Achieving SOC 2 compliance is a significant milestone for any startup. It signals to your customers, investors, and partners that you take data security seriously. However, many startups fall into the trap of thinking SOC 2 is entirely about internal security, locking down laptops, encrypting databases, and training employees.
SOC 2 vendor management also requires aligning internal controls with external vendor oversight to ensure comprehensive risk mitigation.
While those are critical, there is a massive external component that often trips up founders and CTOs: Vendor Management.
In the eyes of a SOC 2 auditor (and your customers), your security posture is only as strong as your weakest link. If you share customer data with a third-party vendor, and that vendor gets breached, you are responsible.
This article will guide you through the requirements of SOC 2 vendor management, specifically tailored for the resource-constrained, fast-moving reality of a startup.
What is SOC 2 Vendor Management?
At its core, SOC 2 vendor management is the set of processes you use to vet, monitor, and manage the third-party services your company relies on. These third party vendors can introduce significant risks if not properly managed under SOC 2 requirements.
In the official language of the AICPA (the body that governs SOC 2), this falls primarily under Common Criteria 9.2 (CC9.2), which states:
“The entity assesses and manages risks associated with vendors and business partners.”
This doesn’t mean you need to micromanage every subscription tool you use. It means you need a system to:
- Know who your vendors are.
- Understand the risks they pose to your data.
- Verify that they are secure before you hire them.
- Check in on them regularly to ensure they stay secure.
Why This Matters for Startups
For a startup, vendor management isn’t just about passing an audit. It’s about survival and growth.
- Risk Reduction: Startups rely heavily on SaaS tools (AWS, Slack, GitHub, HR platforms). A breach in one of these can cascade into your environment.
- Sales Enablement: Your enterprise customers will send you security questionnaires. They will ask, “How do you assess your sub-processors?” Having a robust vendor management program allows you to answer confidently and close deals faster.
- Operational Maturity: It forces you to track what tools you are actually paying for, often uncovering unused subscriptions and saving money. Effective vendor management leads to direct cost savings by streamlining processes, reducing unnecessary expenses, and improving overall profitability.
The SOC 2 Vendor Management Lifecycle
Effective vendor management is not a one-time checklist; it is a lifecycle. To satisfy SOC 2 requirements without slowing down your operations, follow this six-step framework.
A vendor management system can help automate and streamline each phase of the SOC 2 vendor management lifecycle by centralizing vendor interactions, data management, performance tracking, risk assessment, communication, and reporting.
Phase 1: Inventory and Identification
You cannot secure what you don’t know you have. The first step is creating a “Source of Truth” for every third-party vendor your company uses.
How to do it:
- Poll your team: Ask department heads (Engineering, Marketing, HR, Sales) what tools they use.
- Check the money: Review bank statements and corporate credit card transactions for recurring SaaS payments.
- SSO Logs: If you use Google Workspace or Okta, check which applications employees are logging into.
What to capture in your inventory:
- Vendor Name
- Service Provided (e.g., Cloud Hosting, CRM, Payroll)
- Data Types Accessed (e.g., PII, PHI, Internal Code, Public Data)
- Business Owner (The internal employee responsible for this relationship)
- Centralized vendor data: Maintain a single, reliable source of vendor data to enable effective tracking, risk assessment, and informed decision-making.
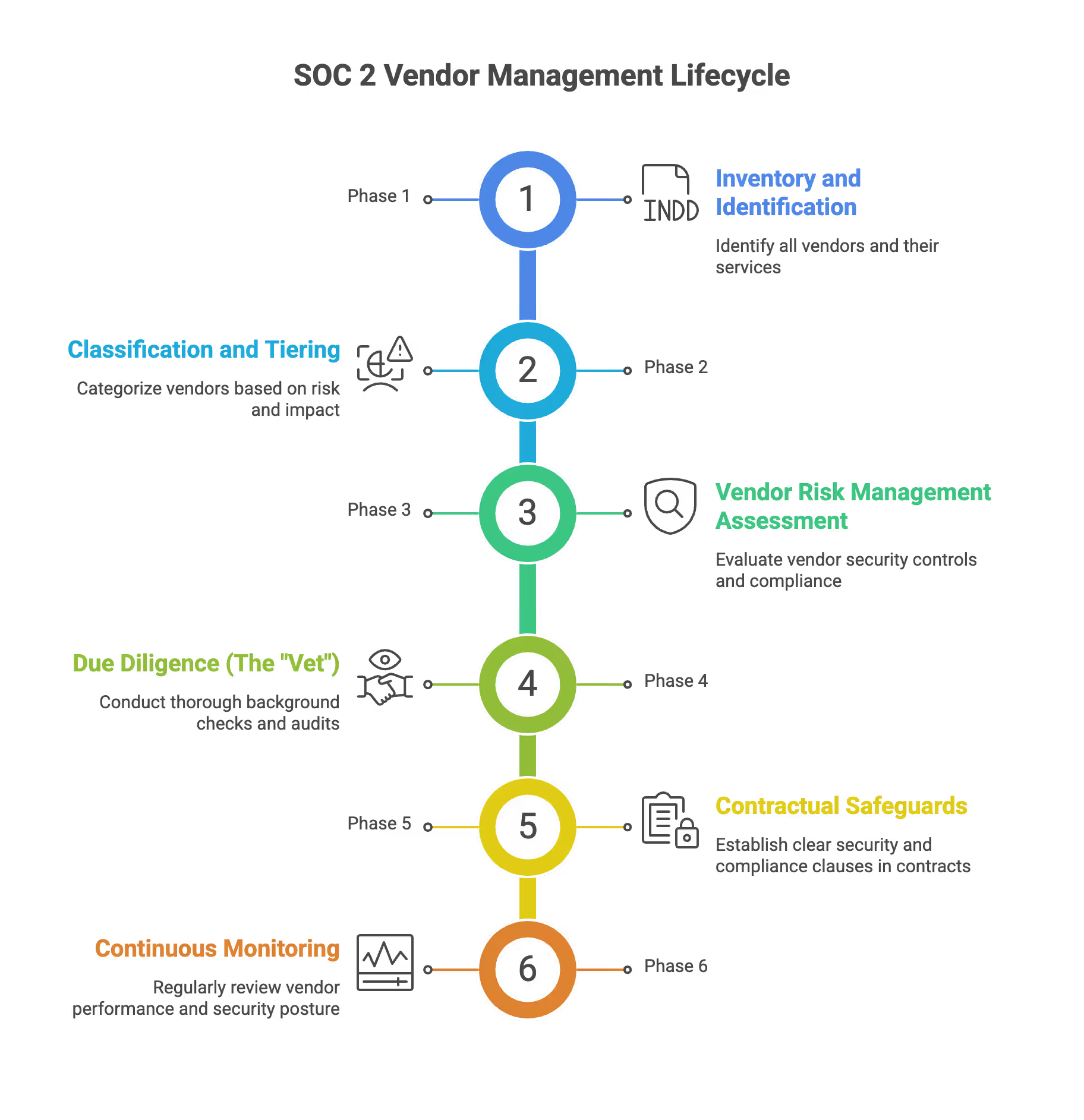
Phase 2: Classification and Tiering
Not all vendors are created equal. Your lunch delivery service does not require the same level of scrutiny as your cloud hosting provider. To save time, you should categorize vendors based on risk.
Suggested Tiers:
Critical Risk (High):
- Vendors that store, process, or transmit sensitive customer data (PII/PHI).
- Vendors that provide critical infrastructure (if they go down, you go down).
- Examples: AWS/GCP/Azure, payment processors, production database providers.
Moderate Risk (Medium):
- Vendors with access to internal company data but not sensitive customer data.
- Vendors whose failure would be annoying but not catastrophic.
- Examples: Project management tools, internal wikis, marketing analytics tools.
Low Risk:
- Vendors with no access to data or systems.
- Examples: Office cleaning services, catering, social media schedulers.
Startup Tip: Focus 80% of your energy on the Critical vendors. These are your key vendors for SOC 2 compliance and vendor risk management, as they have the greatest impact on your security and compliance posture. Auditors will look at this list most closely.
Phase 3: Vendor Risk Management Assessment
Once you have identified your critical vendors, you must formally assess the risks they pose. These are known as vendor risk assessments, which are essential for identifying vulnerabilities and ensuring compliance. This is often where startups get stuck, overthinking the process. It doesn’t need to be a complex mathematical model.
Simple Risk Assessment Workflow:
- Identify the Threat: What could go wrong? (e.g., Data breach, service outage, compliance violation).
- Determine Impact: If it goes wrong, how bad is it? (High/Medium/Low).
- Determine Likelihood: How likely is it to happen? (High/Medium/Low).
- Mitigation: What controls mitigate this? (e.g., “Vendor is SOC 2 compliant,” “We have offline backups”).
Example Entry:
- Vendor: Cloud Hosting Provider
- Risk: Availability failure (Server goes down).
- Impact: High (Product is unusable).
- Mitigation: Vendor guarantees 99.99% uptime in SLA; we deploy across multiple availability zones.
- Residual Risk: Low.
Phase 4: Due Diligence (The "Vet")
Before you sign a contract (or immediately, if you are backfilling for existing vendors), you must verify the vendor’s security posture. Robust due diligence processes are essential for reviewing SOC 2 reports and managing vendor risk, ensuring that you thoroughly assess report validity, scope, and address any deficiencies to maintain compliance.
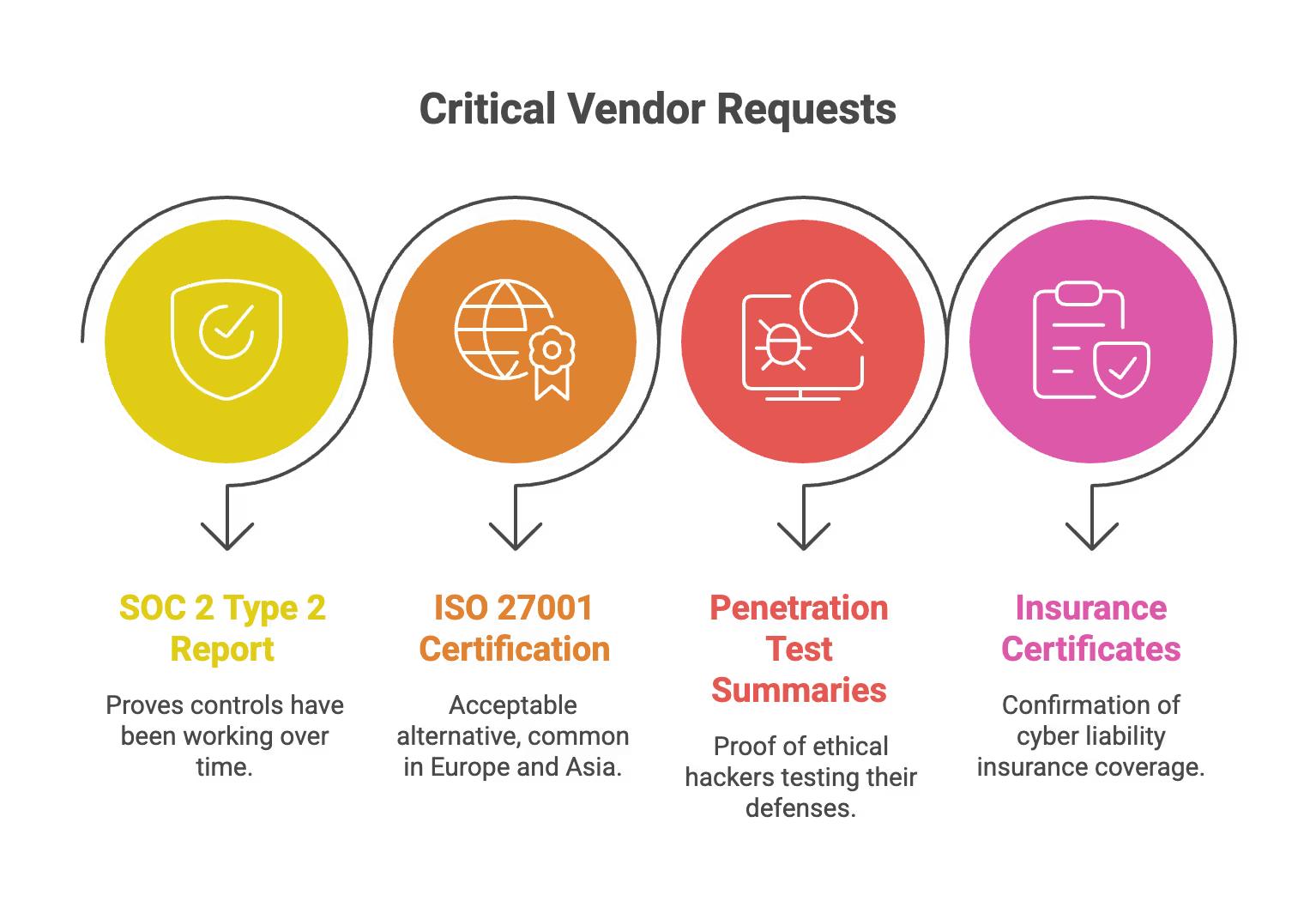
What to request from Critical Vendors:
- SOC 2 Type 2 Report: This is the gold standard. A Type 2 report proves their controls have been working over a period of time (usually 6-12 months).
- ISO 27001 Certification: An acceptable alternative to SOC 2, common in Europe and Asia.
- Penetration Test Summaries: Proof that they hire ethical hackers to test their defenses.
- Insurance Certificates: Do they have cyber liability insurance?
What to do if they don’t have a SOC 2 Report:
If a critical vendor is a small startup that doesn’t have SOC 2 yet, you can’t just ignore it. You must conduct a Security Questionnaire. Thorough diligence processes, such as security questionnaires and follow-up reviews, are critical for ensuring compliance and operational integrity when formal reports are unavailable.
- Ask them to fill out a standard questionnaire (like the CAIQ-Lite or VSA).
- Review their answers for red flags (e.g., no multi-factor authentication, no data encryption).
- Document your acceptance of the risk (e.g., “Vendor is pre-SOC 2 but has strong encryption and is critical for our roadmap. We accept this risk for 12 months.”).
Phase 5: Contractual Safeguards
When onboarding a new vendor, your contract (or Terms of Service) should include specific security clauses. If you are using a giant vendor like Amazon or Google, you are stuck with their standard terms (which are usually fine). For smaller B2B vendors, ensure the contract covers:
- Right to Audit: Can you request their security docs?
- Breach Notification: They must tell you within a specific timeframe (e.g., 24 or 72 hours) if your data is compromised.
- Data Deletion: They must delete your data when you cancel the service.
- Confidentiality/NDAs: Standard protection for your trade secrets.
- Review Service Level Agreements (SLAs): SLAs should clearly define performance standards such as uptime, defect rates, and remedies if service levels are not met. Incorporate these SLAs into your contract to set expectations and ensure accountability.
Phase 6: Continuous Monitoring
This is the “Management” part of Vendor Management. You cannot just vet a vendor once and forget them for five years. SOC 2 requires ongoing monitoring. Continuous risk monitoring is essential to proactively identify and address vendor-related risks, ensuring that any changes in a vendor’s security posture are detected and managed in real time.
Annual Review Checklist:
- Request the new SOC 2 report: SOC 2 reports expire every 12 months. You need the current one.
- Review the “Bridge Letter”: If the report period ended 3 months ago, a bridge letter certifies that nothing bad has happened in the gap.
- Review SLAs: Did they meet their uptime guarantees?
- Check for incidents: Did they have any public security breaches in the news?
Vendor Relationships: Building Trust Beyond Compliance
While meeting regulatory requirements is essential, the most effective vendor management process goes further, focusing on building genuine, trust-based vendor relationships. For startups, this means treating vendors not just as service providers, but as strategic business partners who play a critical role in your growth and success.
Strong vendor relationships are built on transparency and open communication. By sharing your business goals, upcoming projects, and expectations, you enable vendors to better support your needs and proactively address potential risks. Regular check-ins and honest feedback sessions help both sides stay aligned, resolve issues quickly, and adapt to changing requirements.
Deep Dive: How to Review a Vendor's SOC 2 Report
A common mistake startups make is requesting a vendor’s SOC 2 report, saving the PDF in a folder, and never opening it. Auditors will catch this. You need to prove you reviewed it. A thorough review should cover the Trust Services Criteria, including security, availability, processing integrity, confidentiality, and privacy.
The 15-Minute Review Strategy:
- Check the Opinion (Section I): Look for the auditor’s opinion letter. You want to see “Unqualified Opinion” (this is good—it means ‘without reservation’). If it says “Qualified Opinion,” they failed something major.
- Check the Scope: Does the report cover the actual service you are buying? (e.g., If you bought their “Cloud Product,” but the SOC 2 report is only for their “Consulting Services,” it’s useless).
- Read “Section IV” (Exceptions): Scan the table of controls. Look for any items where the auditor noted an “Exception.”
- Example: “The auditor found that 2 out of 10 new hires did not complete background checks.”
- Your Job: Decide if this exception puts your data at risk. If it’s minor, document that you reviewed it and it’s acceptable.
- Review access controls as documented in the SOC 2 report to ensure technical safeguards are in place to protect sensitive data and mitigate risks of unauthorized access.
- CUECs (Complementary User Entity Controls): This is vital. The report will have a section listing things you (the User) must do to keep the system secure.
- Example: The vendor encrypts data, but you are responsible for managing your user passwords.
- Action: You must map these controls to your own internal security policies.
- Evaluate processing integrity to ensure the vendor’s systems maintain data accuracy, completeness, and reliability, especially if you handle sensitive or regulated information.
Best Practices for Startups
Startups do not have dedicated “Vendor Risk Managers.” Here is how to handle this workload efficiently. Vendor management software can help automate onboarding, performance tracking, and compliance tasks, making the process more streamlined and manageable for growing teams.
1. Centralize Your "Vendor Trust" Folder
Create a dedicated Google Drive or SharePoint folder structure:
- /Vendor Management- /Active Vendors
- /Vendor A -> (Contracts, SOC 2 Report 2024, Risk Assessment)
- /Vendor B
- /Terminated Vendors
Centralizing documentation in this way supports transparent and efficient vendor interactions by making all records, communications, and key documents easily accessible and organized for your team.
2. Use the "Gatekeeper" Method
Empower your Finance or Operations lead to act as a gatekeeper. No new software purchase gets approved until the “Business Owner” submits a basic vendor intake form that answers: “Is this critical?” and “Does it hold customer data?” This method streamlines vendor onboarding by ensuring all necessary documentation, system setup, and compliance checks are completed from the start.
3. Automate with Compliance Tools
Use a compliance automation platform (like Drata, Vanta, Secureframe, or Sprinto). These tools can:
- Import your vendor list from your accounting software.
- Send automated emails to vendors requesting their security certificates.
- Read the documents and flag issues automatically.
- Remind you when a review is due.
Adopting a software solution for SOC 2 vendor management increases efficiency and reduces manual errors by systemizing and automating key processes.
4. Leverage "Trust Centers"
Many modern SaaS companies have public “Trust Centers” (e.g., trust.vendorname.com) where you can download their SOC 2 reports automatically after signing a digital NDA. This is much faster than emailing support. Additionally, the entity obtains privacy commitments by requiring vendors to agree to privacy terms before accessing sensitive documentation.
Vendor Management Common Pitfalls to Avoid
Even well-intentioned startups make mistakes that lead to audit exceptions. These mistakes can jeopardize regulatory compliance and increase risk exposure. Watch out for these traps:
The "Scope Creep" Trap
The Mistake: Listing every single vendor in your critical risk register, including your coffee supplier and Spotify subscription.
The Fix: Be ruthless with your scoping. Only include vendors that impact the Security, Availability, or Confidentiality of your customer data. Focus on vendors that influence your core business processes, especially those whose services affect your operational workflows or critical business functions. If a vendor has no access to production systems or data, they are likely out of scope for strict monitoring.
The "Paper Tiger" Review
The Mistake: Collecting SOC 2 reports but having no evidence that anyone looked at them.
The Fix: Create a simple “Vendor Review Memo” or a spreadsheet column where you type: “Reviewed on [Date] by [Name]. Report was Unqualified. No relevant exceptions found. CUECs noted and implemented.” This documentation helps demonstrate fulfillment of compliance requirements during audits.
The "Sub-Processor" Blind Spot
The Mistake: Forgetting that your vendors have vendors too (4th parties).
The Fix: Your critical vendors (like AWS or a payment gateway) are required to manage their own underlying vendors. When you review their SOC 2 report, check that they have a control for “Vendor Management.” This is a key aspect of third party risk management, ensuring that risks are managed throughout the supply chain. If they do, you generally don’t need to vet their vendors personally.
The "Set It and Forget It"
The Mistake: Doing a great job onboarding a vendor in 2022, but having zero documentation for 2023, 2024, or 2025.
The Fix: Set a recurring calendar invite or Jira ticket for “Annual Vendor Security Review.” Risk teams can use automated reminders and collaborative workflows to ensure timely reviews and consistent documentation. Do it at the same time every year so it becomes a habit.
Missing the "Offboarding" Step
The Mistake: Canceling a subscription but forgetting to ensure data was deleted or access tokens were revoked.
The Fix: Include a “Vendor Offboarding” checklist in your procedures. Robust supplier management practices ensure secure and compliant offboarding of vendors.
- Contract terminated.
- Data export requested (if needed).
- Written confirmation of data destruction obtained.
- SSO/API access revoked.
How SecureLeap Supports Your SOC 2 Audit Journey
SecureLeap focuses specifically on seed to Series B technology startups and SMB SaaS companies that need SOC 2 compliance, often for the first time, and lack a full time security leader.
Core Services
SecureLeap provides practical support across the entire SOC 2 journey:
- SOC 2 readiness assessments to identify gaps and create remediation roadmaps
- Control design and implementation tailored to cloud native startups
- Virtual CISO leadership for ongoing security guidance without full time headcount
- Policy drafting that reflects how your team actually operates
- Evidence management and coordination with CPA audit firms
- Risk assessment and risk management program development
Compliance Automation Integration
SecureLeap helps implement and manage compliance automation platforms like Drata, Vanta, and Secureframe. Integration with your existing cloud stack (AWS, Azure, GCP, GitHub, GitLab) enables automated evidence collection and operational effectiveness monitoring throughout your audit period.
Bundled Solutions
Enterprise customers often require both a SOC 2 report and an annual application or API penetration test. SecureLeap bundles these services together, handling both your compliance preparation and your technical security validation in a coordinated engagement.
Getting Started
SecureLeap offers free SOC 2 audit readiness consultations for startup CEOs and CTOs. During this call, you will receive:
- Custom timeline based on your deal deadlines
- Recommended Trust Services Criteria for your market
- Scope recommendations based on your infrastructure
- Estimated budget range for your specific situation
Schedule your consultation to validate your assumptions about scope and avoid over engineering controls that do not match your actual risk profile or customer requirements.
FAQ SOC 2 Vendor Management
What is SOC 2 Vendor Management?
It is the set of processes used to vet, monitor, and manage third-party services to comply with AICPA Common Criteria 9.2. This system ensures you understand and mitigate the risks external vendors pose to your data.
Why is vendor management critical for startups?
It prevents security breaches from third-party tools and helps you pass enterprise security questionnaires to close sales deals. Additionally, it improves operational maturity by identifying unused subscriptions and saving money.
What are the steps in the SOC 2 vendor management lifecycle?
The lifecycle consists of six phases: inventory, classification, risk assessment, due diligence, contractual safeguards, and continuous monitoring. Following this framework ensures compliance without slowing down startup operations.
How should I handle a vendor without a SOC 2 report?
If a critical vendor lacks a SOC 2 report, you must conduct a security questionnaire using standards like CAIQ-Lite or VSA. Review their answers for red flags and document your acceptance of the risk.
How often do I need to review my vendors?
SOC 2 requires continuous monitoring, which includes formally reviewing vendor SOC 2 reports annually as they expire. You should also check SLAs and bridge letters during this annual review process.
What is the difference between Critical and Low risk vendors?
Critical vendors store sensitive customer data or provide essential infrastructure that impacts your uptime. Low risk vendors, like cleaning services or social media schedulers, have no access to production systems or data.


%20(10)%20(1).avif)

%20(4)%20(1).avif)
%20(3)%20(1).avif)