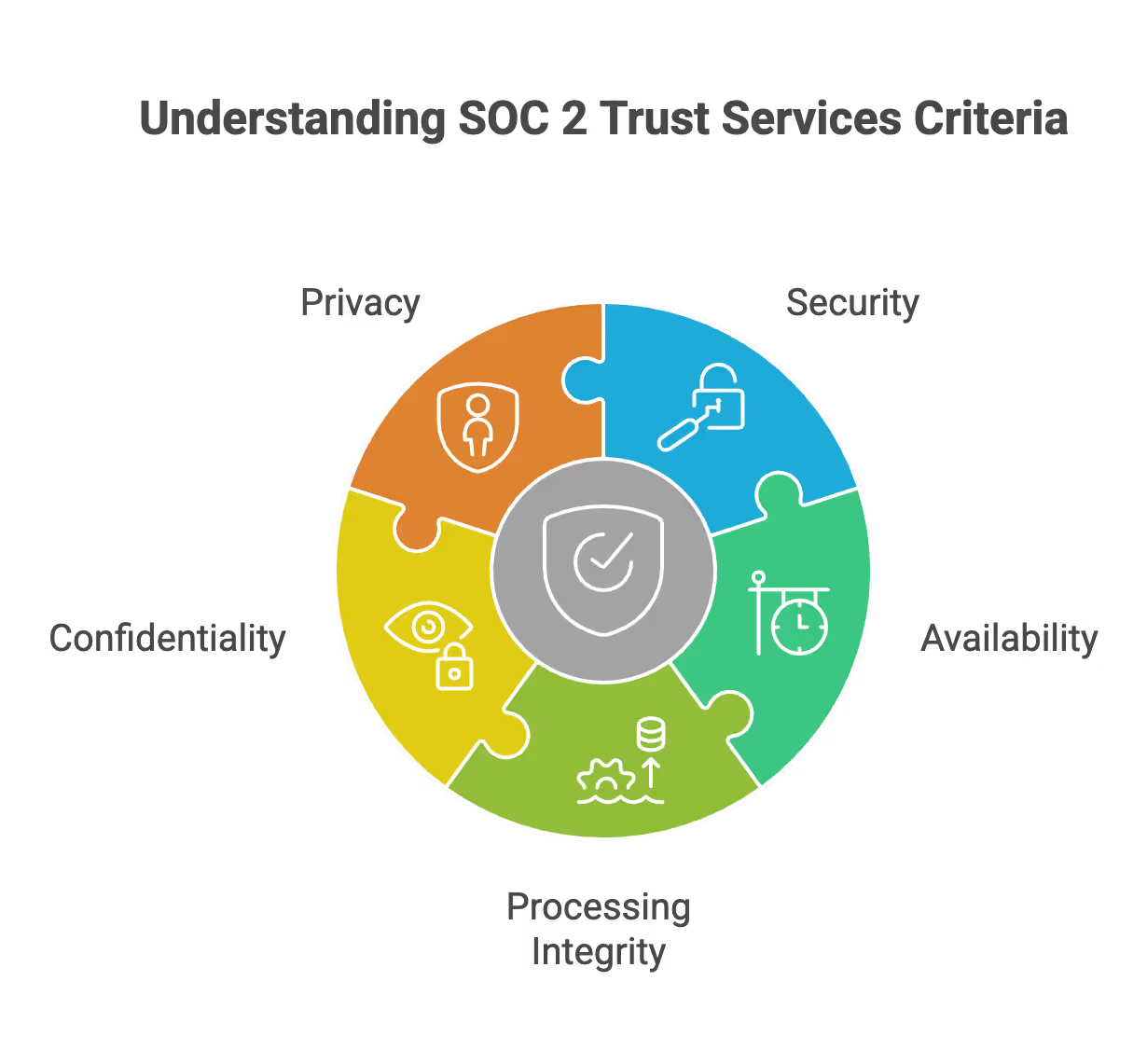
The Five Trust Services Criteria (TSC)
When pursuing SOC 2, you select which criteria are relevant to your business. Security is the only mandatory criterion, often referred to as the “Common Criteria.”
Security (Mandatory):
- This criterion refers to the protection of system resources against unauthorized access.
- It covers firewalls, intrusion detection, multi-factor authentication (MFA), and physical security.
- For most early-stage startups, the “Security” category alone constitutes a significant portion of the audit.
Availability:
- This addresses the accessibility of the system, products, or services as stipulated by a contract or service level agreement (SLA).
- It involves performance monitoring, disaster recovery plans, and incident response handling.
- If your startup promises 99.99% uptime to enterprise clients, this criterion is essential.
Processing Integrity:
- This addresses whether system processing is complete, valid, accurate, timely, and authorized.
- Data processing is a critical aspect of this criterion, ensuring that data is handled accurately, securely, and in compliance with standards.
- It is vital for fintech startups or data analytics platforms where data accuracy is the core product.
- It ensures that the data going in is processed correctly before coming out.
Confidentiality:
- This covers data that is designated as confidential, such as intellectual property, price lists, or sensitive business data.
- It focuses on encryption, access controls, and network firewalls.
- This is distinct from privacy; confidentiality usually refers to business data, whereas privacy refers to personal data.
Privacy:
- This addresses the system’s collection, use, retention, disclosure, and disposal of personal information.
- It aligns closely with the Generally Accepted Privacy Principles (GAPP).
- If you handle PII (Personally Identifiable Information) for consumers, this criterion is highly recommended.
Type 1 vs. Type 2: The Startup Dilemma
Understanding the difference between the two types of reports is critical for your timeline and budget.
- SOC 2 Type 1:
- This is a snapshot in time.
- The auditor looks at your system on a specific date (e.g., September 1st) and verifies that your controls are designed suitably.
- It is faster and cheaper, making it a good starting point for startups needing to unblock a specific deal immediately.
- SOC 2 Type 2:
- This covers a period of time, usually 3 to 12 months.
- The auditor verifies that your controls were operating effectively throughout that entire period.
- This is the gold standard. Enterprise buyers will eventually demand a Type 2 report because it proves you stick to your rules, not just that you wrote them down.
Part 2: What is HIPAA? The Law of the Land
The Health Insurance Portability and Accountability Act (HIPAA) is a United States federal law enacted in 1996. HIPAA is a compliance framework that sets standards for protecting health information and applies to organizations that handle protected health information (PHI). To achieve HIPAA compliance, organizations must implement safeguards and protocols to protect PHI and respond to potential breaches. Unlike SOC 2, which is voluntary (market-driven), HIPAA is mandatory if you touch protected health information (PHI).
The Department of Health and Human Services (HHS), specifically the Office for Civil Rights (OCR), enforces HIPAA. Violations can lead to civil and criminal penalties, which can be catastrophic for a cash-strapped startup.
Who Needs to Comply?
Startups often get confused about whether HIPAA applies to them. It usually comes down to two categories:
- Covered Entities:
- Healthcare entities such as healthcare providers (doctors, clinics, psychologists, dentists), health plans (insurance companies, HMOs), and healthcare clearinghouses. These organizations must adhere to HIPAA regulations when handling sensitive health information.
- Business Associates:
- This is where most startups fit in.
- If you are a SaaS platform, a cloud storage provider, or an analytics tool that processes, stores, or transmits PHI (including electronic health records) on behalf of a Covered Entity, you are considered a Business Associate.
- You must sign business associate agreements (BAAs) with your customers, which are legally binding and require you to comply with HIPAA. Vendors handling electronic health records must also ensure they meet HIPAA requirements.
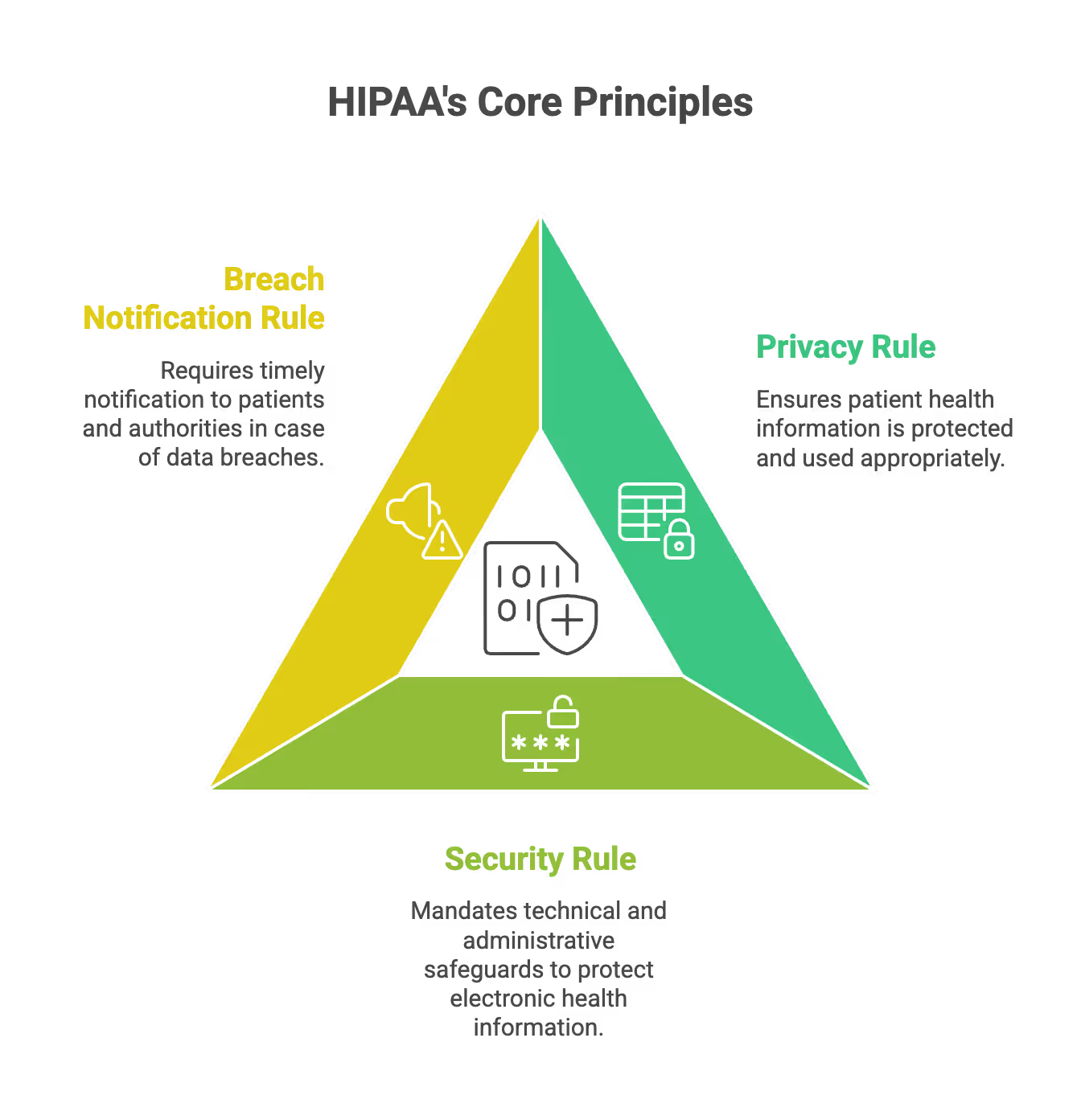
The Three Main Rules of HIPAA
HIPAA is vast, but for a tech startup, the focus is generally on three specific areas.
- The HIPAA Privacy Rule:
- This sets national standards for the protection of patient health information (PHI).
- It dictates how patient health information can be used and disclosed.
- It gives patients rights over their data, including the right to examine and obtain a copy of their health records.
- The HIPAA Security Rule:
- This is the technical heart of HIPAA for software companies.
- It establishes national standards for protecting electronic protected health information (e-PHI).
- It requires administrative, physical, and technical safeguards (more on this in the Best Practices section).
- The Breach Notification Rule:
- This requires Covered Entities and their Business Associates to provide notification following a breach of unsecured PHI.
- If you have a data leak, you are legally required to tell the government and the affected individuals.
- The clock starts ticking the moment you discover the breach, usually giving you 60 days or less to report.
Together, these rules form the core HIPAA compliance requirements for organizations handling PHI.
Part 3: SOC 2 vs. HIPAA – The Key Differences
While both frameworks deal with data security, their origins, enforcement, and goals differ significantly.
1. Motivation and Enforcement
SOC 2:
- Driver: The Market. Your customers demand it to trust you.
- Enforcer: No government body. It is enforced by the AICPA through licensed CPA firms.
- Consequence of failure: Loss of sales, reputational damage, and inability to close enterprise contracts. Achieving SOC 2 compliance helps build trust with customers by demonstrating your commitment to security and operational controls.
HIPAA:
- Driver: The Law. You must comply if you handle PHI.
- Enforcer: The U.S. Federal Government (HHS/OCR).
- Consequence of failure: Heavy fines (up to $1.5 million per year per violation category), potential jail time for negligence, and mandatory corrective action plans. Compliance violations can result in regulatory penalties and require organizations to implement corrective action plans to address deficiencies.
2. Scope of Data
SOC 2:
- Broad scope. It covers any data related to the service you provide.
- This includes customer data, source code, financial records, and employee information.
- It is industry-agnostic, used by everyone from marketing tech to HR software.
HIPAA:
- Narrow scope. It applies strictly to Protected Health Information (PHI).
- HIPAA is focused on protecting healthcare data, including PHI and other sensitive patient information.
- PHI includes 18 specific identifiers (like names, dates, SSNs, IP addresses) when linked to health status.
- If your startup collects data but none of it is health-related, HIPAA does not apply.
3. Certification vs. Attestation
SOC 2:
- You receive an “Attestation Report.”
- An auditor gives an opinion on whether you passed.
- You can share this report with customers under an NDA.
HIPAA:
- There is no official government “HIPAA Certification.”
- Third-party companies sell “HIPAA Certifications,” but these are merely external validations of your compliance program. They do not offer legal immunity.
- Compliance is a continuous state of adhering to the law, not a badge you earn once. Maintaining compliance with HIPAA requires ongoing oversight, monitoring, and policy adherence to ensure you continuously meet regulatory requirements.
Part 4: Startup Best Practices for Implementation
Whether you are pursuing SOC 2, HIPAA, or both, the operational reality for a startup is similar. You need to build a culture of security without drowning in paperwork. Aligning and streamlining your compliance efforts is essential to efficiently meet both SOC 2 and HIPAA requirements, reduce redundancies, and optimize resources.
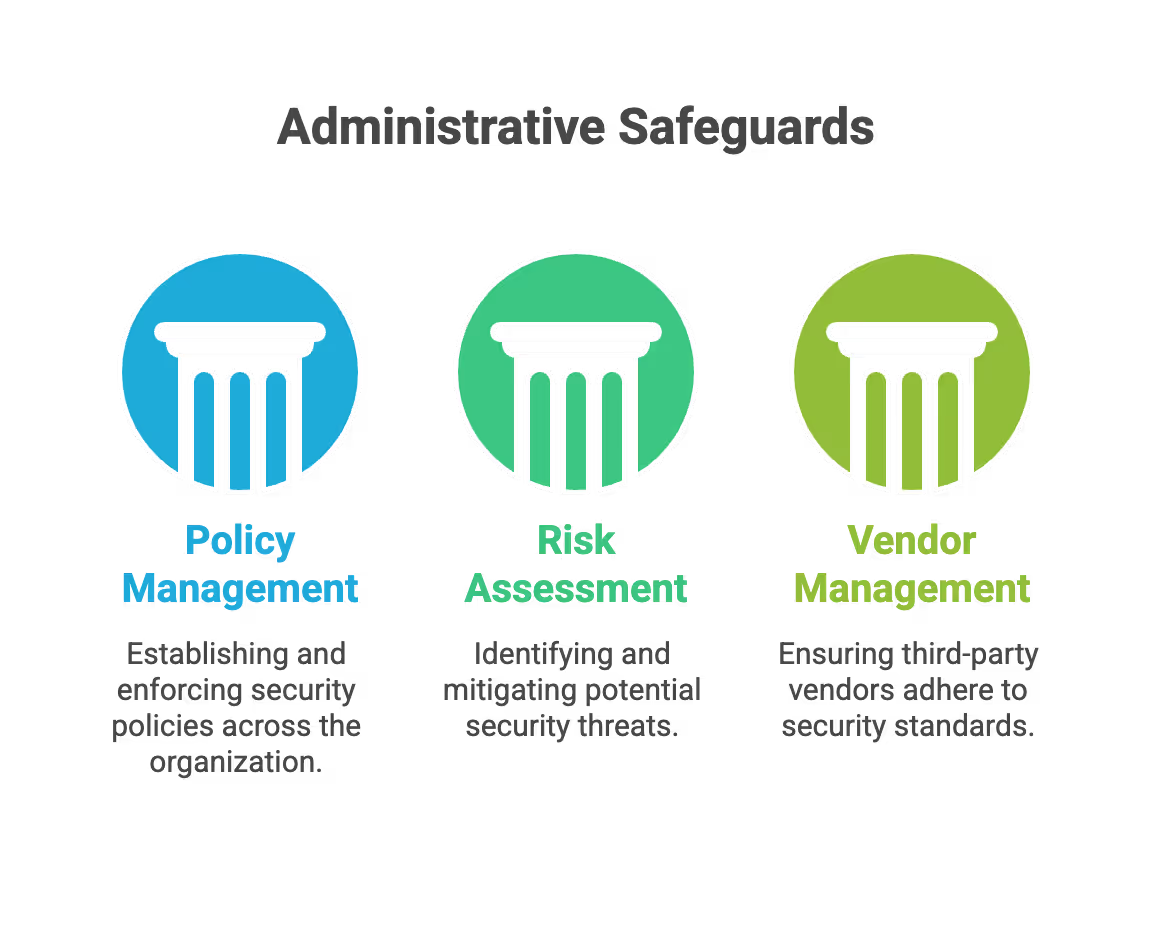
1. Administrative Safeguards (The "Paperwork" Layer)
This is about governance. Auditors and regulators want to see that management is involved in security, not just the engineering team.
Policy Management:
- Create a central repository for all security policies (Acceptable Use, Incident Response, Access Control).
- Require employees to review and acknowledge these policies annually.
- Use version control for your policies so you can prove what rules were in place at any given time.
Risk Assessment:
- Conduct annual risk assessments.
- Use risk assessments to identify threats (e.g., ransomware, insider threat, AWS outage).
- Score threats based on likelihood and impact during your risk assessments.
- Document your mitigation strategies for high-priority risks.
Vendor Management:
- You are responsible for the vendors you use.
- Create a checklist for onboarding new SaaS tools.
- Ensure your cloud providers (AWS, Google Cloud, Azure) and sub-processors are also SOC 2/HIPAA compliant.
2. Technical Safeguards (The "Code" Layer)
This is where your engineering team will spend the most time. Both SOC 2 and HIPAA demand rigorous technical controls.
Access Control:
- Implement the Principle of Least Privilege. Employees should only have access to the data they need to do their job.
- Enforce Multi-Factor Authentication (MFA) everywhere. No exceptions.
- Review access logs quarterly to remove permissions for terminated employees or role changes.
- Access controls are essential to protect sensitive data and sensitive information from unauthorized access, helping your organization meet SOC 2 and HIPAA requirements.
Encryption:
- Encryption at Rest: Ensure all databases, S3 buckets, and backup volumes are encrypted (e.g., AES-256).
- Encryption in Transit: Use TLS 1.2 or higher for all data moving over public networks.
- Key Management: Rotate your encryption keys regularly (e.g., annually) and store them securely using a service like AWS KMS.
- Encryption safeguards sensitive information and is a critical measure to protect sensitive data from breaches or unauthorized disclosure.
Change Management:
- Do not push code directly to production.
- Require code reviews (pull requests) for every change.
- Run automated tests (CI/CD) to check for security vulnerabilities before deployment.
- Keep a log of who approved what change and when it went live.
3. Physical Safeguards (The "Real World" Layer)
Even if you are a fully remote startup, physical safeguards matter. This concerns the devices your employees use and their working environments.
Device Management (MDM):
- Use Mobile Device Management software (like Jamf or Kandji) to enforce security on employee laptops.
- Enforce full-disk encryption (FileVault for Mac, BitLocker for Windows).
- Configure screens to lock automatically after 5 minutes of inactivity.
Workstation Security:
- Train employees not to leave laptops unattended in public spaces (coffee shops, airports).
- Ensure home Wi-Fi networks are password-protected.
- Establish a clean desk policy regarding sensitive notes or written passwords.
Part 5: Common Pitfalls and Issues to Avoid
Startups often make avoidable mistakes that delay their audit or leave them vulnerable to fines. Here are the most common issues.
- Fix: Treat compliance as an ongoing process, not a one-time project. Implement ongoing risk management practices to ensure continuous compliance with SOC 2 and HIPAA requirements. Leverage compliance automation platforms that enable continuous risk monitoring, providing proactive oversight of security controls and helping identify emerging threats.
1. The "Set It and Forget It" Trap
- The Issue:
- Founders rush to get a SOC 2 Type 1 report or sign a BAA, then ignore compliance for the rest of the year.
- The Consequence:
- When the Type 2 audit period arrives, the auditor finds huge gaps where controls weren’t running.
- For HIPAA, if a breach occurs and you haven’t updated your risk assessment in three years, you will be found negligent.
- The Fix:
- Treat compliance as a continuous process. Use compliance automation platforms (like Drata, Vanta, or Secureframe) to monitor your controls 24/7. Implement ongoing risk management and continuous risk monitoring to ensure SOC 2 and HIPAA compliance is maintained throughout the year, proactively identifying and addressing new threats as they arise.
2. Scope Creep (Over-scoping)
- The Issue:
- Startups try to include every single system and employee in the audit scope.
- The Consequence:
- The audit becomes expensive, unwieldy, and takes months longer than necessary.
- The Fix:
- Segment your network. Isolate the environment that handles customer data/PHI.
- Only include systems and people that actually touch sensitive data in the audit scope.
3. Copy-Pasting Policy Templates
- The Issue:
- Downloading generic policy templates and finding/replacing "[Company Name]" without reading them.
- The Consequence:
- You end up with policies promising things you don't do (e.g., "We inspect physical badges at the data center entrance" when you are 100% AWS-hosted).
- Auditors will catch this discrepancy immediately.
- The Fix:
- Customize every policy. Ensure it reflects your actual reality. It is better to have a simple policy you actually follow than a complex one you ignore.
4. Ignoring the "Business Associate Agreement" (BAA) Chain
- The Issue:
- A startup signs a business associate agreement with a hospital customer but forgets to sign business associate agreements with their own vendors (like their email provider or hosting service).
- The Consequence:
- This is a direct violation of HIPAA. Failing to have proper business associate agreements in place can result in compliance violations. If your vendor leaks data, you are liable because the chain of trust was broken.
- The Fix:
- Map out your data flow. Every external vendor that touches PHI must sign a business associate agreement with you.
5. Insufficient Employee Training
- The Issue:
- Treating security training as a boring onboarding checklist item that is never repeated.
- The Consequence:
- Human error is the leading cause of data breaches. An employee clicking a phishing link can bypass your expensive firewalls.
- The Fix:
- Conduct security awareness training at least annually.
- Run simulated phishing tests to see which employees need extra help.
- Make security part of the company culture, celebrating those who report suspicious activity.
Part 6: Overlap and Integration
The good news for startups is that SOC 2 and HIPAA have significant overlap. If you are building for one, you are likely 50% to 75% of the way to the other. Aligning your HIPAA compliance efforts with SOC 2 can streamline your processes and reduce redundant work.
Both frameworks are focused on protecting healthcare data, including sensitive patient information such as PHI. Integrating SOC 2 and HIPAA enhances data protection for healthcare organizations, helping build trust and meet regulatory requirements.
The "Map Once, Comply Twice" Strategy
Access Controls:
- HIPAA requires unique user identification and emergency access procedures.
- SOC 2 requires logical access security and user revocation.
- Implementation: One strong Identity Provider (IdP) like Okta or Google Workspace covers both. Regular risk assessments are essential to identify gaps in access controls and ensure ongoing compliance with SOC 2 and HIPAA.
Incident Response:
- HIPAA requires a response plan for reporting breaches.
- SOC 2 requires procedures for identifying and managing incidents.
- Implementation: Create one master Incident Response Plan (IRP) that includes specific addendums for who to notify in case of PHI involvement. Conducting risk assessments helps ensure your incident response plan addresses emerging threats and vendor risks.
Encryption:
- HIPAA calls encryption “addressable” (meaning you should do it unless impossible).
- SOC 2 Confidentiality criterion mandates it.
- Implementation: Encrypting your AWS RDS instances covers requirements for both frameworks simultaneously. Integrating encryption and other controls supports risk mitigation by reducing the likelihood of data breaches and regulatory penalties across both SOC 2 and HIPAA.
Part 7: Breach Notification – What Happens When Things Go Wrong?
Breach notification is a critical part of both SOC 2 and HIPAA compliance, requiring organizations to respond quickly and transparently when a data breach occurs. Under the HIPAA Breach Notification Rule, covered entities and business associates must notify the U.S. Department of Health and Human Services and affected individuals within 60 days of discovering a breach involving protected health information.
SOC 2 also emphasizes documented procedures for identifying, responding to, and communicating about security incidents, including notifying customers and partners as needed. Having a strong breach notification plan helps protect patient data, maintain trust, and demonstrate accountability by meeting both HIPAA and SOC 2 requirements.
Part 8: Compliance Audits – Proving You’re Doing the Right Thing
Compliance audits are essential for validating your organization’s security and privacy efforts. HIPAA audits, conducted by the Department of Health and Human Services Office for Civil Rights, focus on how well covered entities and business associates protect sensitive data and respond to incidents involving protected health information.
SOC 2 audits are performed by independent certified public accountants who assess controls based on the five Trust Services Criteria, including security and processing integrity. Regular audits help healthcare organizations and startups maintain a strong security posture, identify areas for improvement, and demonstrate commitment to protecting sensitive data while building trust with customers and regulators.
Part 9: Incident Response Plans – Preparing for the Unexpected
Despite strong security measures, incidents can still occur. Both SOC 2 and HIPAA require organizations to have detailed incident response plans to detect, contain, and recover from data breaches or other security events involving sensitive data. These plans should cover all stages of an incident, from detection and assessment to recovery and review. For HIPAA, documented procedures must ensure swift management of unauthorized access or disclosure of protected health information.
SOC 2 also emphasizes clear processes for identifying incidents, notifying stakeholders, and improving defenses. Regularly updating these plans helps healthcare organizations and startups minimize breach impacts, maintain compliance, and protect their reputation.
Part 10: Transparency and Communication – Building Trust with Clients and Patients
Transparency and open communication are essential for both SOC 2 and HIPAA compliance. Clients and patients expect to know how their data is protected and understand their rights. HIPAA requires covered entities to clearly inform patients about privacy practices and obtain authorization before sharing protected health information. Similarly, SOC 2 encourages organizations to be open about their security controls and to communicate proactively about breaches or policy changes. Prioritizing transparency helps healthcare organizations and startups build trust, reduce misunderstandings, and strengthen their reputation as reliable partners in data security and compliance.
How SecureLeap Supports Your SOC 2 Journey
SecureLeap focuses specifically on seed to Series B technology startups and SMB SaaS companies that need SOC 2 compliance, often for the first time, and lack a full time security leader.
Core Services
SecureLeap provides practical support across the entire SOC 2 journey:
- SOC 2 readiness assessments to identify gaps and create remediation roadmaps
- Control design and implementation tailored to cloud native startups
- Virtual CISO leadership for ongoing security guidance without full time headcount
- Policy drafting that reflects how your team actually operates
- Evidence management and coordination with CPA audit firms
- Risk assessment and risk management program development
Compliance Automation Integration
SecureLeap helps implement and manage compliance automation platforms like Drata, Vanta, and Secureframe. Integration with your existing cloud stack (AWS, Azure, GCP, GitHub, GitLab) enables automated evidence collection and operational effectiveness monitoring throughout your audit period.
Bundled Solutions
Enterprise customers often require both a SOC 2 report and an annual application or API penetration test. SecureLeap bundles these services together, handling both your compliance preparation and your technical security validation in a coordinated engagement.
Getting Started
SecureLeap offers free SOC 2 audit readiness consultations for startup CEOs and CTOs. During this call, you will receive:
- Custom timeline based on your deal deadlines
- Recommended Trust Services Criteria for your market
- Scope recommendations based on your infrastructure
- Estimated budget range for your specific situation
Schedule your consultation to validate your assumptions about scope and avoid over engineering controls that do not match your actual risk profile or customer requirements.
FAQ SOC 2 HIPAA Compliance
What is the main difference between SOC 2 and HIPAA?
SOC 2 is a voluntary market-driven framework for service organizations, while HIPAA is a mandatory federal law for any business handling protected health information. SOC 2 covers broad service security whereas HIPAA focus is strictly on healthcare data privacy.
What is a SOC 2 Type 2 report?
A SOC 2 Type 2 report evaluates whether security controls operated effectively over a period of 3 to 12 months. It is the gold standard for enterprise trust because it proves a company follows its security rules consistently over time.
Who is considered a Business Associate under HIPAA?
A Business Associate is any service provider, such as a SaaS platform or cloud host, that processes or stores health data for a healthcare entity. These startups must sign a Business Associate Agreement to legally comply with HIPAA regulations.
What are the penalties for HIPAA non-compliance?
Violations can lead to civil and criminal penalties with heavy fines reaching up to $1,500,000 per year per violation category. Negligence can also result in mandatory corrective action plans or even potential jail time.
Can a startup get an official HIPAA certification?
No, the U.S. government does not offer an official HIPAA certification. While third-party firms provide compliance validations, HIPAA is a continuous state of adhering to federal law rather than a one-time badge.


%20(17)%20(1).avif)

%20(10)%20(1).avif)
%20(4)%20(1).avif)