A SOC 2 audit is an independent assessment performed by certified public accountants that evaluates whether your startup’s security controls meet the standards set by the American Institute of Certified Public Accountants. Enterprise customers keep asking for it in 2026 because it provides standardized proof that you protect sensitive data and manage customer data responsibly.
This guide walks you through everything a startup CEO or CTO needs to know, from understanding what a SOC 2 audit actually involves to building a step by step workflow that gets you from gap analysis to final report delivery.
Answering Your Core SOC 2 Audit Question Fast
When enterprise buyers ask about SOC 2, they want assurance that your SaaS platform handles their data with proper security controls and documented processes. For service organizations like yours, a SOC 2 audit is an independent CPA assessment of your security controls against the AICPA Trust Services Criteria.
Most early stage SaaS companies pursue SOC 2 compliance primarily to unblock stalled deals and shorten security questionnaires rather than for pure regulatory compliance reasons. When you hand over a clean SOC 2 report, procurement teams can skip the 40 page custom questionnaires and move straight to contract negotiation.
Consider this example: a Series A SaaS vendor needs a SOC 2 Type 2 report to close a three year contract with a Fortune 500 customer by Q4. Without it, the deal sits in procurement limbo while competitors with existing reports move forward.
The quick difference between report types: Type 1 evaluates control design at a single point in time, while Type 2 evaluates both design and operating effectiveness over a period of three to twelve months. Enterprise customers strongly prefer Type 2 because it proves your controls actually worked over time.

The rest of this article serves as your step by step playbook, covering Trust Services Criteria selection, readiness workflows, audit timelines, cost expectations, and how to avoid common pitfalls that derail first time audits.
What Is a SOC 2 Audit for a SaaS or Startup
SOC 2 stands for System and Organization Controls 2, a framework created by the AICPA focused on five trust services categories: security, availability, processing integrity, confidentiality, and privacy.
Understanding SOC 2 requires grasping one critical distinction: it is an attestation, not a certification. A CPA firm issues an opinion on how well your controls operated over a defined period, rather than giving you a simple pass or fail badge. This means your SOC 2 report will contain a detailed description of your systems, the controls you have in place, and the auditor’s findings about whether those controls worked as designed.
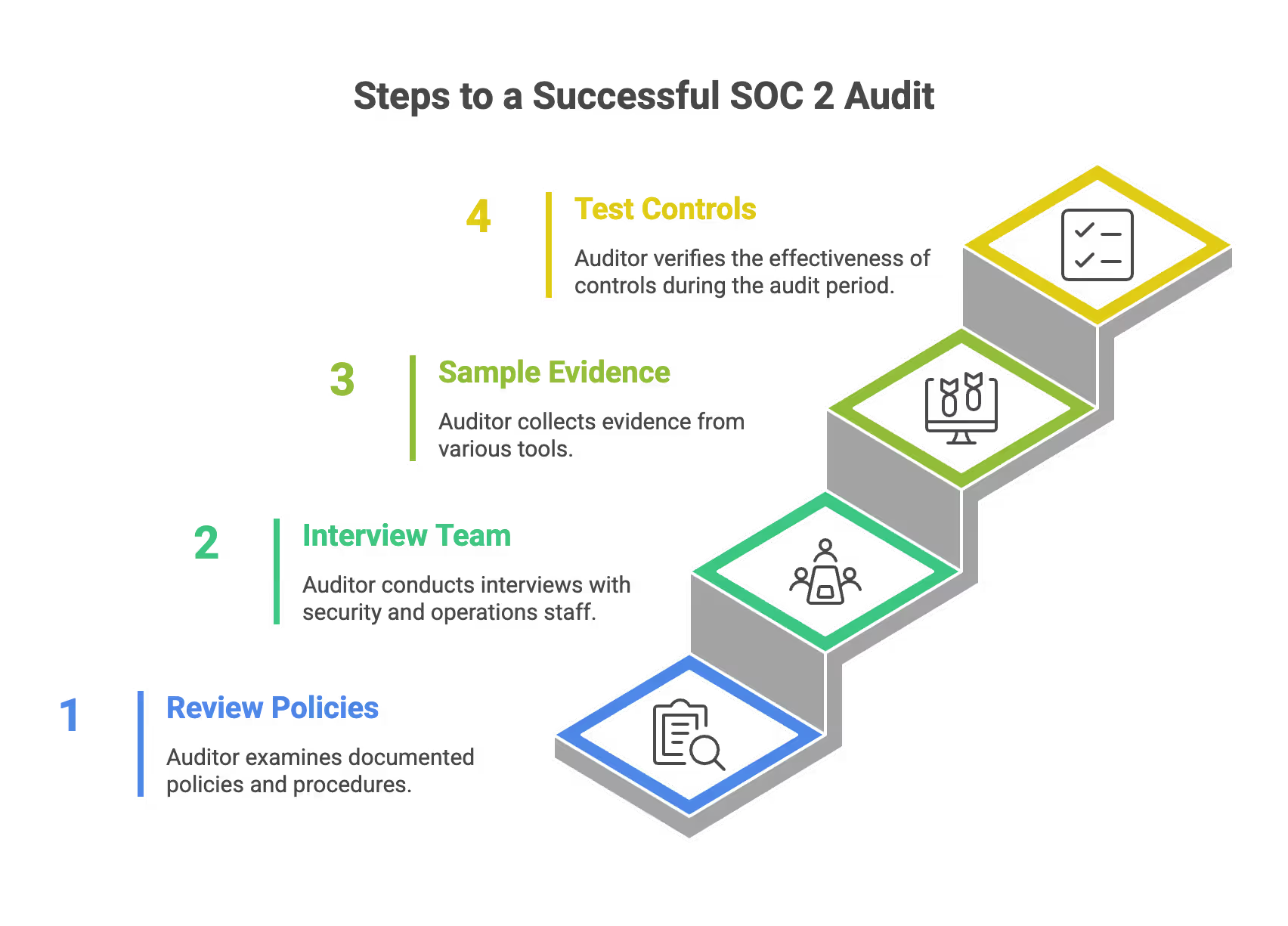
At a high level, here is how a SOC 2 audit works:
- The auditor reviews your documented policies and procedures
- They interview team members responsible for security and operations
- They sample evidence from tools like AWS, GitHub, Okta, Google Workspace, and ticketing systems such as Jira
- They test whether your controls actually operated effectively during the audit period
For most cloud native SaaS platforms, the in scope system typically includes:
- Production cloud infrastructure (AWS, Azure, or GCP)
- CI/CD pipeline and code repositories
- Customer facing application and APIs
- Supporting services such as identity provider and helpdesk
Only licensed CPA firms can sign SOC 2 reports, though security firms like SecureLeap help with readiness assessment, control implementation, and evidence gathering before the formal audit begins.

Why SOC 2 Matters to Small SaaS and Startup Leaders
SOC 2 directly impacts your sales velocity, fundraising ability, and enterprise trust. For early stage companies, these three factors often determine whether you hit your growth targets or struggle to close deals.
By 2026, most procurement and security teams in North America require a recent SOC 2 report from SaaS vendors before signing annual or multi year agreements. This trend has accelerated as data breaches make headlines and organizations demonstrate increased scrutiny of their third party vendors.
The practical impact shows up immediately in your sales process. Before a SOC 2 Type 2 report, your team might spend hours completing 40 page custom security questionnaires for each prospect. After receiving your report, you can simply share a standard SOC 2 package under NDA and move to contract discussions.
Concrete benefits for startup founders include:
- Improved win rate in enterprise RFPs where SOC 2 is a requirement
- Faster deal cycles since security due diligence happens once rather than per customer
- Lower friction in due diligence for Series A and Series B funding rounds
- Clearer internal controls and security processes that reduce actual risk
- Competitive advantage over non compliant rivals who lose 30 to 40 percent of deals
Risk reduction also carries financial weight. Public studies estimate average breach costs for small businesses in the hundreds of thousands of dollars. Documented controls like MFA, centralized logging, and quarterly access reviews materially lower both the likelihood and impact of security incidents.
SOC 2 compliance also creates a foundation for alignment with other frameworks. If your startup later expands into EU markets or healthcare, you will find that many controls map directly to ISO 27001 and HIPAA requirements. This means your initial investment in establishing controls pays dividends across multiple compliance objectives.
Trust Services Criteria and How Auditors Scope Your SOC 2
The Trust Services Criteria define what auditors evaluate during your SOC 2 audit. Understanding how to select the right criteria for your startup helps you avoid unnecessary work while meeting customer expectations.
Security criteria are mandatory in every SOC 2 report and serve as the foundation for all other categories. The other four, availability processing integrity confidentiality and privacy, are optional based on your service and what your customers require. Most startups select Security plus one or two additional criteria that match their product and market.
Here is what each criteria covers in practical terms:
Security (Required)
The security criteria cover your organization’s security posture and ability to protect sensitive customer data from unauthorized access. Typical SaaS controls include:
- Enforced MFA and SSO across all production and corporate systems
- Centralized logging and continuous monitoring of audit trails
- Endpoint protection on employee devices
- Secure coding practices and code review requirements
- Background checks for staff with production access
- Access controls based on least privilege principles
Availability
Availability addresses your organization’s ability to maintain uptime commitments and service level agreements. Auditors expect to see in 2026:
- Documented uptime targets and SLA definitions
- Incident response procedures and on call rotations
- Disaster recovery tests conducted at least annually
- Backup and restore drills with documented results
- Monitoring and alerting for system processing issues
Processing Integrity
This criteria verifies that data processing is complete, accurate, timely, and authorized. Practical examples include:
- Automated test coverage with minimum thresholds
- Code review requirements before merging to main branches
- Change management through Git pull requests with approvals
- Deployment gates that prevent unauthorized releases
- Validation of data inputs and outputs in critical workflows
Confidentiality
Confidentiality protects information designated as confidential from unauthorized disclosure. Controls typically include:
- Data classification using a simple two or three level scheme
- Encryption at rest in services like AWS RDS and S3
- Encryption in transit with TLS 1.2 or higher
- Restricted access to production databases
- Secure handling of protected health information if applicable
Privacy
Privacy connects to regulatory compliance requirements under laws such as GDPR and CCPA. Startups document:
- Data retention policies and schedules
- Rights to deletion and data portability
- Cookie preferences and consent management
- Third party data sharing disclosures in privacy notices
- Processes for responding to data subject requests
For lean startups, a practical scoping approach works as follows:
Starting narrow allows you to reach your first SOC 2 report faster while maintaining the flexibility to expand scope in future audits.
SOC 2 Type 1 vs Type 2 for Early Stage Companies
Choosing between Type 1 and Type 2 depends on your specific deal deadlines and how much groundwork you have already completed. Both report types serve different purposes in your sales and compliance strategy.
Type 1 Report (Point in Time)
A Type I report evaluates the design of your controls at a specific date, for example, as of 30 June 2026. This approach works when you need something in hand quickly to move a proof of concept to pilot or to show immediate compliance progress to a prospect.
Type 1 does not prove that controls actually operated consistently. It confirms that you have designed controls that should work if implemented correctly.
Type II Report (Period of Time)
A Type II report evaluates both design and operating effectiveness of your service organization’s controls over a defined period, usually three to twelve months. For example, a report might cover the period from 1 January to 30 June 2026.
Enterprise customers strongly prefer Type 2 because it proves your internal controls actually ran for months. Quarterly access reviews, incident response drills, vendor management processes, and other recurring controls must demonstrate consistent operation across the entire review period.
Timeline Comparison
Decision Guidance for Founders
If you have a must win deal by Q1 2026 and no security groundwork in place, start with a Type 1 to demonstrate immediate progress. Then commit to a Type 2 observation period immediately after. This gives your prospect confidence that you are on a clear path to full compliance.
If you have six months or more before your critical deal deadline and already have basic security controls operating, skip Type 1 and go straight to Type 2. The Type II report carries significantly more weight with enterprise security teams and provides stronger evidence for ongoing compliance with your existing controls.
Step by Step SOC 2 Audit Readiness Workflow
This workflow outlines concrete actions for a 10 to 150 person SaaS company preparing for their first SOC 2 audit. Each step builds on the previous one to create a structured path to report delivery.
Step 1: Define Your Why and When
Specify your target contract or board objective. For example, closing three enterprise customers by December 2026. Then select your report type (Type 1 or Type 2) and identify your ideal audit window. Work backward from your deadline to establish milestone dates.
Step 2: Define Your Scope
List everything that will be in scope for the audit:
- Production cloud accounts (AWS, Azure, GCP)
- CI/CD pipeline and code repositories
- Identity provider (Okta, Azure AD)
- Corporate productivity tools (Google Workspace, Slack)
- Engineering laptops and mobile devices
- Primary data centers or cloud regions
- Critical SaaS dependencies
Narrowing scope reduces complexity and cost while still meeting customer requirements.
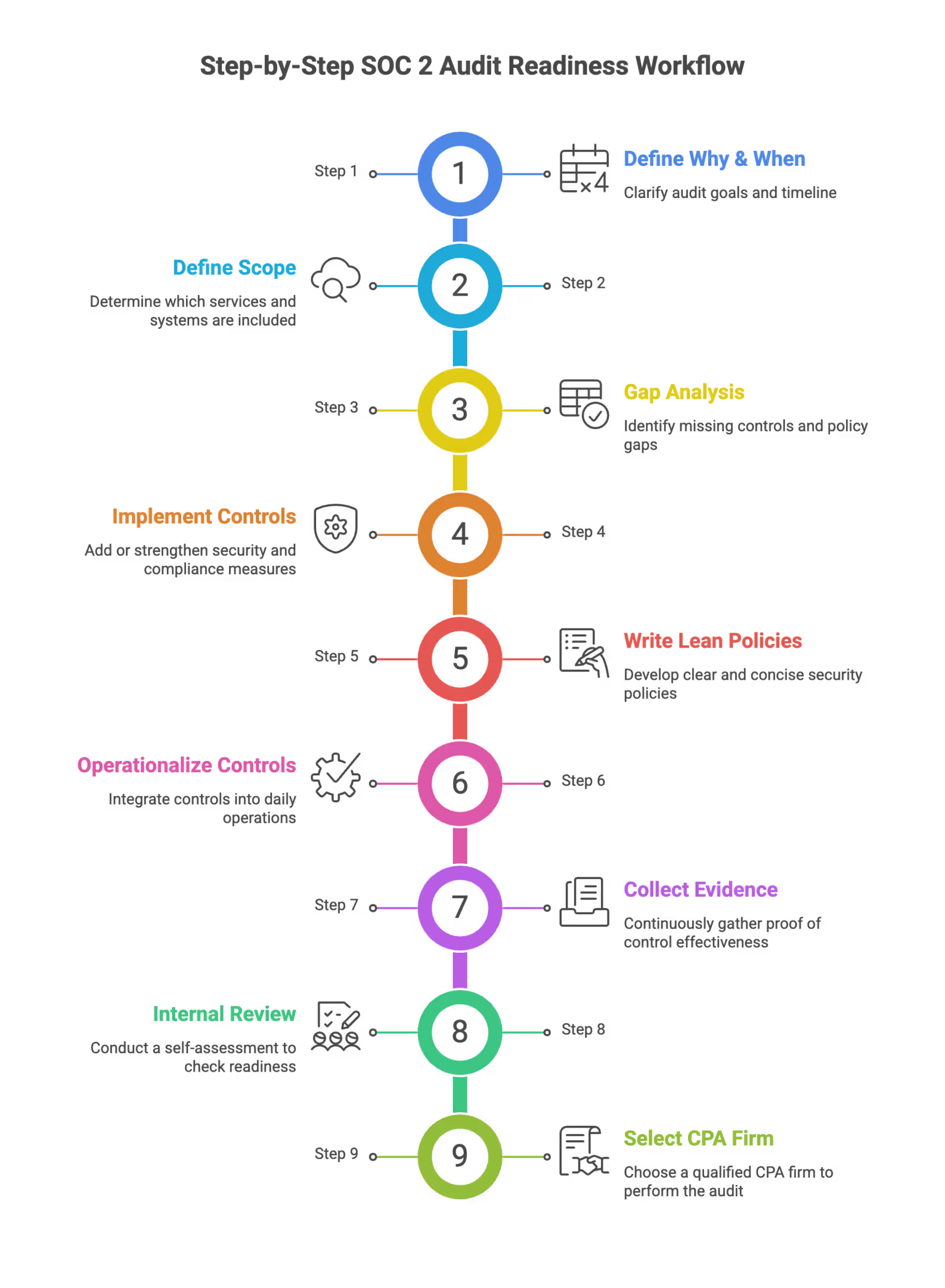
Step 3: Run a Gap Analysis
Compare your current state against the five trust services criteria using a security consultant like SecureLeap or mapping tools from platforms like Drata, Vanta, or Secureframe. Identify missing policies, technical controls relevant to your scope, and evidence gaps.
Common gaps for first time audits include:
- No formal information security policy
- Lack of centralized logging
- Missing vendor risk management process
- Incomplete asset inventory
- No documented incident response procedures
Step 4: Implement Missing Controls
Focus on basics with a pragmatic bias rather than over engineering:
- SSO and MFA enforcement on all critical systems
- Centralized logging with appropriate retention
- Quarterly access review process with documented approvals
- Vendor risk review template for third party vendors
- Secure development lifecycle with code review gates
- Incident response runbook with defined roles
Step 5: Write Lean Policies
Create audit ready policies that reflect how your startup actually works:
- Information Security Policy
- Acceptable Use Policy
- Access Control Policy
- Change Management Policy
- Incident Response Policy
- Business Continuity and Disaster Recovery Policy
- Vendor Management Policy
Avoid copying templates that do not match your operations. Auditors will test whether you follow your own documented procedures.
Step 6: Operationalize Controls
Step 7: Collect Evidence Continuously
Do not wait until the audit to gather evidence. Collect and organize throughout the observation period:
- Screenshots and exports from security tools
- Logs from cloud providers and applications
- Tickets showing approvals and completions
- Board meeting minutes with security discussions
- Security awareness training completion records
evidence in a structured repository mapped to each control requirement. Cloud services like compliance automation platforms simplify this significantly.
Step 8: Run an Internal Readiness Review
Before engaging your CPA firm, conduct a mock audit to test whether evidence is complete. An external firm like SecureLeap can perform this readiness assessment and uncover issues while you still have time to address them.
Step 9: Select Your CPA Audit Firm
Choose an external auditor with experience auditing cloud native startups in your industry. Agree on:
- Audit period and report delivery date
- Detailed evidence request list
- Communication cadence and escalation paths
- Handling of potential exceptions or qualified opinion scenarios

Inside the SOC 2 Audit Process with a CPA Firm
Once you engage your CPA firm and the audit formally begins, here is what CEOs and CTOs should expect at each phase.
Initial Planning
The auditor schedules a planning call to review scope, your control list, key systems, and the observation period. They share a detailed evidence request list, often hosted in a secure portal where your team will upload documentation throughout the engagement.
During this phase, you confirm which trust services principles are in scope and clarify any ambiguity about control boundaries or responsibilities.
Evidence Collection and Walkthroughs
Your team uploads policies, CSV exports from your identity provider, cloud configurations, task tickets showing approvals, and screenshots demonstrating control operation. The auditor schedules live walkthrough sessions where you demonstrate how processes actually work.
These walkthroughs typically cover:
- User provisioning and deprovisioning workflows
- Change management and deployment processes
- Incident response procedures
- Vulnerability management workflows
- Vendor review processes
Testing Methods
The third party auditor tests your controls using several methods:
- Sampling user accounts from AWS and Okta to verify access appropriateness
- Checking that terminated employees lost access within your defined timeline (typically 24 hours)
- Reviewing tickets for quarterly access reviews and confirming approvals occurred
- Verifying incident logs match your documented response procedures
- Testing data security controls like encryption configurations
For Type 2 audits, auditors test samples across the entire period. They might review three or four different quarterly access reviews to ensure controls related to access management operated consistently. A control failure in March cannot be hidden by a clean June review.
Exception Handling
Not every gap results in a qualified opinion. Minor issues with documented remediation efforts may appear in the report but still allow an unqualified opinion. The auditor notes the exception and describes your corrective action.
Systemic failures or material weaknesses that indicate your organization’s internal controls did not operate effectively throughout the period may lead to a qualified opinion. This outcome is rare for well prepared startups but represents significant reputation risk.
Final Report Delivery
The SOC 2 report you receive includes:
- System description detailing your infrastructure and processes
- Management assertion about control design
- Auditor opinion (ideally unqualified)
- Control descriptions mapped to trust services categories
- Test results and any exceptions noted
You can share this report under NDA with prospects, business partners, and user entities who need assurance about your security practices.
Typical SOC 2 Audit Issues for Startups and How to Avoid Them
First time audits frequently surface similar problems. Knowing these pitfalls in advance helps you avoid scrambling during the observation period.
Here 9 commons mistakes SOC 2 Audits :
Incomplete Asset Inventory
Many startups cannot produce a complete list of laptops, cloud accounts, and SaaS tools when asked. Without knowing what exists, you cannot prove you are protecting it.
Mitigation: Implement a lightweight asset management system or MDM before your audit period starts. Track all endpoints, cloud resources, and third party service providers in a central inventory.
Weak Access Control Practices
Shared admin accounts, lack of SSO, and inconsistent offboarding create significant audit exceptions. These gaps directly undermine your organization’s security controls.
Mitigation: Enforce SSO and MFA on core systems. Phase out shared credentials entirely. Document joiner, mover, and leaver procedures with specific timelines for access revocation.
Missing or Stale Policies
Policies copied from templates that do not match your actual workflows create problems during walkthroughs. Auditors quickly identify when documentation says one thing but staff describe different practices.
Mitigation: Align policies to how your team actually works. Have leadership formally approve and date each policy. Schedule annual reviews to keep documentation current.
Inadequate Logging and Monitoring
Production workloads without centralized logs make it impossible to detect or investigate security incidents. This gap affects both your security posture and your ability to provide evidence.
Mitigation: Enable cloud native logging services like AWS CloudTrail, CloudWatch, and VPC Flow Logs. Implement an affordable SIEM or log aggregation solution. Continuously monitor critical systems and configure alerts for suspicious activity.
Vendor Risk Management Gaps
Startups often rely heavily on SaaS tools but lack any formal review of these critical suppliers. This creates blind spots in your strong control environment.
Mitigation: Maintain a vendor inventory with risk ranking for each provider. Collect and store SOC 2 or ISO 27001 certificates and Data Processing Agreements for critical vendors. Conduct annual reviews of your most important third party relationships.
Evidence Gaps from Reactive Collection
Teams that try to reconstruct evidence at the end of the audit window face missing documentation and inconsistent records. This approach also creates stress during an already demanding period.
Mitigation: Establish a quarterly or monthly evidence review schedule. Assign a compliance owner (or virtual CISO) who continuously monitors evidence completeness and flags gaps early.

SOC 2 Audit Timeline and Cost Expectations for Small SaaS Companies
Realistic planning requires honest numbers. Here is what founders should expect for budget and milestone planning without marketing spin.
Typical End to End Timeline
For a first SOC 2 Type 2 report, plan to start readiness work six to nine months before your desired report delivery date. This includes at least three months of audit period plus one to two months for fieldwork and report writing.
Example Milestone Schedule
Cost Ranges
Prices vary significantly based on scope complexity, number of trust services criteria, company size, and auditor selection.
Controlling Costs
Several strategies help manage your SOC 2 investment:
- Narrow scope to only the systems and criteria customers actually require
- Avoid adding unnecessary criteria like Privacy unless customer contracts demand it
- Start with Type 1 when deal deadlines are aggressive and budget is constrained
- Use compliance automation platforms to reduce manual evidence gathering by up to 70 percent
- Bundle services like readiness assessment and penetration testing for volume discounts
SecureLeap offers bundled services combining readiness consulting, penetration testing, and coordination with automation tools to reduce both cost and internal time spent. This approach helps startups achieve continuous compliance without dedicating a full time employee to the effort.
How SecureLeap Supports Your SOC 2 Audit Journey
SecureLeap focuses specifically on seed to Series B technology startups and SMB SaaS companies that need SOC 2 compliance, often for the first time, and lack a full time security leader.
Core Services
SecureLeap provides practical support across the entire SOC 2 journey:
- SOC 2 readiness assessments to identify gaps and create remediation roadmaps
- Control design and implementation tailored to cloud native startups
- Virtual CISO leadership for ongoing security guidance without full time headcount
- Policy drafting that reflects how your team actually operates
- Evidence management and coordination with CPA audit firms
- Risk assessment and risk management program development
Compliance Automation Integration
SecureLeap helps implement and manage compliance automation platforms like Drata, Vanta, and Secureframe. Integration with your existing cloud stack (AWS, Azure, GCP, GitHub, GitLab) enables automated evidence collection and operational effectiveness monitoring throughout your audit period.
Bundled Solutions
Enterprise customers often require both a SOC 2 report and an annual application or API penetration test. SecureLeap bundles these services together, handling both your compliance preparation and your technical security validation in a coordinated engagement.
Getting Started
SecureLeap offers free SOC 2 audit readiness consultations for startup CEOs and CTOs. During this call, you will receive:
- Custom timeline based on your deal deadlines
- Recommended Trust Services Criteria for your market
- Scope recommendations based on your infrastructure
- Estimated budget range for your specific situation
Schedule your consultation to validate your assumptions about scope and avoid over engineering controls that do not match your actual risk profile or customer requirements.
Next Steps for Startup Founders Planning a SOC 2 Audit
Turning this guide into action requires a few immediate moves. Here is your checklist for this week.
Immediate Actions
- Identify your executive sponsor (usually CEO or CTO for early stage companies)
- Choose your desired SOC 2 type (Type 1 or Type 2) and target timeline
- Inventory your core systems: cloud accounts, identity providers, code repositories, and critical SaaS tools
- Ask your key customers or prospects which Trust Services Criteria they expect to see
Validate Your Approach
Book a discovery call with a specialist like SecureLeap to validate assumptions about scope. External perspective helps you avoid two common mistakes: under scoping in ways that leave customer requirements unmet, or over engineering controls that waste time and budget.
Set Up Project Tracking
Create a simple internal SOC 2 project board in tools like Jira, Asana, or Notion. Organize work into tracks for:
- Policies (drafting, review, approval)
- Technical controls (implementation, testing)
- Evidence (collection, organization, gaps)
- Vendor management (inventory, reviews, documentation)
Assign owners to each track and establish a weekly check in cadence to maintain momentum.
Final Thoughts
Early stage SaaS companies routinely reach their first SOC 2 report within one year when they follow a structured workflow and assign clear ownership. The path from zero compliance to a clean SOC 2 Type 2 report is well traveled, and thousands of startups before you have completed this journey successfully.
Your future enterprise customers expect you to protect their data with the same rigor they apply internally. SOC 2 compliance demonstrates that commitment and transforms security from a sales blocker into business intelligence that accelerates your growth.
Start your readiness assessment today, and you will be sharing your SOC 2 report with prospects by your target deadline.
FAQ SOC2 Audit
What is the difference between SOC 2 Type 1 and Type 2?
Type 1 evaluates control design at a single point in time, while Type 2 evaluates both design and operating effectiveness over 3-12 months. Enterprise customers strongly prefer Type 2 because it proves your controls actually worked over a period of time.
How much does a SOC 2 audit cost for a startup?
A Type 2 audit typically costs between $8,000 and $12,000 in fees. Total costs including readiness consulting, automation tools, and penetration testing often range from $20,000 to $50,000 depending on scope.
How long is the timeline for a SOC 2 Type 2 report?
The end-to-end process usually takes 6-15 months. This timeline includes 4-8 weeks of preparation followed by a mandatory 3-12 month observation period and final fieldwork.
Which Trust Services Criteria are required for SOC 2?
The Security criteria is the only mandatory category for every SOC 2 report. Organizations can optionally add Availability, Confidentiality, Processing Integrity, or Privacy based on their specific product and customer requirements.
Why do enterprise customers require a SOC 2 report?
It provides standardized proof that a vendor manages customer data responsibly and maintains proper security controls. A clean report allows procurement teams to skip long security questionnaires and move straight to contract negotiation.


%20(10)%20(1).png)

%20(4)%20(1).avif)
%20(3)%20(1).avif)