Building a startup is an exercise in controlled chaos. You are moving fast, iterating on products, and chasing product-market fit. In this environment, security often feels like a roadblock, something that slows down your deployment pipeline.
However, the reality of the modern digital landscape is unforgiving. A single data breach can destroy the trust you have built with early adopters, derail your next funding round, or result in crippling regulatory fines.
Most web applications are internet facing, making them especially vulnerable to remote attacks and increasing the need for robust security testing.
This guide effectively demystifies Web Application Penetration Testing. It explains what it is, why it is critical for your survival, and how to navigate the process without needing a PhD in cybersecurity.
What is Web Application Penetration Testing?
A Web Application Penetration Test (often called a “pentest”) is a simulated cyberattack against your application. Unlike a real attack, however, this one is authorized, controlled, and performed by ethical security experts.
The goal is not to destroy your system but to identify weaknesses before malicious actors do. During a penetration test, security professionals simulate the actions of a malicious attacker to uncover vulnerabilities that could be exploited in a real-world attack.
The Analogy of the Friendly Burglar
Imagine you have just built a state-of-the-art bank vault (your web app). You believe the walls are thick and the locks are secure.
- Vulnerability Scanning is like having a robot walk around the perimeter checking if the doors are locked. It is automated, fast, and catches the obvious stuff.
- Penetration Testing is hiring a master locksmith to actively try to break in. They will pick the locks, climb through the vents, and trick the guards.
A pentest goes beyond finding a list of errors; it proves how those errors can be exploited to steal data or take over your system.
Why It Is Distinct from Automated Scanning
Many first-time founders make the mistake of running a $50 automated scanner and calling it a penetration test. This is dangerous.
- Scanners often generate false positives (alerting on things that aren’t actually risks).
- Scanners cannot understand business logic (e.g., a scanner doesn’t know that User A shouldn’t be able to see User B’s credit card).
- Scanners cannot chain vulnerabilities together to achieve a high-impact exploit.
Pentesting requires human intuition, creativity, and logic, as well as a focus on methodology and critical aspects of the application to ensure effective testing.
Understanding Web Applications
Web applications are the backbone of modern business, powering everything from customer portals to internal dashboards. Unlike static websites, web applications are dynamic systems that process user input, interact with databases, and often handle sensitive information over the internet. This complexity introduces a wide range of potential vulnerabilities that can be exploited by attackers.
For effective penetration testing, it’s essential to understand the architecture of web applications, how the front-end (what users see) communicates with the back-end (servers, databases, APIs), and how data flows between these components. Weaknesses in any layer can open the door to attacks such as SQL injection, cross-site scripting (XSS), or even remote code execution, where an attacker can run malicious code on your servers.
Penetration testers approach web application penetration by mapping out the system, identifying how users gain access, and pinpointing areas where security controls may be lacking. By thoroughly understanding the structure and logic of your web applications, testers can perform targeted testing to uncover vulnerabilities that could lead to unauthorized access, data breaches, or compromise of critical systems. This foundational knowledge is what separates a surface-level scan from a truly comprehensive application penetration testing engagement.
Why Startups Specifically Need Pentesting
You might think you are too small to be a target. This is a misconception. Automated bots scour the internet 24/7 looking for vulnerabilities; they do not care if you have one user or one million. Startups face a wide range of threats, from automated attacks to targeted exploitation, making proactive security measures essential.
Here are the practical reasons why startups must prioritize this:
1. The "Series A" Requirement
Venture Capitalists and investors are becoming increasingly risk-averse regarding cybersecurity. During due diligence for a Series A or B round, investors will almost always ask for your most recent third-party security audit.
- A clean pentest report signals operational maturity.
- Lack of a report signals negligence.
2. B2B Sales Enablement
If you sell software to other businesses (B2B), your customers will demand it. Enterprise clients simply cannot buy your software without a Vendor Risk Assessment.
- They will ask for a SOC 2 report or an ISO 27001 certification.
- A prerequisite for these compliances is an annual penetration test.
- Having a "Letter of Attestation" from a pentester speeds up your sales cycles significantly.
3. Regulatory Compliance
Depending on your industry, testing might not be optional.
- FinTech: PCI-DSS requires regular testing if you handle credit cards.
- HealthTech: HIPAA requires strict risk management practices.
- SaaS: GDPR requires you to secure European user data.
4. Preventing "Technical Debt"
Fixing a security flaw during the design or early development phase costs pennies. Fixing that same flaw after you have scaled to 100,000 users costs thousands in re-engineering time and potential downtime.
The Core Components of a Web App Pentest
When you hire a firm to test your application, they generally follow a standard methodology. This methodology is often based on a recognized framework, which provides structure and consistency to the penetration testing process. Understanding this lifecycle helps you manage the engagement effectively.
Phase 1: Scoping and Reconnaissance
Before a single test is run, the testers need to understand what they are attacking.
- Domain Enumeration: Finding all subdomains and hidden pages.
- Technology Fingerprinting: Identifying what coding languages, frameworks, and servers you are using.
- Data Flow Analysis: Understanding how data moves from the user to the database.
- Network Mapping: Mapping the network infrastructure that supports the web application, including identifying DNS servers, IP addresses, and other components that host or interact with the application.
During reconnaissance, testers may use passive reconnaissance techniques, such as reviewing historical data from the Wayback Machine, to gather information about the website without direct contact. It is important to note details such as server characteristics, open ports, and other findings during this phase. The goal is to build a comprehensive map of the target site and its supporting network.
Phase 2: Vulnerability Assessment
This is the broad-strokes phase where testers look for potential entry points and collect details about each potential vulnerability to inform later exploitation attempts.
- Checking for outdated server software.
- Looking for misconfigured SSL/TLS certificates.
- Identifying weak password policies.
Phase 3: Exploitation (The "Hack")
This is where the magic happens. The tester attempts to use the vulnerabilities found in Phase 2 to gain unauthorized access, often by attempting a variety of exploits, including those targeting file upload or file inclusion vulnerabilities.
- SQL Injection (SQLi): Attempting to execute commands, such as retrieving sensitive data or dumping database tables, by exploiting the database through tools like SQLMap.
- Cross-Site Scripting (XSS): Attempting to execute malicious scripts that can steal user session cookies or perform unauthorized actions on behalf of users.
- Broken Access Control: Trying to access an Admin dashboard while logged in as a basic user.
- File-related Exploits: Attempting to exploit file upload or file inclusion vulnerabilities, such as uploading a malicious file or including unauthorized files, to gain further access or control over the web application.
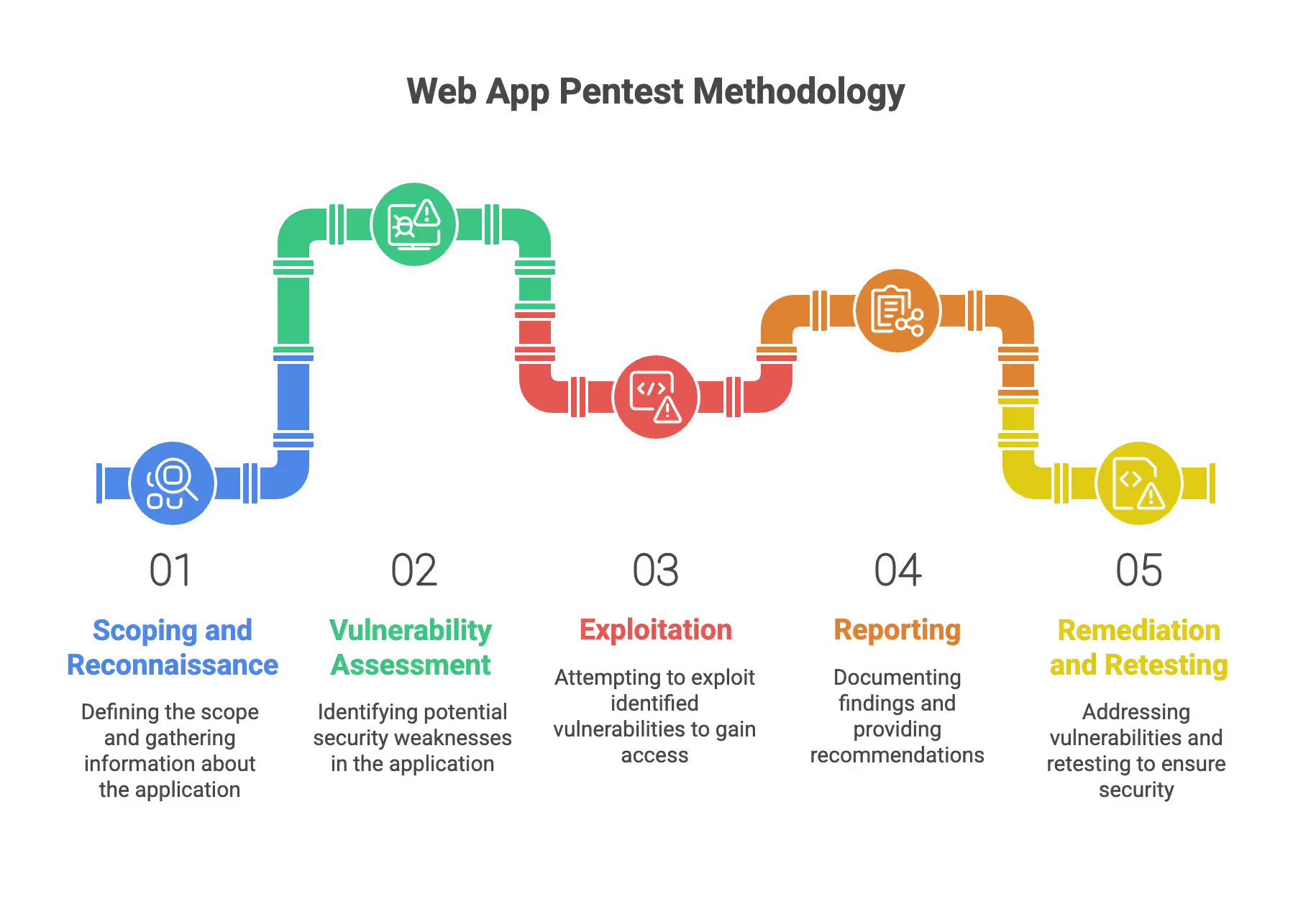
Phase 4: Reporting
The deliverable is a report, not the hack itself. A good report for a startup should include:
- Executive Summary: A non-technical overview for your investors and board.
- Technical Detail: Step-by-step instructions for your developers to reproduce the issue, including relevant server responses and error messages observed during testing.
- Risk Rating: A score (usually Critical, High, Medium, Low) based on impact and likelihood.
Phase 5: Remediation and Retesting
Once you fix the bugs, the testers must verify the fixes.
- Never accept a “fix” without a retest.
- Developers often patch a symptom but leave the root cause exposed. Remediation is not complete until all identified vulnerabilities have been retested and verified as fixed.
Hands-on Experience with Web Application Penetration
There’s no substitute for hands-on experience when it comes to web application penetration testing. Theoretical knowledge is important, but real-world testing requires practical skills in using advanced tools and techniques to uncover and exploit vulnerabilities.
Penetration testers rely on a suite of advanced tools—Burp Suite being a staple—for information gathering, vulnerability scanning, and exploitation. Hands-on testing means going beyond automation: it’s about manually probing the target system, understanding its unique logic, and identifying subtle flaws that automated scanners might miss. This includes everything from mapping out endpoints to crafting custom payloads that test the limits of your application’s security.
By practicing web application penetration testing in real scenarios, testers develop an intuition for where vulnerabilities are likely to hide and how attackers might chain together seemingly minor issues to gain access or escalate privileges. This experience is crucial for identifying vulnerabilities, performing effective remediation, and ultimately strengthening the security posture of your web applications. For startups, working with penetration testers who have this hands-on expertise ensures that your application is tested as thoroughly as possible—mirroring the tactics of real-world attackers.
Best Practices for Startups
To get the most Return on Investment (ROI) from a pentest, you need to approach it strategically. It is highly recommended to follow industry best practices to maximize the effectiveness of your penetration testing efforts.
Test Your Staging Environment
Do not test your production environment unless absolutely necessary.
- Pentesting involves aggressive tactics that can crash servers or corrupt data.
- Create a "Staging" or "UAT" (User Acceptance Testing) environment that is an exact mirror of production.
- This allows testers to attack freely without disrupting your real customers.
Embrace "White Box" Testing
There are different types of testing access:
- Black Box: The tester knows nothing and attacks from the outside (like a real hacker).
- White Box: You give the tester source code, documentation, and Admin credentials.
- Gray box: Mix White and Black testing.
For startups, Grey Box is superior. You are paying by the hour. Do not waste the tester’s time forcing them to guess your URLs. Give them access so they can find the deep, hidden logic flaws that a real hacker might take months to find.
Scope for Business Logic
Ensure the testers understand what your app does, not just how it is coded.
- If you are a FinTech app, can a user transfer negative money?
- If you are an E-commerce app, can a user modify the price of an item in the shopping cart before checkout?
- Automated tools will never find these logical loopholes.
Integrate with Your Workflow
Don't just ask for a PDF report.
- Ask the pentester to export findings into your ticketing system (Jira, Trello, GitHub Issues).
- This ensures security bugs are treated with the same workflow as feature bugs.
Common Vulnerabilities You Will Likely Face
The security industry relies on the OWASP Top 10, a list of the most critical web security risks. As a founder, you should be familiar with the big ones. Web app penetration testing is designed to identify and address these common vulnerabilities before they can be exploited.
1. Broken Access Control
This is currently the #1 vulnerability on the web. It happens when restrictions on what authenticated users are allowed to do are not properly enforced.
- Example: Changing the URL ID from /user/100 to /user/101 allows you to see someone else’s profile.
2. Cryptographic Failures
This involves not protecting sensitive data correctly.
- Example: Storing passwords in plain text in the database.
- Example: Transmitting credit card data over HTTP instead of HTTPS.
3. Injection
This occurs when untrusted data is sent to an interpreter as part of a command or query.
- Example: A user enters malicious code into a login field, tricking the database into logging them in without a password.
4. Insecure Design
This is a newer category focusing on risks related to design flaws.
- Example: Falsely assuming that a "secret" URL won't be discovered by bots.
- Example: Failing to put rate limits on a login page, allowing a bot to guess passwords infinitely.
5. Security Misconfiguration
This is usually a result of using default settings.
- Example: Leaving default Admin accounts active (Username: admin, Password: admin).
- Example: Displaying detailed error messages to users that reveal system paths and database versions.
Choosing a Vendor: A Guide for First-Time Buyers
The market is flooded with security vendors. Choosing the right one is difficult for non-technical buyers. Here is how to filter the noise.
Manual vs. Automated
This is the most critical distinction.
- The "Scam": Some vendors will charge you $2,000, run an automated tool, put their logo on the generic report, and hand it to you.
- The Real Deal: A true pentest involves a human engineer spending 40 to 100+ hours manually attacking your app.
Ask this question: "What percentage of the testing is manual versus automated?" If they say less than 80% manual, look elsewhere.
PTaaS vs. Traditional Consultancies
- Traditional Consultancies: You schedule a test in advance. You get a static PDF report. It is often more expensive but very thorough.
- PTaaS (Pentest as a Service): These are modern platforms where you can start a test in days. You see findings in real-time on a dashboard.
Sample Reports
Always ask to see a blinded sample report. Download sample reports from vendors to review the level of detail and clarity provided.
- Is it readable?
- Does it explain business risk or just technical jargon?
- Does it offer clear remediation steps?
Pitfalls to Avoid
Even with the best intentions, startups often stumble during the pentesting process. Avoid these common mistakes.
1. Scope Creep (or Scope Shrink)
- The Mistake: You forget to tell the tester about the API that powers your mobile app, or you exclude the Admin panel to save money.
- The Consequence: The most vulnerable part of your application goes untested. Hackers love Admin panels because they are often less secured than the user-facing app.
2. The "One-and-Done" Mentality
- The Mistake: Treating security as a checkbox. You do it once and forget it.
- The Consequence: Your developers push code every week. Next month's feature release could introduce a critical hole. You need at least annual testing, or testing after every major release.
3. Ignoring "Low" Risk Findings
- The Mistake: Focusing only on Critical and High issues and ignoring Medium or Low findings.
- The Consequence: Sophisticated attackers chain together several "Low" risk issues to create a "Critical" exploit. For example, a low-risk information leak combined with a low-risk misconfiguration can lead to a full breach.
4. Remediation Delays
- The Mistake: Getting the report and waiting months to fix the issues because "product features come first."
- The Consequence: Once a report exists, you are liable. If you are breached via a known vulnerability that you ignored, the legal consequences are severe.

Budgeting for Your Pentest
Pricing is opaque in this industry. Here is what to expect so you can budget accordingly.
Factors Influencing Cost
- Number of Roles: An app with Super Admins, Managers, Editors, and Viewers takes longer to test than an app with just one user type.
- Number of Endpoints: How many distinct pages and API calls does your app have?
- Complexity: A simple blog is cheap; a complex banking platform with 2FA and payment gateways is expensive.
Rough Estimates (Startup Tier)
Pro Tip: If you have a limited budget, be transparent with the vendor. Ask for a "Time-Boxed" assessment. Instead of testing everything, pay for 40 hours of their best effort focused on your most critical features (e.g., the payment and login modules).
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.
FAQ Cloud Penetration Test
What is cloud penetration testing?
Cloud penetration testing is an authorized and simulated cyberattack against your cloud infrastructure. It identifies security holes in your deployments and configurations before malicious actors can exploit them.
How does pentesting differ from vulnerability scanning?
Scanning is an automated and shallow check for known issues using software tools. Penetration testing is a human-led assessment that attempts to exploit vulnerabilities to provide a realistic picture of risk.
Why do startups need cloud penetration testing?
It is essential for passing vendor risk assessments and meeting compliance standards like SOC 2 or HIPAA. Testing also protects intellectual property and prevents attackers from racking up thousands of dollars in compute costs.
What is the shared responsibility model in cloud security?
Providers like AWS or Azure secure the physical infrastructure while you are responsible for everything inside the cloud. This includes your data, application code, user permissions, and encryption settings.
What is a grey box penetration test?
In a grey box test, the startup provides testers with some information like user credentials or documentation. This approach is efficient because it allows experts to find deep logic flaws quickly.
How often should a startup perform a penetration test?
You should schedule a penetration test at least annually or after every major product release. Regular testing is vital because a test from six months ago becomes obsolete as you release new code.
FAQ Web Application Penetration Testing
What is web application penetration testing?
A web application penetration test is a controlled simulated cyberattack performed by ethical experts to identify vulnerabilities. It uses human intuition to find logic flaws and security gaps that automated tools often miss.
Why do startups need a penetration test?
Startups need pentesting to satisfy investor due diligence and meet security requirements for B2B enterprise sales. It is also required for major compliance standards like SOC 2, HIPAA, and PCI-DSS.
How much does a web application pentest cost?
A basic pentest for an early-stage startup typically costs between $4,000 and $8,000. More complex or compliance-focused tests for FinTech or healthcare applications usually range from $5,000 to $30,000.
What is the difference between vulnerability scanning and pentesting?
Vulnerability scanning is an automated tool that checks for basic security gaps and known errors. Penetration testing involves a human expert actively trying to exploit weaknesses and bypass security controls.
What is white box penetration testing?
White box testing gives the expert full access to source code, documentation, and administrator credentials. This method is more efficient for startups as it allows for deeper analysis of hidden logic flaws.
How often should a startup perform a penetration test?
Startups should perform a penetration test at least annually or after every major feature release. This prevents technical debt and ensures new code does not introduce critical security holes.


%20(16)%20(1).avif)

%20(13)%20(1).avif)
%20(7)%20(1).avif)