Building a startup is like building a high-performance race car. You spend months engineering the engine (your product), polishing the chassis (your UI/UX), and securing the best drivers (your team). But before you take that car onto the track at 200 mph, you need to crash-test it. You need to know if the wheels will fly off under pressure or if the brakes will fail at a critical moment.
In the digital world, this crash test is called Penetration Testing (also commonly referred to as "pen testing" or "pentesting").
For many non-technical founders, security often feels like an afterthought or a box to check for compliance. However, in an era where data breaches can bankrupt a young company overnight, understanding the types of penetration testing is not just a technical requirement. It is a survival skill.
This guide will walk you through the landscape of penetration testing. We will explore what it is, the specific types relevant to startups, and the best practices to ensure you get the most value out of your investment.
What is Penetration Testing?
At its simplest, penetration testing is a simulated cyberattack against your computer system to check for exploitable vulnerabilities. Unlike a real attack, this is performed by ethical hackers (the “good guys”), also known as pen testers, who you pay to find the holes in your defense before the “bad guys” do. Pen testers often use manual testing techniques to uncover vulnerabilities that automated tools might miss.
The goal is to identify weak spots in your:
- Software applications
- Cloud infrastructure
- Networks
- User behaviors
For a startup, a pentest is a sanity check. It answers the question: Are we actually as secure as we think we are?
Why Startups Cannot Ignore This
You might think you are too small to be a target. This is a dangerous myth. Automated bots scour the internet 24/7 looking for easy targets, regardless of company size. Furthermore, your growth depends on trust.
Here is why pentesting is non-negotiable for modern startups:
- Building Customer Trust: Enterprise clients will often refuse to sign contracts unless you can prove your security posture. A clean pentest report is a sales asset.
- Regulatory Compliance: Frameworks like SOC 2, ISO 27001, HIPAA, and GDPR often mandate regular security assessments.
- Investor Confidence: During due diligence, savvy investors want to see that you have mitigated technical risk.
- preventing Costly Rewrites: Finding a security flaw early in the development cycle is significantly cheaper than fixing it after you have scaled.
The Methodologies: The Colors of Testing
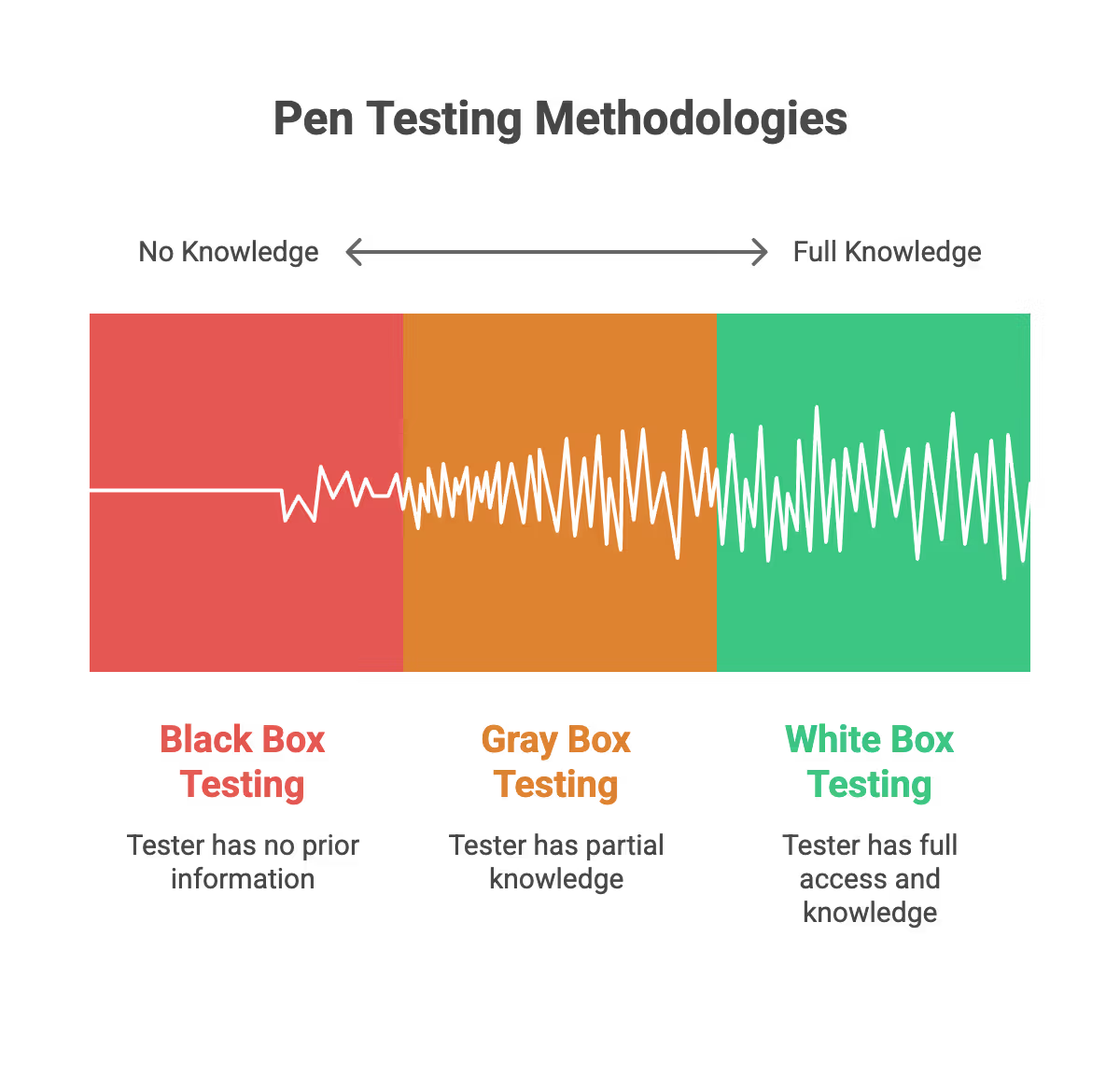
Before we dive into the specific types of systems you can test, you need to understand the perspective of the test. In the industry, we define these perspectives using “box” terminology. Box penetration testing refers to different approaches based on how much knowledge the tester has about the target environment, ranging from no prior information (black-box), partial knowledge (gray-box), to full access (white-box).
1. Black Box Testing
This is the “real-world” simulation. The tester is given zero prior knowledge of your internal systems. They approach your startup exactly like an external hacker would. This approach is known as black box penetration testing.
- The Goal: To see what an outsider can do with no insider information. Black box penetration testing simulates the actions of an external attacker attempting initial access to the target environment.
- The Pros: Simulates a realistic external attack scenario.
- The Cons: It can be time-consuming and might miss internal vulnerabilities that aren’t immediately visible from the outside.
2. White Box Testing
This is the “insider” view. The tester is given full access to your source code, architecture diagrams, and user credentials. This approach is called white box penetration testing.
- The Goal: To find every possible bug and uncover all potential vulnerabilities, including those related to operating systems and internal logic.
- The Pros: Extremely thorough; identifying issues that black box tests might miss.
- The Cons: It is often more expensive due to the time required to analyze code.
3. Gray Box Testing
This is the “user” view and usually the sweet spot for startups. This approach is also known as grey box testing or grey box penetration testing. The tester has some knowledge (like user login credentials or high-level diagrams) but not full code access.
- The Goal: To simulate an attack by a malicious user or an attacker who has breached the perimeter. Grey box penetration testing is designed to simulate attacks by an insider threat or a user with partial knowledge of the system.
- The Pros: balances depth and efficiency.
- The Cons: Requires careful scoping to define what information is shared.
Core Types of Penetration Testing for Startups
Not all pentests are created equal. Depending on your product, whether it is a mobile app, a SaaS platform, or an internal tool, you will need different types of testing. Comprehensive penetration testing should cover network infrastructure, network services, and include vulnerability assessments to ensure all aspects of security are addressed.
Here are the specific categories you need to know:
1. Web Application Penetration Testing
If you are a SaaS startup, this is likely your top priority. This test focuses on the application delivered via a web browser. A web application penetration test is designed to identify vulnerabilities in web applications, web apps, and the underlying web servers. Testers look for logical errors, injection flaws, and broken authentication.
What they test for:
- SQL Injection: Can an attacker trick your database into revealing private data?
- Cross-Site Scripting (XSS): Can an attacker inject malicious scripts to hijack user sessions?
- Broken Authentication: Can a user force their way into another user’s account?
Why startups need it:
- Your web app is your storefront. It is the most exposed part of your business.
- Most data breaches occur through web application vulnerabilities.
2. Cloud Penetration Testing (AWS, Azure, GCP)
Most startups today are “cloud-native,” meaning they do not own physical servers but rent infrastructure from Amazon (AWS), Google (GCP), or Microsoft (Azure). Cloud pentesting is distinct from web app testing; it focuses on the infrastructure hosting your app.
What they test for:
- Misconfigured S3 Buckets: Are your file storage folders accidentally left open to the public?
- IAM Roles: Do your developers have “God mode” permissions they do not need?
- Security Groups: Are your firewalls allowing traffic from dangerous sources?
Why startups need it:
- The Shared Responsibility Model: Cloud providers secure the cloud (the hardware), but you must secure what is in the cloud (your data and configs).
- Cloud penetration testing is essential for uncovering vulnerabilities and security holes that may be present in your cloud infrastructure due to misconfigurations or lack of experience.
- One simple misconfiguration can expose your entire database to the internet.
3. API Penetration Testing
Modern applications are built on APIs (Application Programming Interfaces). These are the bridges that allow different software components to talk to each other. Even if your web interface is secure, a weak API can be a backdoor.
What they test for:
- BOLA (Broken Object Level Authorization): Can User A simply change an ID number in the URL to see User B's data?
- Rate Limiting: Can an attacker flood your API with millions of requests to crash your service?
- Data Exposure: Is the API sending back more data than the app actually displays?
Why startups need it:
- APIs are often the favorite target for automated bots.
- Mobile apps and single-page applications rely heavily on APIs, making them a critical failure point.
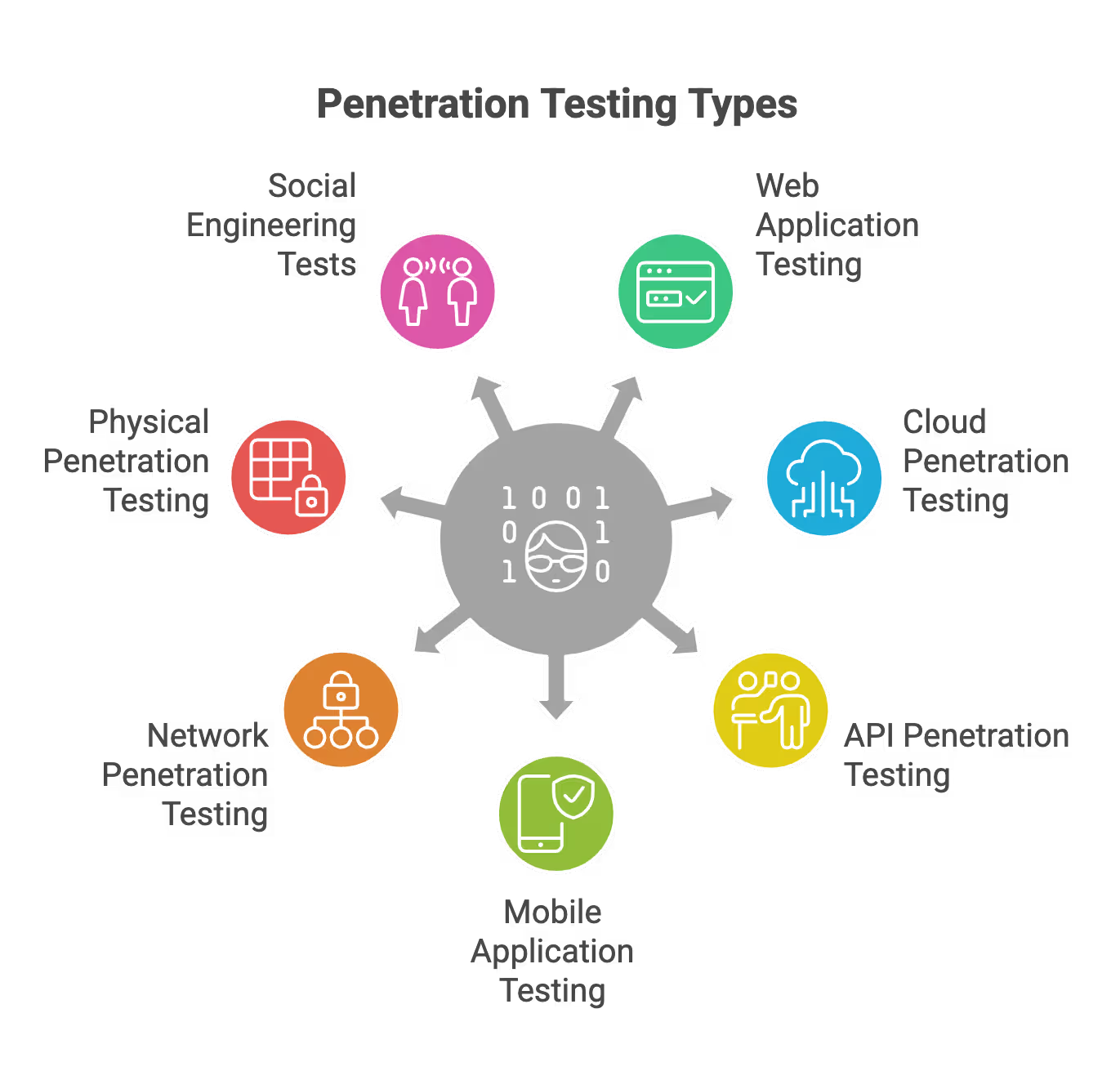
4. Mobile Application Penetration Testing
If your primary product is an iOS or Android app, you need specialized testing. Mobile apps have unique attack vectors involving data storage on the device and communication with the server.
What they test for:
- Insecure Data Storage: Is the app saving passwords or tokens in plain text on the user’s phone?
- Reverse Engineering: Can a competitor or hacker decompile your app to steal your intellectual property?
- Hardcoded Secrets: Did a developer accidentally leave an API key inside the app code?
- Weak Authentication: Does the app use insecure login mechanisms, such as poor password policies, lack of multi-factor authentication, or weak session management, making it easier for attackers to gain unauthorized access?
Why startups need it:
- App Stores (Apple and Google) are increasingly demanding stricter security standards.
- Mobile devices are easily lost or stolen; your app must remain secure even if the device is compromised.
5. Internal and External Network Penetration Testing
This is the “classic” pentest.
- External Network: Focuses on your internet-facing assets (IP addresses, firewalls, routers). This is known as an external penetration test, which evaluates your perimeter security from an outside attacker’s perspective.
- Internal Network: Assumes the attacker is already inside the building (or on the VPN) and tries to move laterally to find sensitive data. This is known as an internal penetration test, which assesses vulnerabilities within your corporate network and simulates lateral movement to uncover internal security gaps.
Why startups need it:
- If you have a physical office with servers, this is critical.
- Even for remote-first startups, testing the VPN and employee laptop configurations falls under this umbrella.
- Network penetration testing helps identify weaknesses in your network security and infrastructure, reducing the risk of cyber threats within your organization.
6. Physical Penetration Testing
Physical penetration testing is a vital but often overlooked part of a comprehensive security strategy for startups, focusing on evaluating the effectiveness of an organization's physical security controls by simulating real-world attempts to gain unauthorized access to facilities, systems, or sensitive data.
During such tests, security professionals employ techniques like lock picking, tailgating by following authorized personnel into restricted areas, and social engineering to bypass physical barriers and uncover weaknesses such as unsecured server rooms, weak access controls, or easily bypassed entry points. Identifying these gaps allows organizations to strengthen their physical security posture proactively, ensuring that defenses are effective against determined attackers and aligned with overall risk management strategies, especially for startups handling sensitive customer data or intellectual property.
7. Social Engineering Tests
No matter how robust your technical defenses are, the human element remains one of the most significant vulnerabilities in any organization’s security posture. Social engineering tests are a specialized form of penetration testing designed to assess how susceptible your team is to manipulation and deception. In these tests, penetration testers use tactics like phishing emails, pretexting by posing as trusted individuals, and baiting by leaving infected USB drives in common areas to try to trick employees into revealing sensitive information or granting access to internal systems.
The objective is to simulate real-world social engineering attacks and identify where your staff might inadvertently compromise security. Social engineering tests provide valuable insights into your organization’s human security layer, highlighting areas where additional training or awareness is needed. By regularly conducting social engineering tests, startups can ensure their employees are prepared to recognize and resist the latest social engineering tactics, reducing the risk of data breaches and unauthorized access.
Best Practices for Startups
Navigating the vendor landscape can be overwhelming. To ensure you get a high-quality assessment without burning your runway, follow these best practices.
Penetration testing should be performed regularly—at least annually or after significant changes to your infrastructure—to maintain your organization's security and meet security regulations. This proactive approach helps startups stay compliant and ensures that security controls are effective against evolving threats.
Define Your Scope Clearly
You do not need to test everything at once. "Scope" refers to the specific assets (IP addresses, URLs, code repositories) that the testers are allowed to attack.
- Prioritize Critical Assets: Focus on the systems that hold customer PII (Personally Identifiable Information) or payment data.
- Exclude Marketing Sites: Your static WordPress marketing blog usually does not need a full enterprise-grade pentest. Focus on the product.
- Production vs. Staging: ideally, test on a "Staging" environment that mirrors production. This prevents the testers from accidentally crashing your live site or deleting real user data.
Choose the Right Timing
Don't pentest too early, but don't wait too long.
- Too Early: If you are still building the MVP and the code changes daily, a pentest is a waste of money.
- The Sweet Spot: Schedule the test when your product is feature-complete and stable, but before a major public launch or a compliance audit window.
Verify the Methodology
Ensure your vendor uses a human-led approach.
- Ask for Credentials: Look for certifications like OSCP (Offensive Security Certified Professional) or CREST.
- Sample Reports: Ask to see an anonymized report. It should contain a narrative of how they got in, not just a list of computer output.
Prepare for Remediation
The pentest doesn't end when you get the report. That is actually when the work begins.
- Triage: You will likely receive a list of "High," "Medium," and "Low" severity issues. Fix the Highs immediately.
- Retesting: Negotiate a "retest" window with your vendor. Once you fix the bugs, they should verify the fixes are effective at no extra massive cost.
Common Pitfalls to Avoid
Founders often make avoidable mistakes when purchasing their first pentest. These errors can lead to a false sense of security or wasted budget.
1. Confusing Vulnerability Scans with Pentests
- Vulnerability Scan: An automated tool runs for 20 minutes and lists potential issues. It is cheap and fast but produces many false alarms and misses logic bugs.
- Penetration Test: A human expert uses tools + creativity to simulate a complex attack chain.
- The Pitfall: Buying a cheap "pentest" for $500 that is actually just an automated scan. If you are doing this for compliance (SOC 2), an automated scan often will not satisfy the auditor.
2. "Set It and Forget It" Mentality
Security is a state of being, not a destination.
- The Reality: New vulnerabilities are discovered every day. Your code changes every week.
- The Solution: Treat pentesting as an annual or bi-annual exercise, not a one-time event.
3. Scope Creep (or Scope Shrink)
- Scope Creep: Adding too many assets to the test midway through, blowing up the budget.
- Scope Shrink: Deliberately hiding parts of the system from testers because you know they are weak. This defeats the purpose. You are paying them to find the bad stuff so you can fix it.
4. Ignoring the "Low" Severity Findings
It is easy to fix the critical bugs and ignore the minor ones. However, hackers often chain together three or four "low" severity issues to create one massive "critical" exploit.
- Advice: Create a roadmap to address the lower-priority issues over time.
5. Failing to Notify Your Cloud Provider
While rules have relaxed, in some specific legacy setups or massive volume tests, triggering a high-volume attack against your AWS/Azure infrastructure without notice might trigger their automated defenses, or get your account flagged.
- Advice: Always check your cloud provider’s current policy on penetration testing permissions.
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.
FAQ Types of penetration testing
What is the difference between a vulnerability scan and a penetration test?
A vulnerability scan is an automated tool that identifies potential issues quickly. A penetration test is a manual assessment by human experts who simulate real world attacks to find complex security gaps.
Which penetration testing methodology is best for startups?
Gray box testing is often the best fit as it balances depth and efficiency. It simulates an attack by a user with partial knowledge of the system to identify internal risks.
How often should a startup perform penetration testing?
Startups should conduct tests at least annually or after significant changes to their infrastructure. This ensures security controls remain effective against evolving threats and meets compliance requirements.
Why is API penetration testing important for SaaS companies?
APIs are frequent targets for automated bots and serve as critical bridges between software components. Testing identifies issues like broken authorization and data exposure that web interfaces might miss.
Can penetration testing help with SOC 2 compliance?
Yes, many security frameworks like SOC 2 and ISO 27001 require regular security assessments. A clean report serves as evidence of a strong security posture for auditors and enterprise clients.


%20(16)%20(1).avif)

%20(13)%20(1).avif)
%20(7)%20(1).avif)