Getting a Service Organization Control 2 (SOC 2) report is rarely about fixing servers; it is mostly about fixing paperwork. Auditors need proof that you have rules and that you actually follow them. These rules are known as organization controls, which are essential for safeguarding data and ensuring system integrity within the SOC 2 framework.
If you are building your compliance program from scratch, do not try to write everything at once. Focus on these core documents. Make sure to identify the controls relevant to your SOC 2 audit, as understanding which controls apply to your organization is critical for effective compliance.
Well-designed SOC 2 policies not only support documentation and compliance but also streamline audit processes and strengthen overall data security.
Introduction to SOC 2 Compliance
SOC 2 compliance is foundational for any service organization that manages sensitive customer data. Developed by the American Institute of Certified Public Accountants (AICPA), the SOC 2 framework is built around five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
These criteria serve as a blueprint for organizations to safeguard customer data and ensure that systems are secure, reliable, and available when needed. Achieving SOC 2 compliance demonstrates to customers, partners, and stakeholders that your organization takes data protection seriously and has implemented the necessary controls to maintain the confidentiality, integrity, and availability of information.
By aligning your policies and procedures with the SOC 2 Trust Services Criteria, you not only meet regulatory requirements but also build a foundation of trust that can accelerate business growth and customer acquisition.

Essential SOC 2 Policies Every Organization Must Implement
1. Information Security Policy (ISP)
This is the “constitution” of your security program. It sets the tone for the organization, establishes data security as a core objective, and gives your security team the authority to enforce rules.
What to include:
- Scope: Does this apply to the whole company or just specific cloud services?
- Roles and Responsibilities: Who is the CISO? Who owns the data? Who signs off on risks?
- Confidentiality Policy: Outline how sensitive data is managed to ensure security and build trust with clients and partners.
- Conduct Policy: Set standards for employee behavior and ethics to maintain a secure and professional workplace.
- Enforcement: Clearly state the penalties for non-compliance. Without consequences, policies are just suggestions.
2. Access Control Policy
This section usually generates the most exceptions during an audit because it is tedious to manage. This policy dictates how users interact with your systems, with access controls being a core component to restrict and monitor user access to data and systems.
Key concepts to define:
- Principle of Least Privilege: Employees should only have the exact access needed to do their jobs, and nothing more.
- Provisioning: The specific steps taken to create an account when someone is hired.
- Deprovisioning (Termination): The “termed user” problem is a classic audit trap. You must set a strict window (e.g., 24 hours) for revoking access after an employee quits.
- Authentication Requirements: Mandate Multi-Factor Authentication (MFA) on all core systems.
- Authentication Mechanisms: Implement strong authentication mechanisms to ensure only authorized users gain access to critical systems and data.
- Periodic Access Reviews: Conduct regular audits of user permissions to verify and restrict access, enhancing your overall security posture.
- Password Policy: Establish requirements for strong passwords, enforce password expiration, and require the use of password managers to securely manage credentials across systems.
3. Change Management Policy
If you are a software company, this controls your engineering culture. Auditors focus heavily on how code moves from a developer’s laptop to the live production environment. Establishing a formal software development lifecycle policy is essential to guide secure coding practices, ensure regular testing, and meet compliance standards throughout the development process.
The “Segregation of Duties” requirements:
- Peer Review: No single person should be able to write code and push it to production without a second set of eyes.
- Environment Separation: You need distinct environments for Development, Staging, and Production.
- Test Data: Explicitly ban the use of live production data in testing environments unless it has been sanitized.
- Emergency Changes: Define a “break glass” procedure for fixing production issues at 2:00 AM when a formal peer review isn’t possible.
- Implement Processes: Establish validation, control, and quality assurance measures during code changes to ensure data accuracy, completeness, and system integrity.
4. Incident Response Policy (IRP)
You cannot prevent every incident, but you can control how you react. This document is your game plan for when things break, including how to prepare for and respond to security incidents.
The IRP Lifecycle:
- Preparation: Defining the Incident Response Team (Legal, Comms, Engineering) and ensuring readiness for various security incidents.
- Identification: Deciding what counts as an incident (e.g., a lost laptop, a failed login, or a data breach that requires a clear response plan).
- Containment: Stopping the bleeding, guided by your mitigation policy to prevent further damage.
- Eradication & Recovery: Removing the threat and restoring service, following your mitigation policy to manage and resolve incidents effectively.
- Communication: Who do you tell, and when? This must align with your customer contracts and legal obligations.
5. Risk Management Policy
This answers the auditor’s question: “How do you decide what to protect?” You need a formal methodology for identifying fear and uncertainty.
The process:
- Assessment Cadence: Define when you assess risk (e.g., Annually? Before every new product launch?).
- Scoring: Establish a method for scoring risks based on Likelihood vs. Impact, and ensure that appropriate controls are implemented to address identified risks.
- The Risk Register: This is the output: a living spreadsheet tracking known risks and management’s decision to either fix them (mitigate) or live with them (accept). As part of risk assessment and control evaluation, maintaining data accuracy is essential for reliable decision-making and compliance.
Additionally, identify the minimum necessary functions required to maintain business continuity during risk events, ensuring your organization can recover core operations effectively.

6. Vendor Management Policy
You are responsible for the security of the tools you buy. If your cloud provider or chat app gets hacked, it becomes your problem. It is also crucial to ensure that your vendors properly manage customer data in line with your SOC 2 policies, as this directly impacts your compliance and risk posture.
Vendor controls:
- Onboarding: You need a security review process before any department buys new software.
- Right to Audit: Ensure contracts allow you to review their security posture.
- Continuous Monitoring: Check your critical vendors annually. Do not just sign a contract and forget about them.
- Data Processing: Evaluate your vendors' data processing practices to ensure they maintain data integrity, process information accurately and securely, and comply with your SOC 2 requirements.
7. Data Classification Policy
Not all data is created equal. You cannot protect everything with the same intensity, so you must label it. To ensure proper handling, it is essential to classify sensitive data based on its risk and impact.
Common classification levels:
- Public: Marketing materials, website content.
- Internal: Employee handbooks, non-sensitive memos.
- Confidential: Customer lists, pricing strategies, source code.
- Restricted: Credit card numbers, health data, passwords.
Handling requirements: Define specific rules for each level, such as “Confidential data must be encrypted at rest” or “Restricted data requires a specific VP’s approval to access.” Protect sensitive data through appropriate access controls, monitoring, and secure handling practices.
- Establish an encryption policy that outlines how sensitive data should be encrypted, specifying the types of data and encryption methods to be used.
- Implement data handling procedures for securely storing, transmitting, and disposing of sensitive data, ensuring compliance with SOC 2 requirements.
8. Physical Security Policy
Even for remote companies, physical security matters.
For offices:
- Badges and visitor logs.
- Locked server rooms.
- CCTV retention, with intrusion detection systems as part of the monitoring infrastructure.
- Control and monitor physical access to all facilities, including the use of access controls and monitoring systems.
- Secure data centers with physical security measures such as restricted access, surveillance, and environmental safeguards.
- Prevent unauthorized physical access to protect company assets and sensitive areas.
For remote work:
- Care for Laptops When Traveling: Ensure laptops are securely handled and never left unattended during travel.
- Keep Home Network Updated: Regularly update and secure your home Wi-Fi network to protect against unauthorized access.
9. Business Continuity & Disaster Recovery (BC/DR)
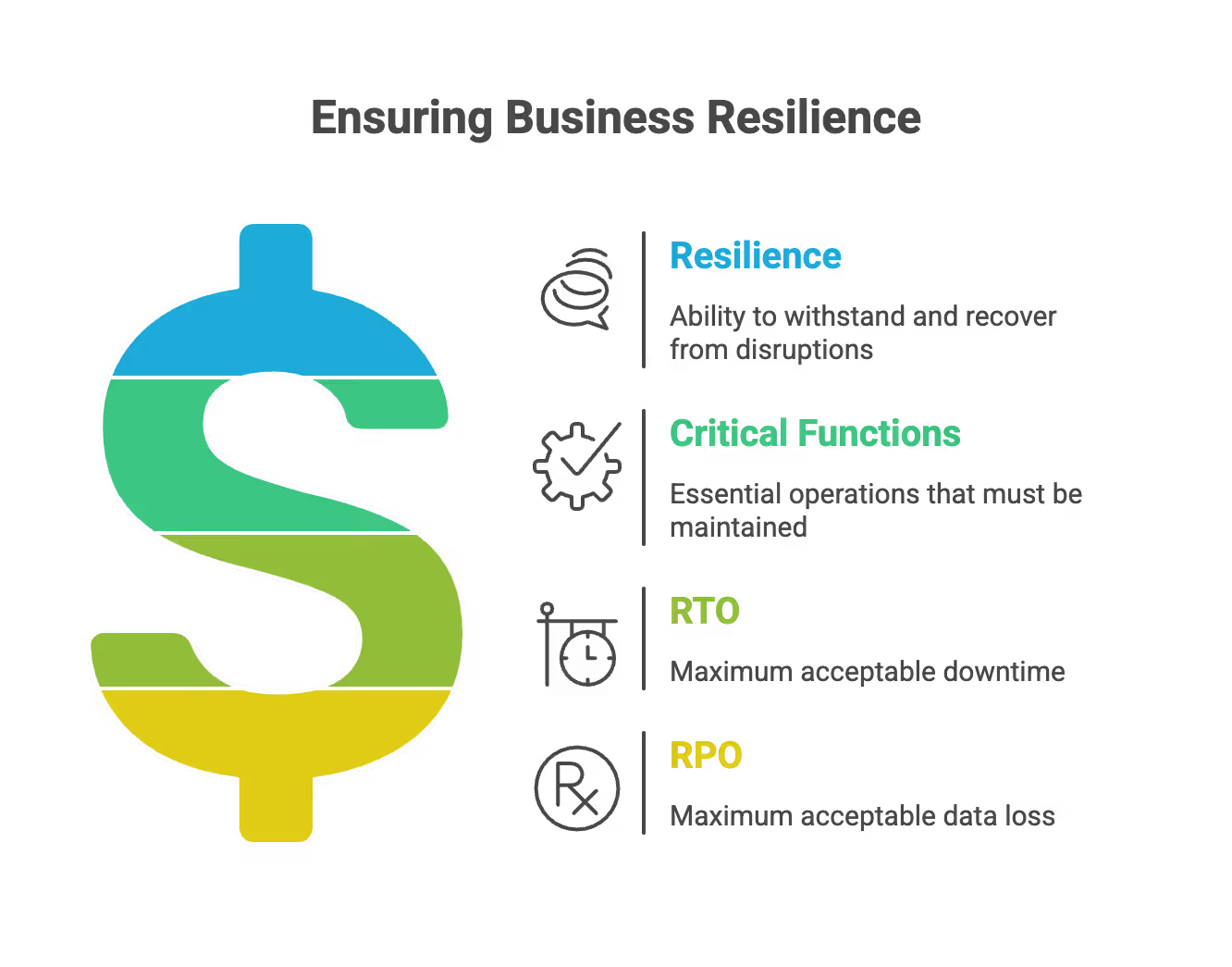
This is about resilience. A formal business continuity policy is essential to ensure your organization can maintain or quickly restore critical functions after disruptive events. You need to define two critical metrics:
- RTO (Recovery Time Objective): How much time can you afford to be offline? (e.g., “We must be back up within 4 hours.”)
- RPO (Recovery Point Objective): How much data can you afford to lose? (e.g., “We can lose the last 15 minutes of transactions.”)
A comprehensive disaster recovery policy provides guidelines and instructions for recovering from disastrous events, and should be closely aligned with your business continuity planning. Developing and maintaining disaster recovery plans is crucial for organizational resilience and swift recovery after disruptions or failures.
Your system backup policy should outline formal procedures for securely storing and recovering business application data and system information in case of disaster or data loss.
To streamline your planning, consider using a business continuity plan template to structure your continuity and recovery strategies, helping mitigate risks and enable rapid recovery during disruptions.
Note: You must test your backups. Taking backups is not enough; you have to prove you can restore from them.
10. Human Resources Security
People are often the weakest link. This policy covers the security aspects of the employment lifecycle.
- Pre-employment: Background checks and screening.
- Onboarding: Signing confidentiality agreements (NDAs) and Acceptable Use Policies (AUP), including guidelines for using the organization's communication mediums such as email, company devices, and networks to ensure proper and acceptable communication practices.
- Training: Mandated security awareness training upon hire and annually thereafter, with a focus on protecting sensitive information, including financial data, and maintaining its confidentiality.
- Sanctions: A clear disciplinary process for employees who violate security policies.
11. Workstation & Mobile Device Policy
This governs the hardware your employees touch every day. The requirements for securing these devices are typically outlined in your workstation security policy, which sets rules and guidelines to reduce risks like unauthorized access and data loss.
Must-haves:
- Full-Disk Encryption: If a laptop is left in a taxi, the data must be unreadable.
- Endpoint Defense: Antivirus or EDR (Endpoint Detection and Response) software must be installed and active.
- OS Updates: Operating systems must be patched automatically.
- MDM (Mobile Device Management): If you allow “Bring Your Own Device” (BYOD), you need a way to remotely wipe company data if the phone is lost.
- Technical Controls: Implement security measures such as encryption, antivirus, and MDM to safeguard devices and ensure audit readiness.
12. Software Development Lifecycle
An effective Software Development Lifecycle (SDLC) policy is crucial for ensuring secure software development aligned with SOC 2 compliance.
Key points:
- Secure coding guidelines to prevent vulnerabilities.
- Regular code reviews to ensure code quality and security.
- Automated testing to detect issues early in development.
- Continuous monitoring of the development process for threats.
- Incorporation of risk management and vulnerability assessments.
- Periodic penetration testing to evaluate security posture.
- Alignment of SDLC practices with SOC 2 compliance requirements.
- Focus on protecting sensitive customer information throughout development.
Security Policy Implementation Strategy
Writing the documents is the easy part. Getting people to follow them is the hard part.
- Collaborate, don't dictate: If you write a Change Management policy that is too strict, developers will bypass it. Work with them to find a process that is compliant but fast.
- Review annually: Set a recurring calendar invite. A policy written three years ago might reference tools you don't even use anymore.
- Keep it simple: Auditors prefer clear, concise language. If your employees can't understand the policy, they will ignore it.
Best Practices and Conclusion
To achieve and maintain SOC 2 compliance, organizations should adopt a set of best practices that reinforce the security and integrity of customer data. Start by developing clear, comprehensive policies and procedures that address all aspects of your operations, from access management and data classification to incident response and vendor management.
FAQ SOC 2 Security Policies
What are the essential SOC 2 policies?
Key policies include Information Security, Access Control, Change Management, Incident Response, and Risk Management. Organizations must also implement policies for vendor management, data classification, and physical security.
What is the Information Security Policy in SOC 2?
This policy acts as the constitution of your security program and establishes data security as a core objective. It defines roles, responsibilities, confidentiality, and enforcement rules for the organization.
How does Change Management work in SOC 2?
Change Management controls how code moves from development to production to ensure security. It requires peer reviews, separate environments for staging and production, and strict testing procedures to prevent unauthorized changes.
What is the difference between RTO and RPO?
RTO refers to how much time you can afford to be offline after a disruption. RPO defines how much data you can afford to lose, such as the last 15 minutes of transactions.
Why is a Vendor Management Policy necessary?
You are responsible for the security of the tools and cloud providers you use. This policy ensures you review vendor security before purchase and conduct continuous monitoring to protect your data.