Black box penetration testing is a method of security assessment where the ethical hacker simulates a real world cyberattack on a system without having any prior knowledge of its internal workings, architecture, or source code.
This approach is frequently referred to as zero knowledge testing because the tester begins with nothing more than the name of the company or a public IP address, forcing them to mimic the behavior of an external threat actor who must locate vulnerabilities solely through open source intelligence and external probing. In cybersecurity, this is often called a black box pen approach, where the tester operates entirely from an outsider’s perspective.
By adopting the perspective of an outsider, this methodology provides organizations with a realistic validation of their public facing security posture and incident response capabilities, focusing on defending against external attacks that simulate real world attacks.
Understanding the Core Philosophy
The philosophy behind black box testing is rooted in realism. In a genuine cyberattack, a hacker rarely has access to network diagrams or administrative credentials at the start of their campaign. They must work for every piece of information they gather. Consequently, a black box test is the most authentic representation of an attack by a motivated outsider, simulating external attacks to test the system's security.
The tester assumes the role of an unprivileged attacker. They are not given a map of the network; they must draw the map themselves. They are not given user accounts; they must steal them or bypass the authentication mechanisms entirely.
This forces the security team to evaluate not just the technical vulnerabilities of their software, but also the visibility of their digital footprint and the robustness of their perimeter defenses, as well as their ability to withstand simulated real world attacks.
The Pros and Cons of Black Box Testing
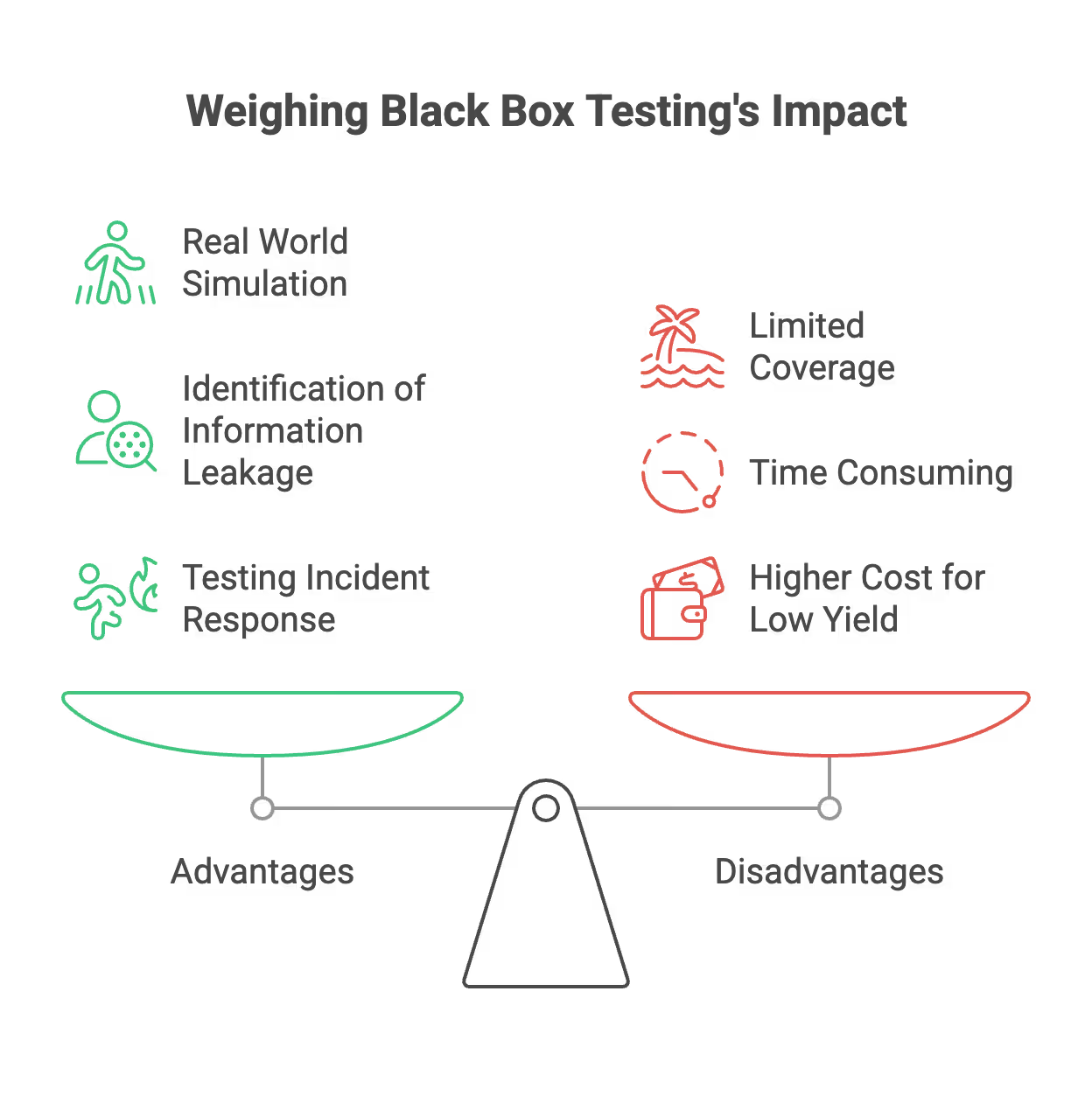
To understand whether this methodology suits a specific organizational need, one must weigh its distinct advantages and disadvantages.
Advantages
- Real World Simulation: The primary benefit is the accurate simulation of an external attack. It demonstrates exactly what a hacker can see and exploit from the public internet without insider help, effectively simulating real world attacks.
- Identification of Information Leakage: This method excels at highlighting Open Source Intelligence (OSINT) risks. Testers often find sensitive data on public repositories, social media, or forgotten subdomains that internal teams assumed were private.
- Testing Incident Response: Because the target organization’s IT staff is often unaware of the specific details of the test, black box engagements effectively measure the alertness and reaction time of the Blue Team (defenders).
- Technology Agnostic: The tester focuses on the behavior of the system rather than the code. This allows them to identify logic flaws and configuration errors that might be overlooked during a code review.
Disadvantages
- Limited Coverage: Since the tester spends a significant amount of time performing reconnaissance and attempting to breach the perimeter, they may not have time to test internal applications deeply. If they cannot breach the outer wall, the internal systems remain untested.
- Time Consuming: The reconnaissance phase requires substantial time. Unlike white box testing where the scope is handed over immediately, a black box tester must manually discover the scope.
- Higher Cost for Low Yield: Organizations may pay for weeks of testing only to find that the firewall held up. While this is a positive security result, it provides less actionable data regarding the security of the internal applications compared to other testing methods.
The Methodology of a Black Box Assessment
A black box engagement follows a rigorous, albeit unscripted, lifecycle. Because the tester starts with zero knowledge, the process relies heavily on discovery.
Phase 1: Reconnaissance and OSINT
The first and most critical phase is intelligence gathering. Before sending a single packet to the target network, the pentester scours the internet for information. This is often called Open Source Intelligence or OSINT.
Testers look for employee email addresses on LinkedIn to create phishing lists. They search GitHub and Pastebin for leaked API keys or credentials. They utilize DNS interrogation to find subdomains that the company may have forgotten, such as a staging server or an old marketing portal.
The goal here is to build a profile of the target that reveals potential weak points. During this phase, testers also collect IP addresses associated with the target organization, which are used for both passive and active reconnaissance to assess the organization's security posture and identify possible entry points.
Phase 2: Scanning and Enumeration
Once the tester has identified the digital assets, they move to active scanning. This involves interacting with the target systems to determine what services are running.
The tester uses automated tools and manual techniques to identify open ports. If Port 80 is open, there is a web server. If Port 22 is open, there is an SSH service. The tester then enumerates these services to find out exactly what version of software is running.
For example, knowing that a web server is running an outdated version of Apache gives the tester a specific path to research for known vulnerabilities.
Vulnerability scanning is performed to identify weaknesses and misconfigurations, and special attention is paid to the operating systems in use, as different operating systems may have unique vulnerabilities and attack surfaces.
Phase 3: Vulnerability Discovery
With a map of the network and a list of running services, the tester begins to look for specific flaws. This is distinct from exploitation. In this phase, the tester is hypothesizing.
They might input invalid data into a login form to see if the system returns a database error, indicating a potential SQL injection vulnerability. They might check if the email server allows relaying, which could be used for spam.
They are cataloging potential vulnerabilities, system vulnerabilities, and outdated software versions based on the configuration errors and outdated software discovered in the previous phase.
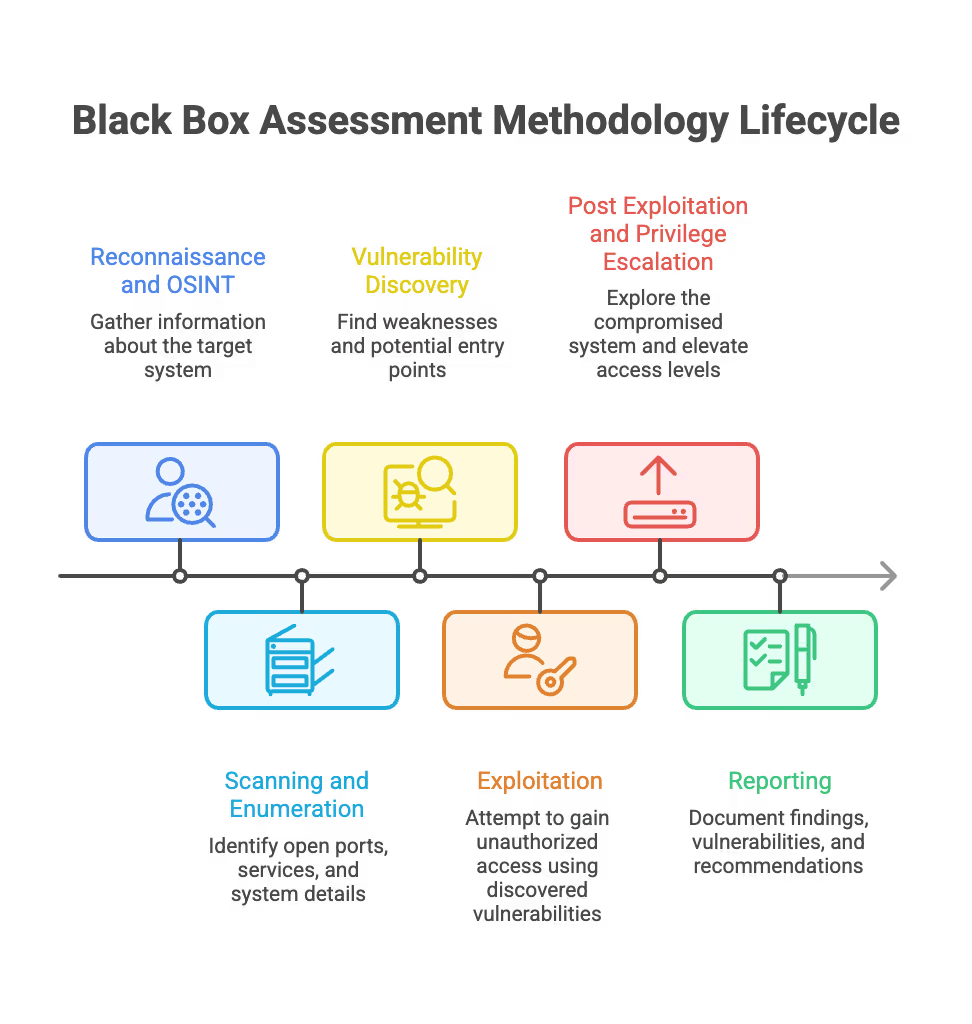
Phase 4: Exploitation
This is the phase that distinguishes a penetration test from a simple vulnerability scan. The tester attempts to weaponize the flaws they found to gain unauthorized access.
If they discovered a vulnerability in a web application, they will write or download a script to exploit it. If successful, they may gain a command shell on the server. This phase confirms whether a theoretical vulnerability is actually dangerous in the specific context of the target environment. Exploitation techniques may include targeting identified vulnerabilities, gaining access through privilege escalation, and using brute force attacks to bypass authentication or escalate privileges.
Phase 5: Post Exploitation and Privilege Escalation
Gaining entry is rarely the final goal. The objective is to determine the business impact. Once inside a server, the tester attempts to pivot.
Pivoting involves using the compromised system as a beachhead to launch attacks deeper into the internal network. The tester also attempts privilege escalation, trying to go from a low level web user to an administrator or “root” user. The ultimate goal is to gain complete access or complete access to the system, demonstrating how much damage an attacker could do after compromising a single perimeter device.
Phase 6: Reporting
The final output of the engagement is a comprehensive report. In a black box test, this report tells a story. It details the narrative of the attack, explaining exactly how the tester moved from having zero knowledge to holding administrative control. It includes an executive summary for leadership and technical remediation steps for the engineering team. The report also covers security validation of the findings, ensures that false positives are minimized, and documents the test cases used to provide thorough and actionable results.
Distinguishing Black Box from Gray Box Testing
To fully appreciate the utility of black box testing, it is essential to compare it with its counterpart, gray box testing. While both aim to secure the environment, they operate under different assumptions and offer different values.
Black box pentesting, also known as black box assessments, involves black box testers using testing methodologies such as exploratory testing to simulate attacks without any prior knowledge.
In contrast, gray box pentest or grey box penetration testing provides the tester with partial knowledge, such as some credentials or system details, allowing for a more balanced and efficient evaluation of vulnerabilities. Grey box testing (or grey box) is a hybrid approach that combines elements of both black box and white box testing, leveraging partial knowledge to simulate insider threats or perimeter breaches.
Information Availability
The most distinct difference lies in the starting data.
- Black Box: The tester has zero information. They must find the login page, guess the username, and brute force the password.
- Gray Box: The tester is provided with partial information. They are usually given valid user credentials (such as a standard employee account) and potentially some architectural diagrams.
Focus of the Assessment
- Black Box: The focus is on the perimeter and the external footprint. It tests the strength of the front door. If the tester cannot break in, the internal application logic remains largely untested.
- Gray Box: The focus is on internal security and lateral movement. Since the tester is given credentials, they do not waste time trying to break the perimeter. They log in immediately and start testing what a compromised user or a malicious insider could do.
Efficiency and Cost
- Black Box: This is less efficient regarding vulnerability discovery per hour. A significant portion of the engagement is spent on reconnaissance.
- Gray Box: This is highly efficient. The “boring” work of finding the server and guessing passwords is skipped. The tester spends almost all their time identifying complex security flaws inside the application.

The Strategic Application of Black Box Testing
Organizations should not view black box testing as a replacement for other testing types but as a specific tool for a specific purpose. It is best utilized in specific scenarios, such as an external penetration test to assess the organization's security posture from the outside. A thorough risk assessment should be conducted to evaluate potential consequences, disruptions, or compliance issues before proceeding with black box testing.
Scenario A: Maturity Validation
A company that has already performed extensive white box (full code review) and gray box testing should commission a black box test. This serves as the final exam. It verifies that the controls implemented during previous phases effectively stop an unknown attacker.
Scenario B: M&A Due Diligence
When one company acquires another, they often want to know the security posture of the acquisition target without alerting the target’s internal IT teams immediately. A black box test allows the acquiring company to assess the risk of the new network from an external perspective.
Scenario C: Compliance and Vendor Requirements
Certain regulatory standards require organizations to perform external penetration tests to demonstrate that customer data is safe from internet based threats.
Deep Dive into Black Box Attack Vectors
A world class black box assessment utilizes a variety of sophisticated attack vectors. It is not limited to simply scanning a firewall. Attack surfaces include web apps, networks, and wireless systems, with testers focusing on system inputs and the system's security to uncover vulnerabilities.
Social Engineering
Because the tester has no credentials, humans often become the easiest entry point. Testers may call the helpdesk impersonating an employee who lost their password. They may send spear phishing emails containing malicious attachments to executive assistants. In a black box test, hacking the human is often faster than hacking the firewall.
Web Application Logic Attacks
Testers look for logic gaps that scanners miss. For example, they might manipulate the URL in an e-commerce store to see if they can change the price of an item to zero before checking out. Without source code, the tester relies on intuition and experience to guess how the developer built the system and where they might have made a mistake.
Password Spraying and Credential Stuffing
Testers utilize databases of previously leaked passwords from other companies. They know that employees often reuse passwords. By trying these leaked passwords against the target organization’s email portal, they often gain entry without ever deploying a software exploit.
The Role of Automated Tools vs Human Intelligence
There is a misconception that penetration testing is merely running software tools. While tools are essential for the initial scanning in a black box test, they are insufficient for a complete assessment.
Automated scanners are excellent at finding known vulnerabilities, such as an unpatched version of Windows. However, they are terrible at understanding context. A scanner might report a login page as secure because it uses encryption. A human black box tester, however, will notice that the login page helps users guess usernames by displaying different error messages for valid vs invalid accounts.
World class black box testing relies on the creativity of the human mind. The tester must think laterally. If the front door is locked, they check the windows. If the windows are barred, they check the ventilation shafts. This creative persistence is what defines a high quality engagement. To ensure thoroughness, testers often use a black box pentesting checklist aligned with standards like OWASP, and after vulnerabilities are identified, organizations should implement appropriate security controls to remediate the findings.
Managing the Risks of Black Box Testing
While beneficial, black box testing carries inherent risks that must be managed through a proper Rules of Engagement (RoE) document.
System Stability
Because the tester does not know the internal architecture, there is a risk that a scanning tool might overwhelm a fragile legacy server, causing a denial of service. The RoE must establish limits on scanning intensity.
Data Privacy
Testers may inadvertently stumble upon highly sensitive customer data or intellectual property. It is vital that the engagement contract includes strict non disclosure agreements and protocols for handling sensitive evidence.
De-confliction
Since the internal security team may not know about the test, they might block the tester’s IP address. There must be a point of contact (usually a CISO or IT Director) who is aware of the test and can intervene if the response escalates to law enforcement involvement.
It is important to note that black box testing is performed without insider knowledge or access to the system's internal workings, which limits the depth of the assessment compared to white box or gray box approaches.
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.
FAQ Black Box Pentest
What is black box penetration testing?
Black box penetration testing is a security assessment where the tester has zero prior knowledge of the internal systems. It simulates a real world attack from the perspective of an external threat actor.
What are the main benefits of black box testing?
It provides a realistic simulation of external attacks and identifies information leaks via open source intelligence. It also measures the alertness and reaction time of an organizations internal security team.
How does black box testing differ from gray box testing?
Black box testing involves zero prior knowledge and focuses on the perimeter. Gray box testing provides partial information like user credentials to focus on internal security and lateral movement.
What are the phases of a black box assessment?
The process includes reconnaissance, scanning, vulnerability discovery, exploitation, post-exploitation, and reporting. Each phase builds on information discovered in the previous stage to demonstrate business impact.
Why should startups perform black box penetration tests?
It serves as a final validation of security controls and supports compliance readiness for standards like SOC 2 and ISO 27001. It also builds trust with investors and enterprise clients by proving infrastructure resilience.