If you’re running a B2B SaaS company and you’ve started fielding security questionnaires from enterprise prospects, you’ve probably encountered the question: “Do you have SOC 2?” This guide breaks down exactly what soc 2 compliance means for startup founders, why it matters for closing deals, and how to get there without derailing your product roadmap.
What SOC 2 Compliance Really Means (Fast Answer for Busy Founders)
Let’s cut straight to it. When someone asks if you’re “SOC 2 compliant,” they’re asking whether an independent firm of certified public accountants has formally attested that your security controls meet the AICPA’s trust services criteria. It’s not a certification you earn once and display forever. It’s an attestation tied to a specific point in time or observation period.
For a typical B2B SaaS, “being SOC 2 compliant” practically means:
you’ve completed a SOC 2 Type I or Type II audit in the last 12–18 months, and you can share that soc 2 report under NDA with prospects, customers, and investors.
Why does this matter for your startup?
Because SOC 2 directly impacts deal velocity. Instead of spending weeks filling out 200-question security questionnaires, you hand over your report. Instead of stalling at procurement’s security review, you keep moving. When an enterprise buyer asks “Do you have SOC 2?”, you answer with documentation, not excuses.
SecureLeap specializes in helping early-stage SaaS teams get from “no program at all” to audit-ready in a predictable timeline. If you’re tired of losing deals because you can’t answer the SOC 2 question, schedule a free consultation to map out your path.

What Is SOC 2? Framework, Origin, and Core Concepts
SOC 2 (System and Organization Controls 2) is a security and privacy framework defined by the American Institute of Certified Public Accountants (AICPA) specifically for service organizations, especially cloud providers and saas companies. It provides a standardized way to demonstrate that your organization manages risk around customer data responsibly.
A soc 2 report describes and tests your internal controls related to systems that store, process, or transmit sensitive customer data. If your production environment runs on AWS, GCP, or Azure, your SOC 2 scope would typically include how you manage access, monitor threats, handle changes, and protect that infrastructure.
The framework emerged around 2010 as cloud adoption surged and enterprises needed a way to evaluate the security posture of their vendors beyond just financial reporting. By 2026, holding a SOC 2 Type II report has effectively become the gold standard for technology companies selling to mid-market and enterprise accounts in North America.
Here’s what makes SOC 2 practical for startups: it’s technology-agnostic. You can run on any cloud stack or hybrid infrastructure. What matters is how you manage risk, enforce access controls, maintain logging, and handle change control, not which specific tools you use.
The Trust Services Criteria (TSC) in SOC 2
SOC 2 is built around five trust services criteria, and list them briefly: 1) Security (mandatory) 2) Availability 3) Processing Integrity 4) Confidentiality 5) Privacy.
Every soc 2 report must include Security (also called the Common Criteria). The other four criteria are selected based on your product’s risk profile, your customers’ requirements, and your contractual commitments.
A startup’s first SOC 2 scoping conversation usually involves deciding which criteria to include so that you cover what your customers care about without creating unnecessary audit burden. Here’s how different SaaS products might approach this:
This flexibility means you can start with a focused scope and expand in future audit cycles as your product and customer base mature.
What Does SOC 2 Compliance Mean in Practice?
Understanding the soc 2 compliance meaning goes beyond theory. It’s about your controls, documentation, and operational behavior being tested by an independent CPA firm against relevant auditing standards.
Here’s the distinction:
SOC 2 compliance: you meet the trust service principles through your controls and processes.
SOC 2 report: the formal document from a CPA firm that attests to that compliance for a defined period.
At a high level, compliance typically means you have:
– written security policies that people actually follow,
– technical controls implemented (MFA, least privilege, logging, backups, etc.),
– repeatable processes for onboarding/offboarding, change management, incident response, and vendor management.
The framework is flexible by design. Two saas companies can both be compliant with different specific controls, as long as they effectively meet the same criteria. A 10-person startup won’t have the same controls as a 500-person enterprise, but both can demonstrate they’re protecting client data appropriately for their context.
SecureLeap helps founders translate abstract criteria into concrete, lightweight controls aligned with startup speed. We work with tools you likely already use: Google Workspace, Okta, GitHub, Jira, and cloud-native security features, rather than forcing you to adopt an entirely new stack.
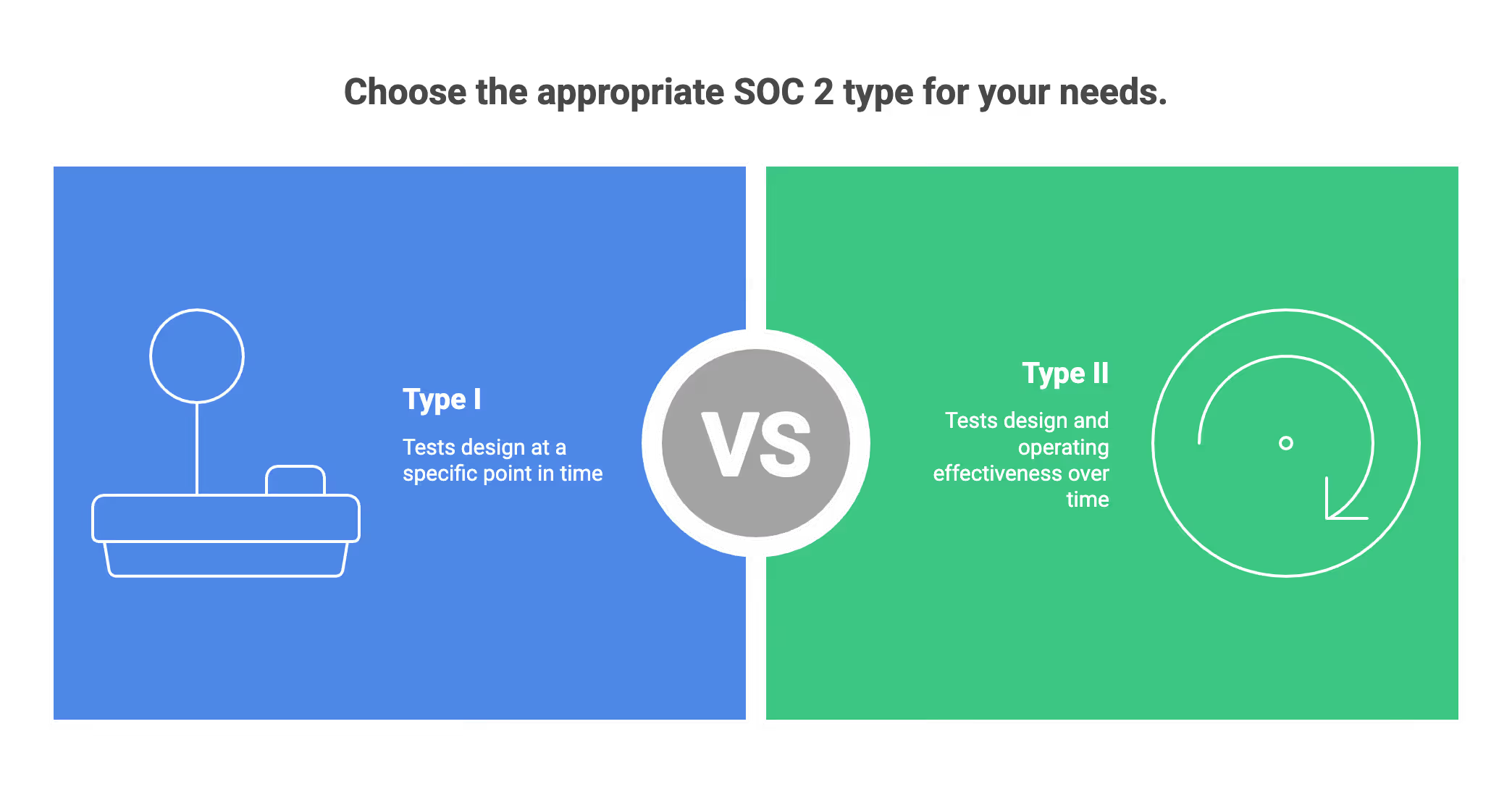
SOC 2 Type I vs. Type II and What “Compliant” Usually Implies
When enterprise customers ask about SOC 2, they almost always mean Type II. Here’s the difference:
Type I tests the design of controls at a specific point in time (e.g., “as of October 31, 2025”). It’s a snapshot that says “yes, these controls exist and are designed properly.”
Type II tests design and operating effectiveness over a period—commonly 6–12 months. It says “these controls not only exist but have been operating effectively throughout this observation window.”
The typical startup path looks like this:
– conduct a readiness assessment and close gaps,
– optionally do a Type I for quick market signal,
– then move to recurring annual Type II reports.
That said, early-stage SaaS teams with pressing deals sometimes jump straight to Type II with an initial 3–6 month observation period, then extend to 12 months in subsequent cycles. This approach gets you the more valuable report type faster.
SecureLeap can help you decide whether to start with Type I or go directly to Type II based on your current pipeline, burn rate, and investor expectations. There’s no one-size-fits-all answer.
Why SOC 2 Compliance Matters for SaaS & Startup Founders
SOC 2 isn’t about checking a compliance box. It’s about revenue access, deal velocity, and risk management. By 2025–2026, most mid-market and enterprise buyers treat SOC 2 as a default vendor requirement in security questionnaires and RFPs.
Without SOC 2, startups often:
– stall late-stage deals,
– face weeks of custom security reviews,
– lose to competitors who can attach a soc 2 report to their reply.
Beyond closing deals, SOC 2 brings internal value. The process forces you to gain visibility into your cloud footprint, clarify responsibilities, and establish incident response procedures. When an employee leaves or a security incident occurs, you’re not scrambling; you have playbooks.
If you’re losing or delaying deals because of missing SOC 2, talk to SecureLeap about mapping a realistic 3–12 month path to compliance.
Building Trust and Shortening Sales Cycles
A recent SOC 2 Type II report dramatically simplifies vendor due diligence. Instead of filling out those 200-question spreadsheets that procurement sends, you share your report under NDA and answer a small set of follow-ups. Your auditor’s opinion carries weight that your own assertions cannot.
Consider this scenario:
You’re a Series A SaaS selling into a Fortune 500 healthcare system. Their procurement team explicitly requires a soc 2 report dated within the last 12 months. Without it, you don’t make it past the initial security review. With it, you move straight to contract negotiation.
SOC 2 compliance is now a common checkbox in procurement systems like Ariba and Coupa. Having your report prepared lets you keep sales cycles measured in weeks instead of quarters. According to industry analyses, compliant SaaS companies see up to 40% improvement in RFP success rates and 2x faster sales cycles.
This is about business operations, not just good security practices.
Reducing Security and Compliance Risk
SOC 2 controls directly reduce real-world security incidents. Proper access management lowers the likelihood of credential theft. Configuration monitoring catches misconfigured S3 buckets before they become data breaches. Vendor risk management ensures third party vendors aren’t introducing vulnerabilities into your stack.
Here’s a common scenario we see during readiness assessments:
A startup discovers that former employees still have admin access to production systems months after leaving. Fixing this prevents both audit exceptions and serious insider risk. It’s the kind of gap that seems obvious in hindsight but goes unnoticed until someone systematically checks.
Alignment with SOC 2 also helps with overlapping obligations. If you’re a healthtech company handling protected health information, many HIPAA security requirements overlap with SOC 2 controls. Same for GDPR and state privacy laws. Building a strong security posture once lets you prove compliance across multiple frameworks without starting from scratch each time.
Investors and boards increasingly ask early-stage companies about SOC 2 to gauge operational maturity. With data breaches costing SaaS firms an average of $4.45 million per incident (per IBM’s Cost of a Data Breach Report), demonstrating strong internal controls signals that you’re a responsible steward of sensitive information.

The Five SOC 2 Trust Services Criteria Explained for Startups
This section breaks down each trust services criteria from a founder’s perspective—what it means day-to-day for a small engineering and ops team, not abstract compliance theory.
A typical seed–Series B SaaS will almost always include Security, then selectively add other criteria based on service level agreements, data sensitivity, and what user entities (your customers) explicitly require.
Security (Common Criteria – Mandatory)
Security is the foundation of every soc 2 audit and is always in scope. It covers protection against unauthorized access, system abuse, intrusion detection, and other security events that could compromise sensitive data.
For startups, the security principle translates to these core expectations:
– MFA enforced for all production and admin systems,
– least-privilege access via SSO/IdP,
– secure software development practices (code review, dependency scanning),
– logging and alerting for critical events.
Practical examples for your team:
- GitHub branch protections requiring pull request reviews before merging to main
- AWS IAM roles following least-privilege with regular access reviews
- Endpoint protection on all employee laptops
- Password and MFA policies enforced through Google Workspace or Microsoft 365
- Centralized logging via CloudWatch, Datadog, or Splunk with alerting on anomalies
SecureLeap often starts SOC 2 programs by maturing exactly these basics using tools startups already pay for. You don’t need to buy enterprise security suites: native AWS security services plus lightweight monitoring gets you most of the way there.
Availability
Availability is about your service being up and usable as promised in your SLAs. If you commit to 99.9% uptime, you need controls to back that up. This isn’t about being “online 24/7 at any cost”—it’s about meeting your documented commitments.
Key control themes include:
– documented SLAs and internal SLOs,
– monitoring and alerting for uptime and performance,
– backup and restore procedures with periodic tests,
– disaster recovery plans and incident response playbooks.
Example: A SaaS that commits to 99.5% uptime needs health checks, on-call rotation schedules, and tested restore-from-backup procedures. During the audit, you’ll provide evidence that backups actually work typically logs showing successful restoration tests quarterly.
If you don’t make strong uptime promises or your clients don’t require it, you can initially exclude Availability to keep scope and cost manageable. Add it when you sign customers with explicit uptime requirements in their contracts.
Processing Integrity
Processing integrity ensures systems process data accurately, completely, and on time. This matters most for financial calculations, billing systems, or critical analytics where errors have real consequences.
Control examples include:
– automated reconciliation checks for billing or transaction systems,
– validation on data inputs (no invalid dates, negative balances where impossible),
– QA processes and testing pipelines before deploying changes.
If you’re a payments platform or financial data provider, processing integrity is likely essential. If you’re a general productivity tool doing “best effort” analytics, you might delay including it until your algorithms and business logic are more stable and heavily relied upon.
A word of caution: including unnecessary TSCs just to look more “impressive” complicates audits and increases work without real business benefit. Be strategic about scope.
Confidentiality
Confidentiality covers information that must be restricted to authorized parties—customer business data, proprietary models, non-public roadmaps, and confidential data your customers share with you.
Important control themes include:
– data classification (e.g., Public, Internal, Confidential),
– encryption at rest and in transit (TLS 1.2+, KMS-managed keys),
– access control and approvals for sensitive datasets,
– secure data disposal and retention policies.
Example: A B2B SaaS storing customer CRM or HR data in a multi-tenant database uses row-level access control and strong key management to protect tenant data from cross-customer exposure. This directly addresses common investor and customer questions about how you segregate tenant data.
If you store sensitive data of any kind, financial data, HR records, business intelligence, Confidentiality should likely be in your first audit scope.
Privacy
Privacy focuses on personal data (PII) and how you collect, use, retain, and disclose it. This criterion overlaps heavily with GDPR-style privacy programs and addresses data privacy requirements that regulations impose.
Typical SOC 2 Privacy elements include:
– a clear, accurate privacy notice,
– consent and preference management where required,
– data subject rights workflows (access, deletion, correction),
– secure handling of special categories of data if applicable.
Most early-stage SaaS teams handling substantial end-user PII: HR tech, healthtech, edtech should plan to include Privacy within the first 1–2 SOC 2 cycles.
SecureLeap can align SOC 2 Privacy work with existing GDPR/CCPA obligations to avoid duplicate effort for your legal and product teams.
Who Needs SOC 2 Compliance and When to Start
Any service organization storing or processing customer data in the cloud, especially B2B SaaS, managed service providers, and data platforms will eventually be asked for SOC 2. The question is when.
Typical trigger points for startups include:
– first enterprise prospect or channel partner security review,
– questions from a strategic customer’s InfoSec team,
– requests from investors during Series A/B due diligence,
– expansion into regulated sectors like healthcare or fintech.
Scenario comparisons:
High-level guidance: most SaaS teams should start SOC 2 readiness about 6–12 months before they expect large enterprise deals to close. Starting earlier is always better than scrambling when a whale account suddenly asks for your report.
SecureLeap can help you assess “Is now the right time?” Schedule a free readiness discussion before committing budget to an audit firm or automation tool.
SOC 2 vs. SOC 1 vs. SOC 3 (Choosing the Right Report)
The differences matter for procurement:
SOC 1: internal controls over financial reporting; mostly for services that directly impact customers’ financial statements.
SOC 2: controls over security, availability, processing integrity, confidentiality, and privacy; the default choice for SaaS and cloud service providers.
SOC 3: a public, high-level summary of SOC 2 without sensitive details, mainly used for marketing.
For nearly all B2B saas companies, SOC 2 is the primary report requested. SOC 1 is rarely appropriate unless you process or host financial reporting systems for your customers (like a payroll processor that directly affects their books).
Some mature companies obtain both SOC 2 and SOC 3, using SOC 3 as a website badge while sharing the detailed SOC 2 only under NDA with qualified prospects.
Quick decision aid: If you’re a SaaS startup and your prospects aren’t explicitly asking about financial reporting impact, you almost certainly need SOC 2, not SOC 1. When financial institutions ask about “SOC compliance,” they typically mean SOC 2 for security and data handling.

How SOC 2 Compliance Works: From Readiness to Audit
For founders and CTOs who’ve never navigated a compliance audit before, here’s the high-level workflow. Understanding the main stages helps you plan resources and set realistic expectations with your team.
The stages are:
- readiness assessment and scoping,
- gap remediation and control implementation,
- evidence collection and continuous monitoring
- independent audit and report issuance
- annual maintenance and improvement
The complexity depends heavily on your existing security maturity and whether you use compliance automation platforms (like Drata, Vanta, or Secureframe) versus managing evidence in spreadsheets.
SecureLeap offers bundled services: readiness, vCISO guidance, audit support, and penetration testing, so you’re not managing separate vendors and fragmented advice. One team, one point of contact, one bill.
Readiness Assessment and Scoping
A readiness assessment maps your current organization controls against SOC 2 criteria and identifies gaps in policies, tooling, and practices. This is where you figure out what work actually needs to happen before inviting an auditor.
Typical scoping decisions include:
– which product(s), environments (prod vs. staging), and regions are in scope,
– which Trust Services Criteria to include in the first report,
– which third-party services (AWS, Stripe, Auth0, cloud providers, data centers) fall under vendor risk management.
Example: A startup scopes only its primary SaaS product and production AWS account in year one, leaving legacy beta environments and internal tools out of scope. This focused approach controls audit costs while still satisfying customer requirements.
SecureLeap or a similar advisory team can run this assessment in a few weeks, providing a prioritized roadmap rather than a generic checklist that leaves you guessing what to do first.
Implementing and Maturing Controls
This is the phase where you:
– formalize policies (access control, change management, incident response, acceptable use),
– configure tools (SSO, endpoint protection, logging, backups),
– deploy processes (onboarding/offboarding, vendor reviews, risk assessment procedures).
Step-by-step guidance for founders: 1) start with identity and access management across all key systems, 2) secure your cloud environment with baseline hardening and guardrails, 3) set up centralized logging for critical services, 4) train staff on security awareness and incident reporting.
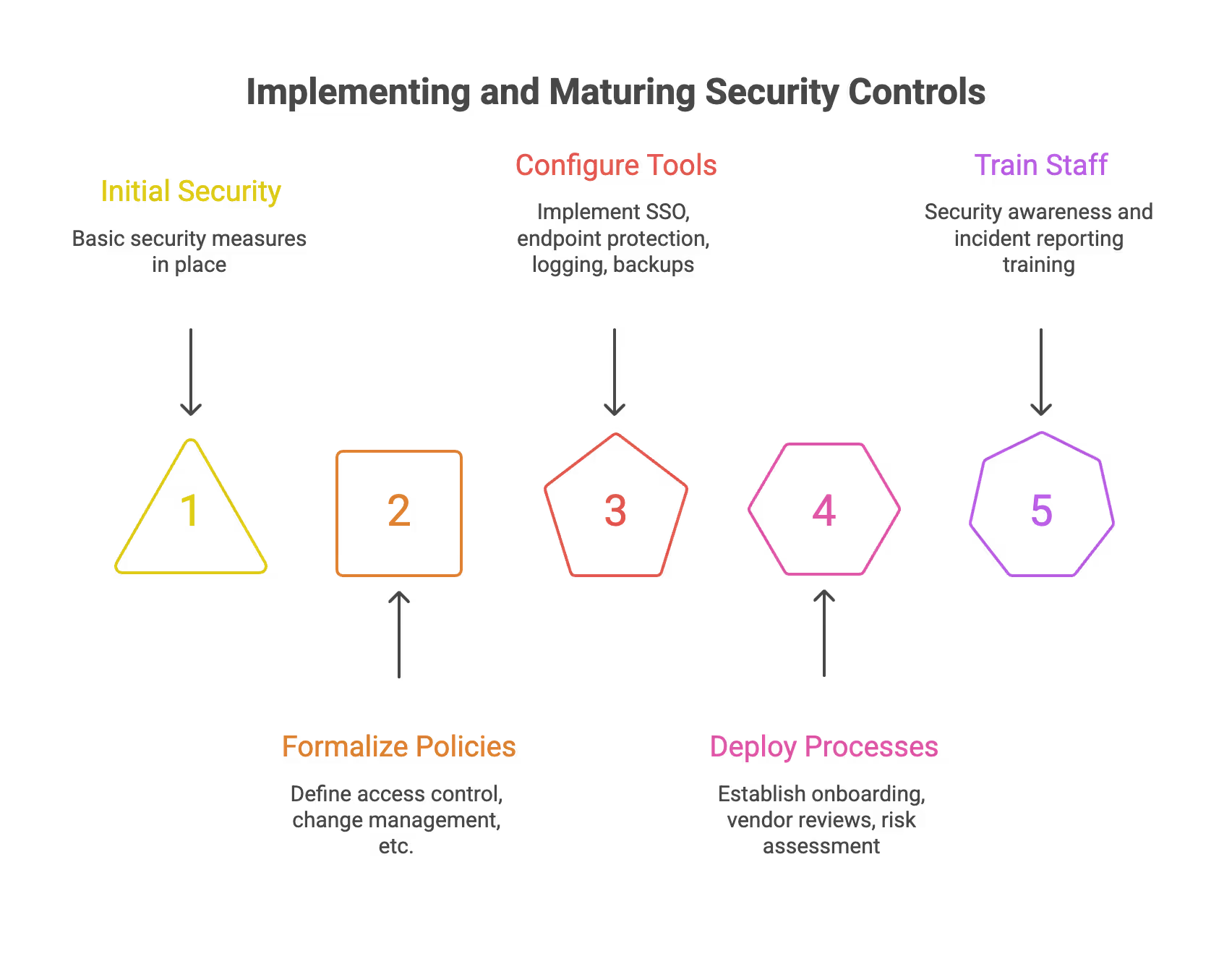
This phase typically takes 2–4 months depending on your starting point. SecureLeap can act as your vCISO function here, making pragmatic decisions that balance compliance requirements and startup velocity. We’ve seen too many startups over-engineer their controls based on enterprise playbooks that’s not necessary or helpful.
Note: healthtech or fintech startups may need additional layers for HIPAA or PCI DSS considerations. SOC 2 work can be aligned with those frameworks in parallel, sharing controls and documentation across multiple compliance programs.
Evidence Collection, Automation Tools, and Working with Auditors
Such an audit relies on evidence: screenshots, configuration exports, logs, ticket histories, training records, and policy documents. The service organization’s management is responsible for providing this evidence during fieldwork.
Compliance automation tools like Drata, Vanta, or Secureframe can:
- continuously pull evidence from systems (AWS, GitHub, Okta, Jira),
- alert you when controls drift (e.g., MFA disabled, missing endpoint agent),
- generate auditor-ready reports.
Workflow example:
– connect your cloud, identity provider, and code repositories to the platform,
– map automated tests to specific SOC 2 controls,
– use dashboards to track readiness before inviting the auditor in.
Automating compliance cuts evidence collection time by 50% or more compared to manual approaches. For resource-strapped teams, this is essential.
SecureLeap can both implement and operate these tools for you, and coordinate directly with the CPA firm during fieldwork to minimize founder distraction. Your job is building product and let us handle the evidence collection and auditor questions.
Timeframe, Costs, and How SecureLeap Can Help
Realistic timelines for a small, focused SaaS with executive buy-in:
– 2–4 months for readiness and remediation,
– 3–12 months operating period for a first Type II (depending on strategy),
– 4–8 weeks after period end for auditors to test evidence and issue the report.
Cost factors at a high level:
– auditor fees (varying by scope and firm reputation - typically $15K-$50K for early-stage companies),
– internal time investment from engineering, DevOps, and leadership,
– optional spend on consulting, vCISO support, pentesting, and automation platforms.
SecureLeap helps control overall cost and risk by: – designing a right-sized SOC 2 scope that covers customer requirements without over-scoping, – reusing controls and documentation for future frameworks (ISO 27001, HIPAA), – bundling vCISO, readiness, audit coordination, and penetration testing so startups don’t overpay for disconnected services.
Many startups come to us after getting quotes from multiple vendors and realizing the total cost (tools + consultants + auditors + pentest) adds up quickly. Our bundled approach gives you predictable pricing and a single team that understands your full picture.
FAQ Meaning SOC2 Compliance
What does SOC 2 compliance mean for SaaS companies?
SOC 2 is a security framework from the AICPA that proves a company manages customer data securely through independent CPA audits. It is considered the gold standard for technology companies selling to enterprise accounts in North America.
What is the difference between SOC 2 Type 1 and Type 2?
Type 1 tests the design of security controls at a specific point in time as a snapshot. Type 2 tests both the design and operating effectiveness of those controls over a period of 6 to 12 months.
How long does it take to become SOC 2 compliant?
Readiness and remediation usually take 2 to 4 months followed by an observation period of 3 to 12 months for Type 2 reports. Final report issuance typically requires another 4 to 8 weeks after the audit period ends.
What are the 5 Trust Services Criteria in SOC 2?
The five criteria include security, availability, processing integrity, confidentiality, and privacy. Security is the only mandatory criterion while others are selected based on your product and customer needs.
How much does a SOC 2 audit cost for a startup?
Auditor fees for early stage companies typically range from $15,000 to $50,000 depending on the scope and firm reputation. Total costs may increase with additional spend on automation platforms, penetration testing, and vCISO support.
Final Take: Get SOC 2 Certification Fast and Affordable with Secureleap
Achieving SOC 2 certification is a critical step in demonstrating your commitment to data security and winning the trust of enterprise customers. While the process can seem complex and costly, partnering with the right experts can make all the difference.
Secureleap specializes in helping organizations obtain SOC 2 certification quickly and at a very competitive price. With tailored services designed to streamline your audit process, reduce preparation time, and manage costs effectively, Secureleap ensures you get a credible, customer-trusted SOC 2 report without unnecessary delays or expenses.
Whether you're a startup or a growing mid-market company, Secureleap’s expertise and efficient approach can help you navigate the compliance journey smoothly, so you can focus on what matters most—growing your business with confidence.
Contact Secureleap today to learn how we can support your SOC 2 compliance needs and accelerate your path to certification.