Startups live by the mantra “move fast and break things.” It is the engine of innovation. However, in the digital age, you want to be the one breaking your own things before a malicious actor does it for you.
Security is no longer just a technical requirement; it is a sales enabler. If you are selling B2B software, your customers—especially enterprise clients—will demand proof that their data is safe. This is where the Pentest (Penetration Test) comes in.
Penetration testing is a method for gaining assurance that your systems are secure and your customers' data is protected by uncovering vulnerabilities and validating the effectiveness of your security measures.
This guide is designed for non-technical founders and first-time buyers. We will demystify the process, explain why it is critical for your bottom line, and show you how to conduct one effectively without burning your runway.
Part 1: What Exactly is a Pentest?
Think of a penetration test as a digital fire drill.
If you wanted to know if your office was safe from burglars, you could hire a security consultant to try and break in. They might try to pick the lock, climb through a window, or talk their way past the receptionist. If they succeed, they tell you exactly how they did it so you can fix that specific weakness.
A pentest is the exact same process, but it's a simulated attack on your software and network.
The Core Definition: Simulated Attack
A penetration test is an authorized, simulated cyberattack on your computer system, performed to evaluate the security of the system. Penetration tests involve executing simulated cyberattacks to identify vulnerabilities in systems and networks.
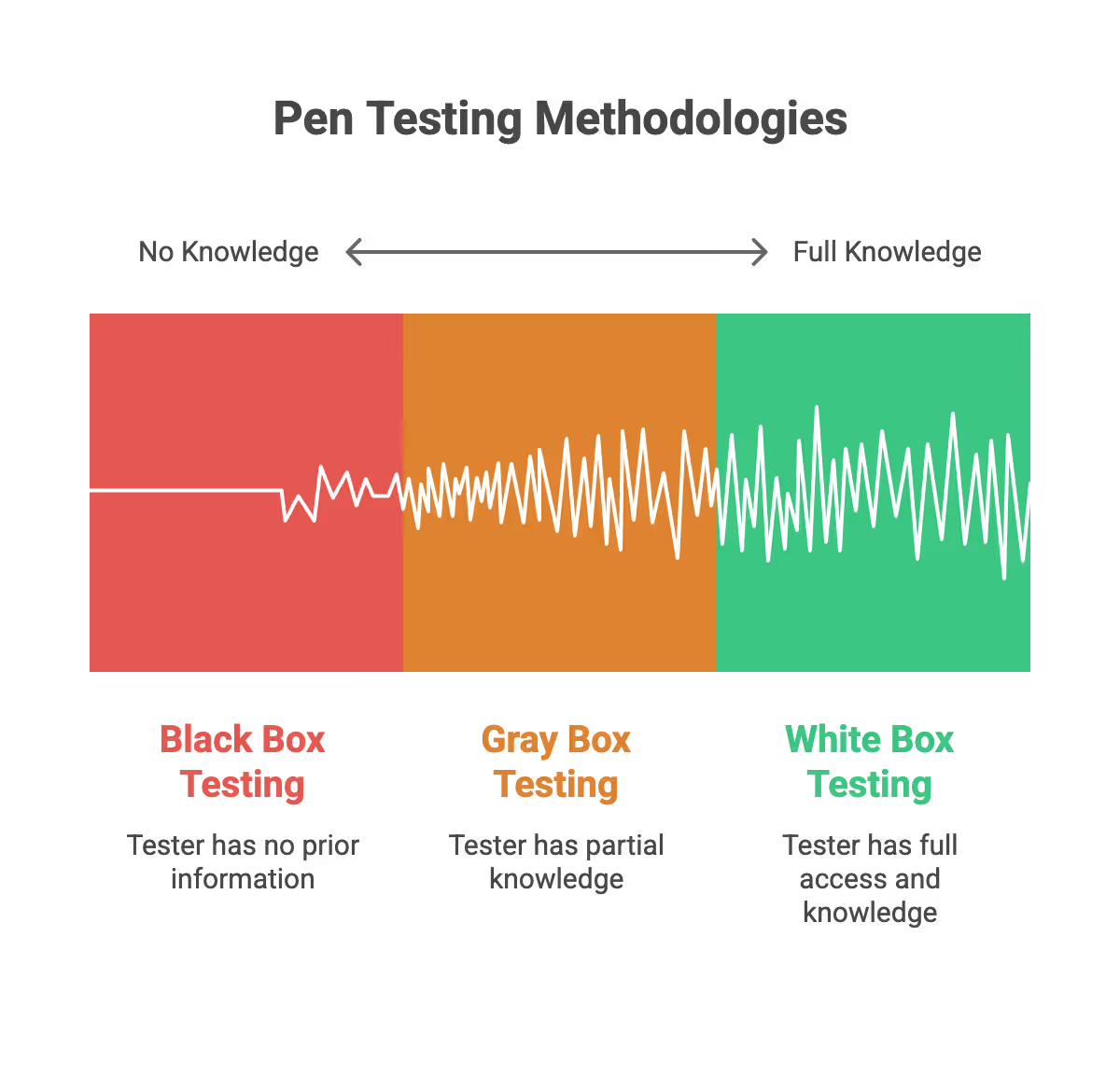
The Three Flavors of Pentesting
Not all tests are created equal. Depending on what you are building and how much information you want to give the testers, you will choose one of three approaches:
- The Scenario: The tester acts like a real-world hacker with no prior knowledge of your system and attempts to breach the target system from an external perspective.
- The Goal: To simulate an external attack from a stranger.
- The Pros: It reveals what a hacker can do from the outside.
- The Cons: It can be time-consuming and might miss internal vulnerabilities that are easily exploitable once inside.
White Box Testing
- The Scenario: The tester is given full access—source code, architecture diagrams, and admin credentials—to the target system.
- The Goal: To find every possible flaw, including deep logic errors in the code.
- The Pros: This is the most thorough and comprehensive test.
- The Cons: It takes the longest and is usually the most expensive.
Grey Box Testing (The Startup Sweet Spot)
- The Scenario: The tester has partial knowledge, such as user credentials and basic documentation, but not full source code access.
- The Goal: To simulate an attack by a user on the platform or an insider threat. This approach can also simulate an internal test, where the tester acts as a trusted insider to identify vulnerabilities within the target system.
- The Pros: It balances speed and depth. This is usually the best return on investment for startups.
Part 2: The "Why" – Beyond Just Security
As a founder, you have a million places to spend capital. Why spend it on hackers?
For startups, a pentest is rarely just about security. It is a strategic business asset. Penetration testing helps protect your company's reputation by demonstrating a commitment to security, which is crucial for maintaining customer trust and minimizing the risk of reputational damage from data breaches.
1. Unblocking Enterprise Sales
If you are selling upstream to larger companies, their Vendor Risk Management (VRM) team will send you a security questionnaire. One of the top questions is always: "When was your last third-party penetration test?"
- Having a clean report ready to share shortens sales cycles.
- It signals maturity and reliability.
2. Achieving Regulatory Compliance
You cannot scale without compliance. Most major frameworks require regular pentesting:
- SOC 2 Type II: Requires an annual pentest.
- ISO 27001: Mandates vulnerability management and testing.
- HIPAA: Essential if you handle health data.
- PCI-DSS: Mandatory if you process credit card payments.
3. Protecting Valuation and Reputation
A data breach in the early stages of a startup can be a death sentence.
- Investors view security incidents as a sign of poor governance.
- Customers lose trust instantly.
- The cost of remediation often exceeds the cost of prevention by a factor of ten.

Part 3: Pentest vs. Vulnerability Scan – Do Not Get Fooled
This is the most common pitfall for first-time buyers. You must understand the difference to avoid buying a “fake” pentest.
A vulnerability assessment is often automated and may not provide the depth of a manual penetration test. Vulnerability scanning uses automated tools to quickly identify known security issues, but these tools can generate false positives, which may lead to unnecessary remediation efforts. I
In contrast, manual penetration testing goes beyond automated scans by simulating real-world attacks, validating findings, and reducing the occurrence of false positives for a more accurate evaluation of your security posture.
Vulnerability Scanning
- What it is: An automated software tool (like a robot) runs through your code looking for known issues.
- How it works: It matches your software version against a database of known bugs.
- The output: A long list of potential issues, many of which might be false alarms.
- Analogy: Like running a spellcheck on a document. It catches typos, but it cannot tell you if the plot makes sense.
Penetration Testing
- What it is: A human expert (or team) using tools and creativity to find vulnerabilities and logic flaws that automated scans might miss.
- How it works: The human attempts to chain together small issues to create a major breach.
- The output: A curated report of verified risks with proof-of-concept evidence.
- Analogy: Like hiring a professional editor. They check the flow, the logic, and the narrative.
Key Takeaway: If a vendor promises a “full pentest” for $500 and delivers it in 2 hours, you just bought a vulnerability scan. Do not submit this to a serious enterprise client; they will reject it.
Part 4: How to Effectively Conduct a Pentest
Running a pentest involves more than just signing a contract. To get value, you need to manage the lifecycle effectively. An effective pen testing process involves several key steps, from planning and scanning to remediation, ensuring a structured approach to identifying vulnerabilities and strengthening your security posture.
Step 1: Define Your Scope
You cannot test “everything.” You need to tell the testers exactly what is in bounds.
- Identify Critical Assets: What is your crown jewel? (e.g., The database, the payment gateway, the user login). These are the components of your system's defenses that are most important to protect.
- URLs and IPs: List the specific web addresses and API endpoints to be tested.
- Exclusions: explicitly state what they should not touch (e.g., a third-party chat widget or a legacy server that is being decommissioned).
Step 2: Choose the Right Environment
Never test in Production if you can avoid it.
- The Risk: Testers might accidentally crash your server, delete data, or flood your support team with test emails.
- The Solution: Set up a Staging Environment.
- The Requirement: Ensure Staging is an exact mirror of Production (same code, same infrastructure) so the results are valid.
Step 3: Select the Right Vendor and Penetration Testing Tools
Don't just Google "cheap pentest." Look for credentials.
- Certifications: Look for testers with OSCP (Offensive Security Certified Professional) or CREST certifications.
- Sample Reports: Ask to see an anonymized report. Is it readable? Does it explain how to fix the bugs?
- Specialization: If you are a Blockchain startup, hire a Blockchain specialist. If you are a mobile app, hire mobile experts.
Step 4: The Testing Window
- Communication: Create a shared Slack channel or email thread with the testers.
- Whitelisting: Tell your engineering team to “whitelist” the testers’ IP addresses on the company's firewall. You don’t want your firewall to block them immediately; you want to see if they can break the application, not test the effectiveness of the firewall.
- Monitoring: Have your team monitor logs to see if they can detect the attack. This tests your defensive capabilities.
Step 5: The Report and Remediation
The test ends with a report. This is not the end of the job; it is the beginning of the work.
- Triage: The report will rank issues (Critical, High, Medium, Low).
- Prioritize: You must fix Critical and High issues immediately, with critical security vulnerabilities addressed as a top priority to prevent exploitation.
- Assign: Create tickets in Jira (or your project management tool) for every valid finding.
Step 6: The Retest
This is crucial. Once you fix the bugs, you must ask the vendor to verify the fixes.
- Most reputable vendors include one free retest in the price.
- This results in a "Clean Report" or "Letter of Attestation" which states that known vulnerabilities have been remediated.
- This is the document you send to your enterprise customers.

Mobile Device Security in Pentesting
Mobile devices have become crucial to business operations but also introduce unique security risks that can compromise sensitive data. Mobile device penetration testing goes beyond evaluating just the apps—it simulates attacks on mobile applications, the devices themselves, and their network connections. Security professionals assess vulnerabilities such as insecure data storage, weak encryption, poor authentication, and the effectiveness of mobile device management (MDM) and mobile application management (MAM) solutions to prevent unauthorized access and data leakage. By identifying and addressing these weaknesses, organizations can reduce the risk of data breaches, protect sensitive information, maintain customer trust, and meet compliance requirements, making regular mobile device pen testing an essential proactive measure for startups and SMBs.
Cloud and IoT Security in Pentesting
As more organizations move their operations to the cloud and adopt IoT devices, the landscape of potential security vulnerabilities grows. Pen testing for cloud environments involves simulating real world attacks on cloud-based infrastructure, platforms, and web applications to uncover new vulnerabilities that could lead to data breaches or unauthorized access. Security experts assess everything from misconfigured storage buckets to weak access controls, ensuring that your cloud systems are resilient against evolving threats.
IoT pen testing focuses on the security of connected devices,ranging from smart sensors to industrial control systems, by identifying exploitable vulnerabilities such as weak passwords, outdated firmware, and insecure communication protocols. These devices often serve as entry points for attackers seeking to compromise your broader IT system.
Part 5: Best Practices for Startups
To maximize the return on your investment, follow these golden rules.
Startups can choose from a range of penetration testing services to meet their specific needs and budgets, ensuring they identify vulnerabilities and strengthen their cybersecurity posture effectively.
1. Pentest Before You Need To
Do not wait until a client is demanding the report to sign a contract.
- Pentesting takes 1–2 weeks.
- Remediation takes 1–3 weeks.
- Retesting takes 1 week.
- Total lead time: 4–6 weeks. Plan accordingly.
2. Embrace "Pentest as a Service" (PtaaS)
Traditional consulting firms charge high hourly rates and deliver a PDF. Modern PtaaS platforms offer:
- Real-time viewing of findings as they are discovered.
- Integration with Jira/GitHub.
- Direct chat with the ethical hackers, where the testing team works closely with your developers to address findings in real time.
- This model fits the agile workflow of a startup much better than the “waterfall” consulting model.
3. Focus on Logic, Not Just Syntax
Ensure your testers understand your business logic.
- Example: A scanner knows if your SSL certificate is expired.
- Business Logic: A human needs to test if User A can see User B's invoices by simply changing the ID number in the URL (IDOR vulnerability).
- Action: Give the testers a demo of your product before they start so they understand how it should work.
4. Clean Your Code First
Don't pay an expensive consultant to find bugs you already know about.
- Run free, open-source automated scanners internally first.
- Fix the low-hanging fruit.
- Let the paid professionals focus on the complex, hard-to-find issues.
5. Create "Test Users"
Do not force testers to create their own accounts.
- Pre-provision accounts with different roles (e.g., Admin, Editor, Viewer).
- This allows testers to check for "Privilege Escalation" (can a Viewer become an Admin?).
Part 6: Common Pitfalls and Issues to Avoid
Even smart founders make mistakes when buying security services. Failing to follow best practices can lead to unresolved security issues that put your business at risk. Here is what to avoid.
Pitfall 1: Scope Creep (or Scope Shrink)
- The Issue: You forget to include your new mobile API in the test.
- The Result: You get a clean report, but your biggest risk surface was never checked.
- Avoidance: maintain an up-to-date asset inventory and review it with the vendor before signing.
Pitfall 2: The "One and Done" Mentality
- The Issue: Treating security as a checkbox. You do it once and forget it.
- The Result: You release new code next week that introduces a massive bug, but you aren't testing again for a year.
- Avoidance: Implement continuous scanning and schedule a manual pentest at least annually, or after any major product release.
Pitfall 3: Ignoring "Low" and Critical Security Vulnerabilities
- The Issue: Fixing only the “Critical” bugs and ignoring the “Low” ones to save time.
- The Result: Hackers often chain together three or four “Low” vulnerabilities to create a “High” impact attack.
- Avoidance: Create a roadmap to address all findings eventually, even if the timeline for low risks is longer. This helps prevent attacker lateral movement within your network, reducing the risk that minor vulnerabilities are exploited to move sideways after an initial breach.
Pitfall 4: adversarial Relationships
- The Issue: Your developers take the report personally and get defensive. "That's not a bug, that's a feature!"
- The Result: Friction between teams and slow fixes.
- Avoidance: Frame the pentest as a learning opportunity. Celebrate the catch. "Better we found it than a bad guy."
Pitfall 5: Testing on Production during Peak Hours
- The Issue: Running heavy automated scanning tools on your live app on Black Friday.
- The Result: Your site goes down, and you lose revenue.
- Avoidance: As mentioned, use Staging. If you must test Production, schedule it during your lowest traffic windows (e.g., 2 AM - 6 AM).
Part 7: The Economics of Pentesting
Understanding the cost structure helps you budget effectively. The cost of a pentest can vary depending on the penetration testing tools and methodologies used, as more advanced tools and techniques may increase both accuracy and price.
What Drives the Cost?
- Complexity: A simple marketing site is cheap. A complex fintech app with 50 user roles is expensive.
- Lines of Code / Endpoints: More API endpoints mean more hours required to test.
- Methodology: White box is more expensive than Grey box.
- Brand: A "Big 4" accounting firm will charge 3x more than a boutique security firm for the same (or sometimes worse) work.
Typical Startup Budgeting
- Seed Stage: You might get away with automated scanning and a very small, targeted pentest ($4k - $6k).
- Series A: You need a full comprehensive pentest for compliance ($10k - $25k).
- Series B+: You will likely need continuous testing and multiple assessments ($30k+ annually).
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.
FAQ What is Pentest
What is a penetration test?
A penetration test is an authorized, simulated cyberattack on a computer system to evaluate its security. It involves human experts using tools to identify and validate vulnerabilities that automated scans might miss.
What is the difference between a pentest and a vulnerability scan?
A vulnerability scan is an automated tool that catches known bugs, while a pentest is a manual assessment by human experts. Pentesters can chain multiple small issues together to find complex security flaws that automated robots cannot detect.
Which compliance frameworks require a penetration test?
Major frameworks like SOC 2 Type II, ISO 27001, and HIPAA require regular penetration tests. These assessments provide proof to enterprise clients that your security measures are effective and data is protected.
How much does a penetration test cost for a startup?
Costs vary based on complexity, but a seed stage startup might spend $4,000 to $6,000 for a targeted test. For Series A companies requiring full compliance, the cost generally ranges from $10,000 to $25,000.
Why is grey box testing recommended for startups?
Grey box testing balances speed and depth by giving testers partial knowledge of the system, such as user credentials. This approach provides the best return on investment by simulating attacks from a trusted insider or registered user.


%20(16)%20(1).avif)

%20(13)%20(1).avif)
%20(7)%20(1).avif)