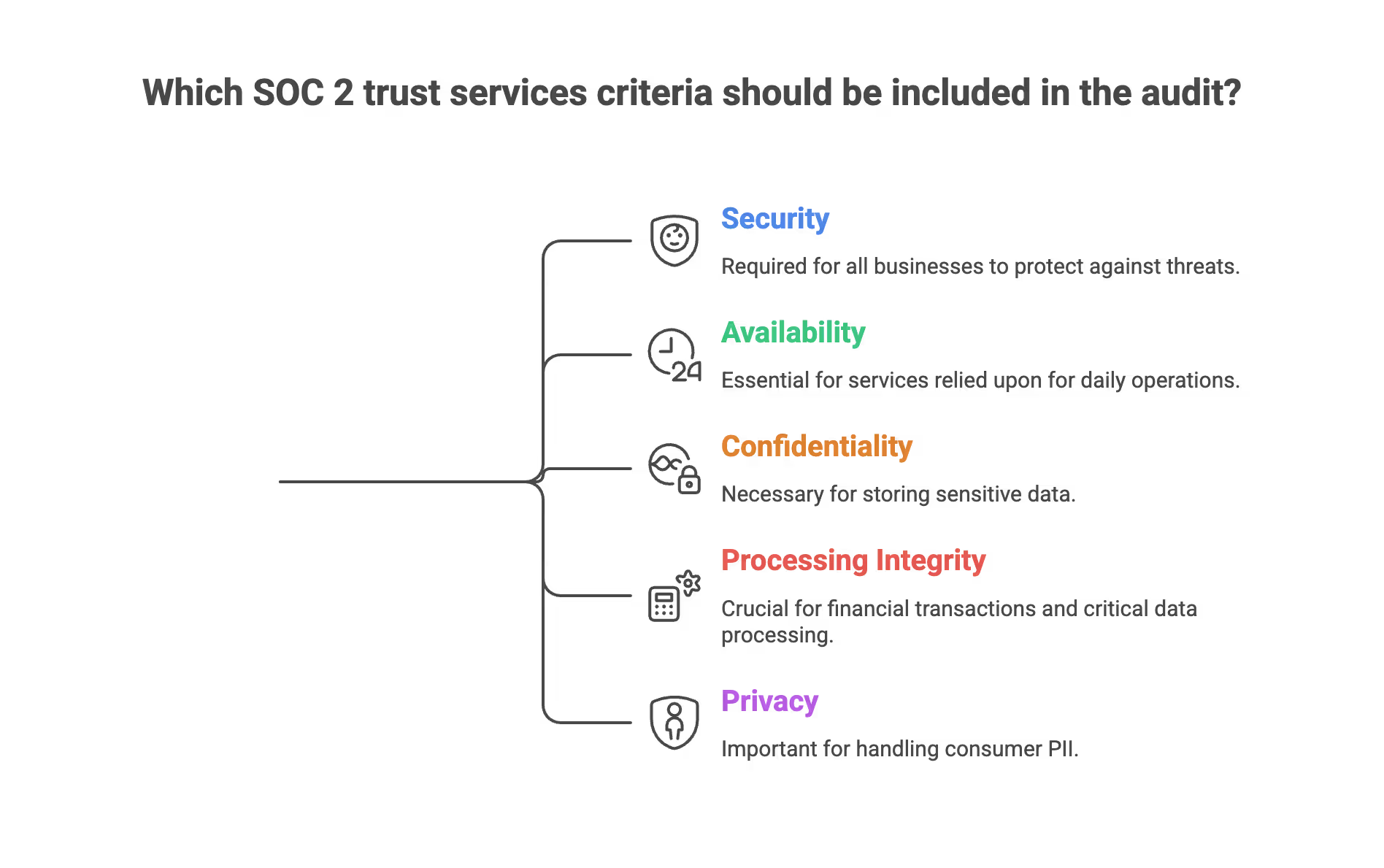
SOC 2 Trust Services Criteria (TSC) are the five categories established by the American Institute of Certified Public Accountants (AICPA) that define what a SOC 2 audit evaluates: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is the only mandatory category. All other criteria are optional and selected based on the services your organization provides.
KEY TAKEAWAYS
• SOC 2 has 5 Trust Services Criteria (TSC)
• Only Security is mandatory for every audit
• Availability, Processing Integrity, Confidentiality, and Privacy are optional — chosen by your scope
• First-time audits should focus on Security only
• Risk assessment is required across all selected TSC
When IT professionals, compliance officers, and business leaders search for the “5 Trust Services criteria of SOC 2,” they are typically looking for clarity on what these five categories (Security, Availability, Processing Integrity, Confidentiality, and Privacy) actually entail.
These are commonly referred to as the 'five criteria' that form the foundation of SOC 2 assessments. Organizations may also consider 'additional categories' or 'other criteria' beyond the core five, depending on their specific business needs and data handling requirements.
Preparing for a SOC 2 audit can be an overwhelming process, and organizations want to understand exactly what framework they are being measured against, which categories are mandatory for their business, and what internal controls they need to implement to pass their audit.

Created by the American Institute of Certified Public Accountants (AICPA), the SOC 2 Trust Services Criteria (TSC) form the foundational framework used by auditors to evaluate an organization’s systems and processes. The TSC includes 'points of focus' as guidance for implementing controls, but not all points are mandatory for every organization, these serve as helpful examples rather than strict requirements.
If you are gearing up for a SOC 2 audit, you do not necessarily need to be audited against all five categories. However, it is important to identify areas of risk or control gaps before the audit to ensure comprehensive coverage and improvement.
Understanding what each of the SOC 2 criteria means is the first step in properly scoping your audit and proving to your customers that their data is safe in your hands.
When scoping your audit, remember that the criteria and their system requirements apply to a wide range of organizational systems, not just IT, and the trust services criteria apply broadly across departments.
The SOC 2 framework is designed for any service organization that makes service commitments to customers regarding data security and privacy.
Here is a comprehensive breakdown of the five trust services criteria, what they mean, and how to determine which ones apply to your business.
1. Security
Security, in the context of SOC 2, is the only mandatory Trust Services Criterion. It requires that systems protect information and resources against unauthorized access, whether physical or logical, that could compromise the availability, integrity, confidentiality, or privacy of data.
What it means: Security is the only mandatory category in a SOC 2 audit. Often referred to as the “Common Criteria,” it serves as the baseline for the entire framework. If you are pursuing a SOC 2 report, you must include the Security criteria. The Security criteria is service organization relevant, meaning it applies to all service organizations and must be included in every SOC 2 audit, regardless of the organization's industry or size. It focuses on how well your organization protects its data and systems from malicious actors, unauthorized access, and vulnerabilities.
Examples of Controls:
- Implementing Multi-Factor Authentication (MFA) and strict password policies.
- Deploying firewalls, intrusion detection systems, and endpoint protection.
- Conducting regular vulnerability scans and penetration testing.
- Establishing role-based access controls (RBAC) to ensure employees only have access to the data they need to do their jobs.

A SOC 2 Type I audit typically takes 4–8 weeks to complete, while a Type II audit , which evaluates controls over a 6–12 month observation period, takes significantly longer, according to compliance platform Vanta's .
2. Availability
Availability is a SOC 2 Trust Services Criterion that evaluates whether a system remains accessible and operational according to the commitments and requirements defined in service level agreements (SLAs). It does not mandate a specific uptime percentage — it audits whether your controls support what you've promised.
What it means: Availability ensures that your systems, products, or services are accessible to your customers exactly when they need them, as stipulated in your Service Level Agreements (SLAs) or contracts. This criteria does not set a specific benchmark (like "99.99% uptime"); rather, it evaluates whether you have the proper controls in place to support and monitor your own promised accessibility and performance.
Examples of Controls:
- Disaster recovery and business continuity plans.
- Routine data backups and offsite storage.
- Network performance monitoring and capacity planning to prevent system overloads.
- Incident response plans to quickly restore services in the event of an outage.

3. Processing Integrity
Processing Integrity is the SOC 2 criterion that verifies system processing is complete, valid, accurate, timely, and authorized. It is most relevant to organizations whose services involve executing financial transactions, payroll calculations, or data transformations where errors have direct downstream consequences.
What it means: Processing Integrity is about making sure your system does exactly what it is supposed to do, without errors, omissions, or delays. The processing integrity criteria are the standards used to ensure that system processing is accurate, complete, and timely, providing reliable results without manipulation. It ensures that data is processed predictably and that your system is free from unauthorized or inadvertent manipulation. Data integrity is also crucial here, as it maintains the reliability and consistency of data throughout system operations, especially in processes like order fulfillment or financial transactions. This criteria is highly recommended for companies that execute critical transactions on behalf of customers, such as financial services, payroll processing, or large-scale data analytics.
Examples of Controls:
- Quality assurance (QA) and testing procedures.
- Data validation checks to catch input errors before they are processed.
- System monitoring to detect processing anomalies or batch processing failures.
4. Confidentiality
Confidentiality under SOC 2 protects business-sensitive information , such as trade secrets, pricing data, and intellectual property, that is designated confidential by agreement (e.g., NDAs). It is distinct from Privacy, which covers consumer personal data.
What it means: Confidentiality focuses on protecting sensitive business information that is restricted to a specific set of people or entities. The confidentiality category is a specific set of criteria aimed at protecting sensitive information and ensuring that only authorized users have access. This data might include intellectual property, trade secrets, financial records, pricing lists, or business plans protected by Non-Disclosure Agreements (NDAs). While “Privacy” focuses on personal data, “Confidentiality” is typically concerned with B2B data and proprietary corporate information. Organizations may choose to include additional criteria such as Confidentiality based on their business needs and data handling requirements.
Examples of Controls:
- Encrypting data both at rest and in transit.
- Strict network firewalls and access controls to limit who can view sensitive files.
- Secure data disposal and retention policies to ensure confidential data is permanently destroyed when it is no longer needed.

5. Privacy
Privacy under SOC 2 governs how an organization collects, uses, retains, discloses, and disposes of Personally Identifiable Information (PII), such as names, Social Security numbers, health records, and financial details. It aligns with AICPA's Generally Accepted Privacy Principles (GAPP).
What it means: The Privacy criteria is strictly concerned with Personally Identifiable Information (PII), which is data that can be used to identify an individual, such as names, social security numbers, health records, or financial details. The privacy category is a set of controls and criteria focused on protecting consumer data and ensuring compliance with privacy principles. It measures how your organization collects, stores, and handles this personal data in accordance with your organization’s privacy notice and external regulations.
Examples of Controls:
- Clear privacy policies that communicate to users how their data will be used.
- Opt-in/opt-out mechanisms to gather explicit user consent.
- Protocols for responding to user requests to access, correct, or delete their personal data.
- Anonymization or redaction of personal information where applicable.
How to Choose the Right Trust Services Criteria for Your Business
A common misconception is that a company must include all five SOC 2 trust services criteria in their audit. In reality, you only need to select the criteria that are relevant to the services you provide and the promises you make to your customers.
- Security is required for everyone. No exceptions.
- If your customers rely on your software for their daily operations (e.g., a B2B SaaS platform), you should include Availability.
- If you store proprietary client data, intellectual property, or confidential business strategies, include Confidentiality.
- If you process financial transactions, e-commerce orders, or large amounts of critical data, include Processing Integrity.
- If your business handles massive amounts of consumer PII (like a healthcare platform, HR software, or a B2C application), you should include Privacy.
Each criteria is supported by several associated points of focus, which provide detailed guidance for implementing effective controls and ensuring compliance with the SOC 2 trust services criteria.
Secureleap Tip : Unless your customer specifically requests it, focus your first SOC 2 audit on the Security criteria only. This approach simplifies the audit process, reduces complexity, and helps you establish a solid compliance foundation before expanding to additional criteria in future audits.
Risk Assessment and Management
Risk assessment and management are at the heart of the Trust Services Criteria (TSC) and play a critical role in any successful SOC 2 examination. Each of the five trust services criteria—security, availability, processing integrity, confidentiality, and privacy—requires organizations to proactively identify, evaluate, and address potential risks that could impact their systems and customer data.
Under the security criteria, organizations must regularly assess threats such as unauthorized access, data breaches, and system vulnerabilities. This involves a thorough risk assessment process to determine the likelihood and potential impact of these risks on your operations and customer trust. Once risks are identified, effective risk management strategies must be implemented. These include establishing robust control activities, such as access controls and monitoring controls, as well as developing incident response plans to quickly address security events.
The availability criteria focus on minimizing the risk of system downtime and ensuring that services remain accessible to customers. This means evaluating risks related to hardware failures, network outages, or cyberattacks, and implementing backup processes, disaster recovery plans, and business continuity strategies to reduce the impact of such incidents.
For processing integrity, organizations must assess risks that could compromise the accuracy, completeness, or timeliness of data processing. Controls such as automated data validation, system monitoring, and regular audits help ensure that data processing remains reliable and trustworthy.
Confidentiality and privacy criteria require organizations to identify risks related to the unauthorized disclosure or misuse of sensitive information. This includes evaluating how confidential information and personal data are stored, accessed, and transmitted, and implementing encryption, access restrictions, and secure data disposal practices.
By conducting regular risk assessments and maintaining a strong risk management program, organizations can reduce the likelihood of security incidents, data losses, and compliance failures. This not only helps meet the requirements of the trust services criteria but also builds confidence with customers and stakeholders that their data is being handled with the highest standards of integrity, confidentiality, and privacy.
Audit and Reporting
The SOC 2 audit and reporting process is designed to provide independent assurance that an organization’s systems and controls meet the rigorous standards set by the Trust Services Criteria (TSC). During a SOC 2 examination, a service auditor evaluates the organization’s control environment and system operations, focusing on how well the selected trust services criteria(security, availability, processing integrity, confidentiality, and privacy) are being met.
The audit process begins with a detailed review of the organization’s security controls, including both physical access controls (such as data center security) and logical access controls (like user authentication and authorization). Auditors also assess monitoring activities, change management procedures, and incident response plans to ensure that the organization can detect, respond to, and recover from potential risks and incidents.

Control activities are a key focus, as they demonstrate how the organization manages day-to-day operations to protect customer data and maintain system integrity. This includes evaluating business continuity planning, backup processes, and disaster recovery capabilities under the availability processing integrity confidentiality criteria.
The resulting SOC 2 report provides a comprehensive overview of the organization’s system, including a description of the security category and the specific control criteria used for evaluation. The auditor’s opinion details whether the controls are suitably designed and operating effectively to meet the selected trust services criteria. This report serves as a valuable tool for organizations to demonstrate their commitment to security, availability, processing integrity, confidentiality, and privacy to customers, partners, and regulators.
By undergoing a SOC 2 examination and sharing the resulting report, organizations can provide transparent assurance that their systems and controls are robust, reliable, and aligned with industry best practices—helping to build trust and support business growth in competitive markets.
How SecureLeap Helps Startups With SOC 2
SecureLeap focuses specifically on startups and small businesses rather than large enterprises. Our experience spans SaaS, fintech, and healthtech clients between pre seed and Series B stages, which means we understand the constraints you face.
Our approach combines advisory services, vCISO leadership, Pentesting, and implementation support for compliance automation tools such as Drata, Vanta, and Secureframe. This combination streamlines evidence collection and keeps internal teams focused on product delivery.
A typical engagement with SecureLeap includes:
- Running a SOC 2 readiness review to assess current state
- Prioritizing remediation tasks based on audit requirements and customer pressure
- Drafting security policies and operational controls
- Coordinating directly with your audit firm to reduce back and forth
- Managing the project timeline so lean engineering teams stay productive
If you are evaluating SOC 2, book a short consultation to review your pipeline, existing controls, and realistic timing without committing to a full audit immediately.
FAQ SOC 2 Trust Services Criteria
What are the 5 SOC 2 trust services criteria?
The five SOC 2 criteria are Security, Availability, Processing Integrity, Confidentiality, and Privacy. They form the foundational framework used by auditors to evaluate an organization.
Is the Security criteria mandatory for a SOC 2 audit?
Yes, Security is the only mandatory category in a SOC 2 audit and is often referred to as the Common Criteria. It serves as the baseline framework to protect data from unauthorized access.
What is the difference between Confidentiality and Privacy in SOC 2?
Confidentiality focuses on protecting sensitive B2B data like intellectual property and trade secrets. Privacy is strictly concerned with protecting consumer Personally Identifiable Information.
Do I need to include all five criteria in my SOC 2 audit?
No, you only need to select the criteria that are relevant to the services you provide to your customers. While Security is required for everyone, the other four are optional based on your business needs.
Why is risk assessment important for SOC 2 compliance?
Risk assessment helps organizations proactively identify and address potential threats to their systems and customer data. It ensures that effective control activities and incident response plans are implemented.
What is the difference between SOC 2 Type I and Type II?
A SOC 2 Type I report evaluates whether your controls are suitably designed at a single point in time. A Type II report evaluates whether those controls operated effectively over an observation period, typically 6–12 months. Enterprise customers almost always require Type II.
How long does a SOC 2 audit take?
A Type I audit typically takes 4–8 weeks from readiness to report issuance. A Type II audit requires a 6–12 month observation period before the auditor can evaluate operating effectiveness. Most startups spend 3–6 months preparing before beginning the observation window.
Which SOC 2 criteria do SaaS companies most commonly select?
Security is required for all. Availability is the most commonly added criterion for SaaS companies because enterprise customers need assurance about uptime commitments. Confidentiality is added when handling client IP or NDA-protected data. Privacy is added for products that handle consumer PII.