In short, Cloud Penetration Testing involves an authorized, simulated cyberattack on your cloud infrastructure. It demands specialized expertise in cloud environments, configurations, and the distinct shared responsibility models inherent to cloud platforms.
You are building something incredible. Whether it is a SaaS platform disrupting the fintech space or a new healthcare app powered by AI, you are moving fast. In the startup world, the mantra used to be “move fast and break things.” However, in today’s digital landscape, if you break your security, you might break your company.
As you migrate to or build natively on the cloud, you likely assume that because you are using giants like AWS, Azure, or Google Cloud, you are automatically secure. This is not always right.
These are examples of major cloud providers, and while the cloud service provider is responsible for securing the underlying infrastructure, you are responsible for securing your own deployments, configurations, and data. This is one of the most dangerous misconceptions in the tech industry.
This guide is designed for founders, CTOs, and decision-makers who need to understand Cloud Penetration Testing without getting bogged down in jargon. We will explore what it is, why your startup’s survival might depend on it, and how to navigate the specific ecosystems of AWS, Azure, and GCP. Understanding the shared responsibility model is crucial when using cloud services and cloud systems, as it defines the division of security responsibilities between you and your cloud provider.
Part 1: What is Cloud Penetration Testing?
To understand Cloud Penetration Testing, we first need to look at what it is not. It is not an automated scan that runs in five minutes. It is not simply checking a box for compliance.
Cloud Penetration Testing is an authorized, simulated cyberattack against your cloud infrastructure. Cloud penetration testing requires specialized knowledge of cloud environments, configurations, and the unique shared responsibility models of cloud platforms.
Ethical hackers, often called “white hat” hackers, are penetration testers with expertise in cloud security who attempt to breach your defenses just like a malicious actor would. Their goal is to find holes in your security bucket before the bad guys do.
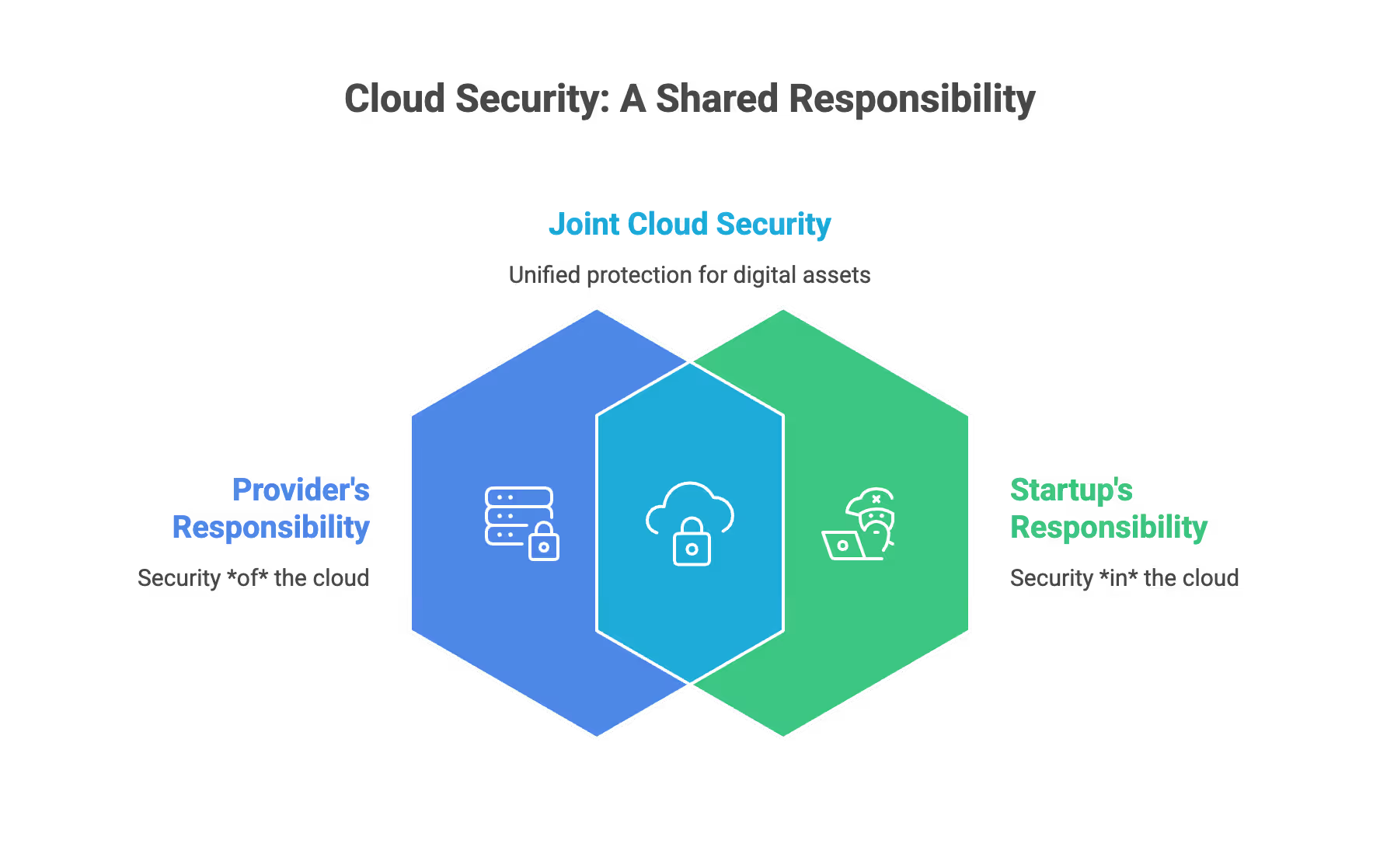
The "Shared Responsibility" Model
The most important concept you must grasp as a startup founder is the Shared Responsibility Model.
- The Provider’s Job (AWS/Azure/GCP): They are responsible for the security of the cloud. They protect the physical data centers, the cabling, the cooling, and the underlying hardware.
- Your Job (The Startup): You are responsible for security in the cloud. This includes your customer data, your applications, your operating systems, your encryption settings, and your passwords.
If you leave a digital door unlocked in your AWS account, Amazon is not responsible for the burglary. Cloud Penetration Testing focuses entirely on your side of this responsibility.
Vulnerability Scanning vs. Penetration Testing
Startups often confuse these two, but knowing the difference is vital for your budget and your security posture.
- Vulnerability Scanning:
- Automated scanning is a preliminary step in security testing, using automated software to look for known issues.
- Like a security guard walking around checking if windows are closed.
- Cheap and fast, but shallow.
- Prone to “false positives” (reporting errors that aren’t real).
Vulnerability assessment and vulnerability analysis are important for identifying known issues in your cloud environment, but may not uncover deeper security weaknesses that require more advanced testing.
- Penetration Testing:
- Human-led intelligence combined with tools.
- Like hiring a master thief to try and break into your house using any means necessary.
- They attempt to “exploit” the vulnerabilities to see how deep they can get.
- Penetration testing goes beyond basic vulnerability testing by simulating real-world attack scenarios to uncover hidden risks.
- Provides a verified, realistic picture of your risk.
Part 2: Why Startups Specifically Need Cloud Pentesting
You might think, “We are too small to be a target.” Unfortunately, automated bots do not care about company size. They scan the entire internet looking for easy targets. Cloud pen testing tools enable startups to simulate real-world attack scenarios, identify vulnerabilities, and improve their overall security posture. Furthermore, startups have specific pressures that make pentesting essential, especially when it comes to protecting critical assets and ensuring the security of their most critical assets through regular security assessments.
1. Building Trust with Enterprise Clients
If you are selling B2B (Business to Business), your large enterprise clients will send you a Vendor Risk Assessment. They will demand to see a recent penetration test report.
- It proves you take their data seriously.
- It shortens the sales cycle.
- It differentiates you from riskier competitors.
2. Regulatory Compliance and Frameworks
As you grow, you will likely need to adhere to security frameworks. Most of these explicitly require or strongly suggest penetration testing.
- SOC 2: The gold standard for SaaS startups.
- ISO 27001: International standard for information security.
- HIPAA: Mandatory if you handle healthcare data.
- PCI-DSS: Mandatory if you process credit card payments.
3. Protecting Intellectual Property
Your code, your algorithms, and your user base are your most valuable assets. A breach can lead to:
- Competitors stealing your logic.
- Ransomware locking you out of your own product.
- Data leaks that ruin your reputation before you even scale.
4. Preventing "Cloud Bill Shock" Attacks
Hackers often do not want your data; they want your computing power.
- Attackers compromise a cloud account.
- They spin up thousands of servers to mine cryptocurrency.
- You wake up to a $50,000 bill from AWS or Azure.
- A penetration test can identify weak access points that allow this to happen

Part 3: Navigating the Platforms (AWS, Azure, GCP)
Every cloud provider has different architectures, services, and security quirks. A generic approach does not work. Your pentest team must specialize in the platform you use. It is crucial to understand the list of permitted services for penetration testing as defined by each cloud provider, such as AWS and Azure, to ensure all testing activities are authorized and compliant with their rules of engagement. The ultimate goal is securing cloud infrastructure by leveraging specialized testing approaches tailored to each environment.
AWS (Amazon Web Services)
AWS is the market leader, and consequently, the most targeted. The complexity of AWS IAM (Identity and Access Management) is the number one source of vulnerabilities for startups.
Key Focus Areas for AWS Pentesting:
S3 Bucket Permissions:
- Are your storage buckets public?
- Can an anonymous user read your private database backups?
- Testers look for “open” buckets that leak user data.
IAM Privilege Escalation:
- Does a junior developer have rights to delete the production database?
- Can a compromised low-level service account grant itself Administrator privileges?
- AWS has thousands of permissions; getting this right is difficult without testing.
Security Groups:
- These are your virtual firewalls.
- Testers check if sensitive ports (like SSH or RDP) are open to the entire internet (0.0.0.0/0).
- Scanning container images stored in Amazon ECR is critical to detect known vulnerabilities and software flaws in containerized applications before deployment.
Lambda and Serverless:
- Startups love Serverless.
- Testers check for code injection flaws within the functions themselves, and tools like Amazon Inspector can automatically detect and analyze security issues within AWS Lambda functions as part of a comprehensive vulnerability assessment.
Microsoft Azure
Azure is heavily integrated with the Microsoft ecosystem. If your startup uses Office 365, you are likely using Azure Active Directory (now Entra ID), which becomes the central nervous system of your security. Penetration testing in Azure environments is essential for identifying security issues and strengthening your security systems, ensuring vulnerabilities are found and mitigated before attackers can exploit them.
Key Focus Areas for Azure Pentesting:
Entra ID (Active Directory) Misconfigurations:
- This is the most critical attack surface in Azure.
- Testers look for weak password policies and lack of Multi-Factor Authentication (MFA).
- They check for “Guest” users who have been granted too much access to internal documents.
Blob Storage:
- Similar to AWS S3, Azure Blobs can be misconfigured to allow public access.
- Testers verify that your private files are actually private.
Automation Accounts:
- Azure uses “Runbooks” to automate tasks.
- These often contain hard-coded credentials that attackers can steal.
Azure Logic Apps:
- Testers examine the workflows to see if they can manipulate the logic to bypass authentication or steal data.
Google Cloud Platform (GCP)
GCP is popular among startups for its Kubernetes (GKE) integration and data analytics capabilities. The security model here relies heavily on Service Accounts.
Key Focus Areas for GCP Pentesting:
Kubernetes (GKE) Security:
- GCP is the home of Kubernetes.
- Testers look for container breakouts (escaping the container to access the host server).
- They check for misconfigured cluster permissions (RBAC).
- Assessing cloud workloads and containerized workloads is critical, as these are common in GCP environments and can introduce unique security risks if not properly managed.
Service Account Keys:
- GCP uses JSON key files for authentication.
- Developers often accidentally upload these keys to GitHub.
- Testers scour code repositories to find leaked keys that give them access to your cloud.
IAM Roles at the Project Level:
- GCP organizes resources into Projects.
- Testers check if a user has “Editor” or “Owner” rights on a project when they only need “Viewer.”
Compute Engine Metadata:
- Testers attempt to query the internal metadata server to steal access tokens from running virtual machines.
The key features of GCP that make it a popular choice for startups include robust support for containerized workloads and cloud-native applications, enabling scalable and flexible cloud workloads.

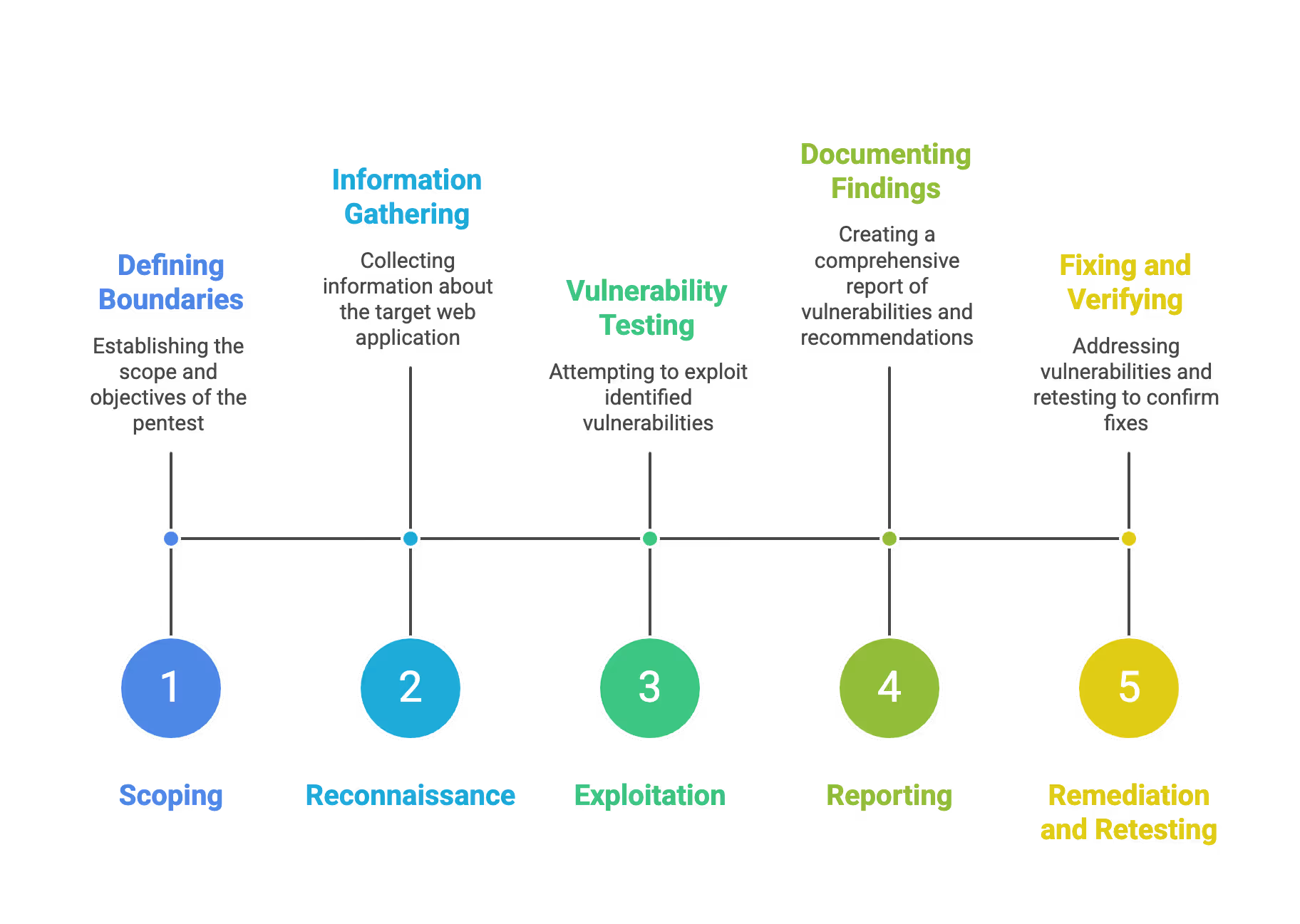
Part 4: The Pentesting Process (What to Expect)
When you hire a firm to conduct a cloud penetration test, it usually follows a structured methodology. This process enables organizations to perform security testing in a systematic and effective manner, identifying vulnerabilities specific to cloud environments. Throughout the engagement, external testers work closely with your internal security team, ensuring collaboration that enhances your overall cybersecurity posture. Understanding this helps you manage the engagement.
Phase 1: Scoping
This is the planning phase. You and the vendor define the rules of engagement.
- White Box: You give the testers full information (diagrams, accounts, documentation).
- Black Box: You give them nothing. They simulate a total outsider. This is more expensive and often yields fewer results in a short timeframe.
- Grey Box: A mix of both (usually provided with user credentials but no architecture diagrams). This is highly recommended for startups as it provides the most value for money.
Phase 2: Reconnaissance
The testers gather intelligence.
- They look for subdomains belonging to your startup.
- They search for leaked passwords or API keys on the public web.
- They map out your cloud infrastructure.
Phase 3: Exploitation
This is the "hacking" phase.
- They attempt to use the vulnerabilities found to gain access.
- They try to pivot (move from one compromised system to another).
- They try to exfiltrate (steal) dummy data to prove it is possible.
Phase 4: Reporting
The most important deliverable.
- You receive a PDF report.
- It should contain an Executive Summary (for you and investors).
- It should contain Technical Findings (for your developers).
- Each finding is ranked: Critical, High, Medium, Low, Informational.
Phase 5: Remediation and Retesting
- Your team fixes the issues.
- Crucial Step: You ask the vendor to perform a "Retest" to verify the fixes actually work.
Cloud Penetration Testing Tools
Cloud penetration testing tools are essential for security professionals aiming to identify and address security vulnerabilities in cloud environments. These tools are designed to simulate real-world attack scenarios, allowing you to uncover weaknesses in your cloud security posture before malicious actors do. There are several categories of testing tools, including vulnerability scanners, penetration testing frameworks, and cloud-specific security assessment platforms.
Popular cloud penetration testing tools include AWS Inspector for Amazon Web Services, Azure Security Center for Microsoft Azure, and Google Cloud Security Scanner for Google Cloud environments. Third-party tools like Nessus, Metasploit, and Burp Suite are also widely used to perform comprehensive testing across different cloud platforms.
By leveraging these tools, security professionals can conduct thorough vulnerability assessments, test for exploitable vulnerabilities, and gain actionable insights into the security of your cloud assets. Incorporating these tools into your security testing process ensures that your cloud defenses are robust, up-to-date, and capable of withstanding real world attack scenarios.
Part 5: Best Practices for Startups
To get the most out of your cloud penetration test, follow these best practices. As startups and growing businesses rapidly adopt new technologies in the cloud, they often encounter new security challenges that require updated testing approaches and best practices.
1. Adopt a "Grey Box" Approach
As a startup, you do not have unlimited budget. Do not waste the tester’s time making them guess your IP addresses. Give them the documentation and test accounts. This allows them to spend their time finding deep logic flaws rather than just scanning the perimeter.
2. Test Your APIs
Modern startups are API-driven. Ensure your penetration test specifically covers your APIs.
- Check for Broken Object Level Authorization (BOLA).
- Ensure one user cannot access another user's data just by changing an ID number in the URL.
3. Separate Production and Staging
Ideally, perform the penetration test on a Staging environment that is an exact replica of Production.
- This prevents accidental downtime during the test.
- It allows testers to be more aggressive without fear of breaking the customer experience.
- If you must test Production, schedule high-risk tests during off-peak hours.
4. Fix High and Critical Issues First
You will likely get a report with many findings. Do not panic.
- Prioritize "Critical" and "High" severity issues immediately.
- Create a roadmap for Medium issues.
- Accept the risk for Low issues if they do not impact core business logic.
5. Implement Infrastructure as Code (IaC) Scanning
Before the human pentest, use tools to scan your Terraform or CloudFormation scripts.
- Catch misconfigurations before they are even deployed.
- This makes the human pentest more efficient as they won't have to report basic errors.
6. Do Not Forget Third-Party Integrations
Your cloud connects to Slack, Jira, GitHub, and payment gateways.
- Ensure the scope includes how these integrations are secured.
- Review the permissions you grant to third-party apps.
Part 6: Common Pitfalls to Avoid
Founders often make avoidable mistakes when procuring or managing a pentest.
1. "Scope Creep" vs. "Scope Gap"
- Scope Creep: Adding too many assets to the test without increasing budget, leading to a rushed and shallow test.
- Scope Gap: Excluding critical systems (like your database) to save money, leaving a massive blind spot.
- Advice: Define the "Crown Jewels" (your most critical data) and ensure the scope focuses heavily on protecting them.
2. Relying Solely on Automated Reports
Some cheap vendors will run a scanner and put their logo on the output.
- The Sign: The report is hundreds of pages long but contains generic text.
- The Fix: Ask for a "Proof of Concept" (PoC) for the vulnerabilities. A human tester will explain how they exploited the flaw.
3. Testing Only Once
Security is a movie, not a photograph.
- Startups release code daily or weekly.
- A pentest from six months ago is obsolete today.
- Advice: Schedule a pentest annually, or after every major product release.
4. Ignoring the "Internal" Threat
Founders focus on external hackers. However, a compromised employee laptop is a major threat.
- Ensure the pentest includes a scenario where the attacker has "User" level access.
- This simulates a phishing attack or a rogue employee.
5. Leaving "Backdoors" Open After Testing
During the test, you might whitelist the tester’s IP address or create specific admin accounts for them.
- The Danger: Forgetting to remove these permissions after the test ends.
- The Fix: Have a strict offboarding process immediately after the final report is delivered.
Part 8: Conclusion
Cloud Penetration Testing is not just a checkbox for compliance; it is a fundamental hygiene practice for any modern startup. It bridges the gap between the security Amazon or Google provides and the security your application requires.
By identifying weak IAM roles in AWS, unblocked ports in Azure, or leaked keys in GCP, you are doing more than fixing bugs. You are protecting your reputation, your customer's trust, and your company's future.
Start small. Define your scope. Hire reputable professionals. And remember: In the cloud, you are only as secure as your configuration.
Take the proactive step today. Secure your cloud, so you can go back to doing what you do best: building the future.
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.
FAQ Cloud Penetration Test
What is cloud penetration testing?
Cloud penetration testing is an authorized and simulated cyberattack against your cloud infrastructure. It identifies security holes in your deployments and configurations before malicious actors can exploit them.
How does pentesting differ from vulnerability scanning?
Scanning is an automated and shallow check for known issues using software tools. Penetration testing is a human-led assessment that attempts to exploit vulnerabilities to provide a realistic picture of risk.
Why do startups need cloud penetration testing?
It is essential for passing vendor risk assessments and meeting compliance standards like SOC 2 or HIPAA. Testing also protects intellectual property and prevents attackers from racking up thousands of dollars in compute costs.
What is the shared responsibility model in cloud security?
Providers like AWS or Azure secure the physical infrastructure while you are responsible for everything inside the cloud. This includes your data, application code, user permissions, and encryption settings.
What is a grey box penetration test?
In a grey box test, the startup provides testers with some information like user credentials or documentation. This approach is efficient because it allows experts to find deep logic flaws quickly.
How often should a startup perform a penetration test?
You should schedule a penetration test at least annually or after every major product release. Regular testing is vital because a test from six months ago becomes obsolete as you release new code.


%20(16)%20(1).avif)

%20(13)%20(1).avif)
%20(7)%20(1).avif)