The right time to perform a penetration test is when your application or infrastructure has reached a functional and stable state, ideally just before moving to a production environment or embarking on a significant commercial milestone.
For a startup, this means finding the balance between a product that is mature enough to be tested effectively and a timeline that allows for security flaws to be remediated before they can be exploited or block a critical business deal.
It is often a mistake to wait for a perfect version of the software, as security should be integrated into the lifecycle once core features are operational but before the data of real users is at risk.

Introduction to Penetration Testing
Penetration testing, often referred to as pen testing, is a proactive security assessment where ethical hackers simulate real-world attacks on your computer systems, network infrastructure, or web applications. The goal is to identify vulnerabilities before malicious actors can exploit them, giving startups a clear picture of their current security posture.
For early-stage companies, penetration testing is a critical concern not just for protecting customer data and intellectual property but also for safeguarding the most critical assets that drive business operations and growth.
In today’s fast-moving digital environment, penetration testing for startups is essential. New risks and emerging vulnerabilities are discovered every day, and attackers are constantly evolving their tactics. Regular security testing helps startups stay ahead of these newly discovered threats, ensuring that sensitive data remains secure and that security measures are effective. By working with a trusted penetration testing provider, startups can benefit from expert guidance on how to identify vulnerabilities and remediate them quickly, reducing the risk of data breaches and regulatory penalties.
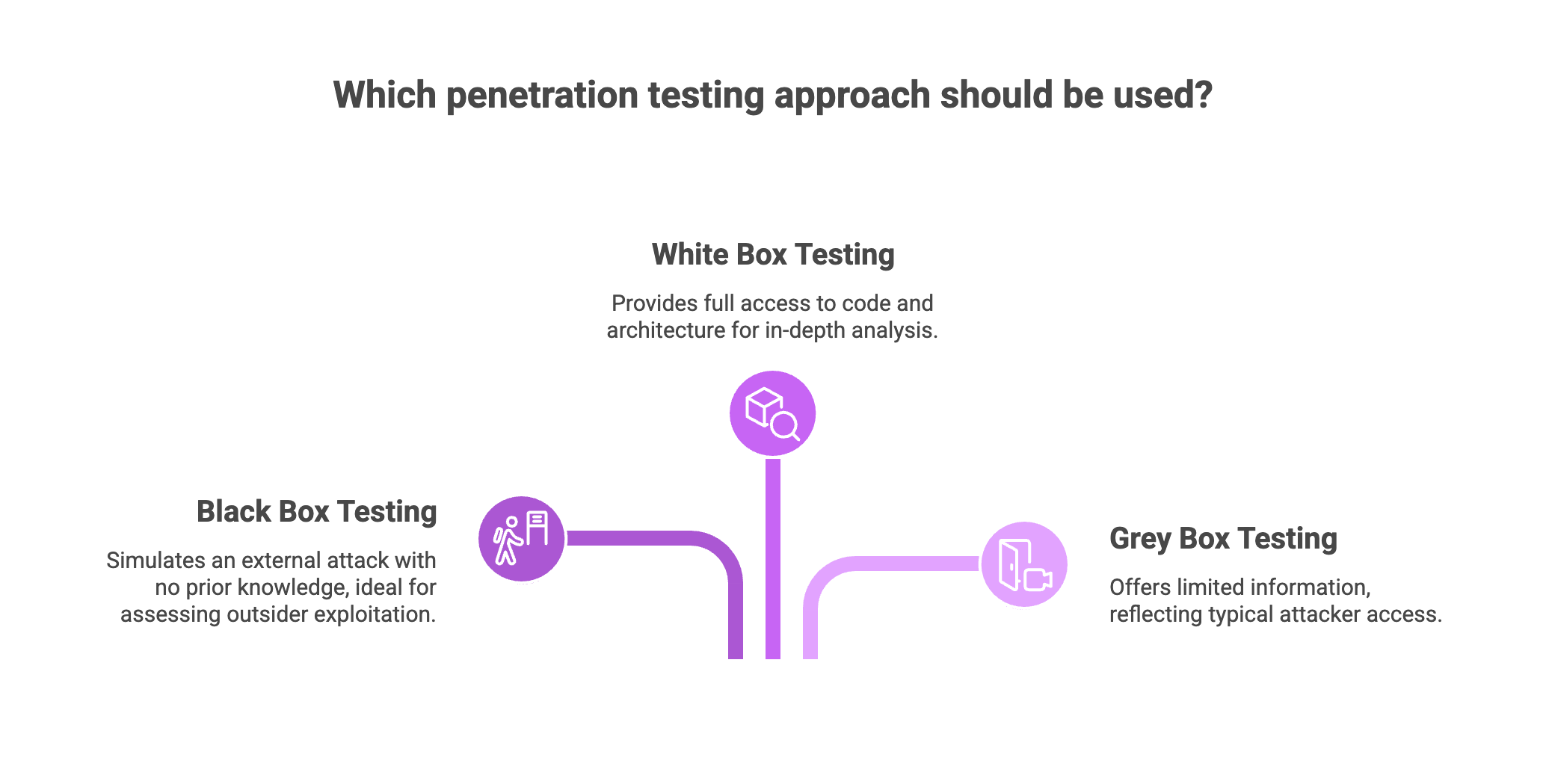
There are several approaches to penetration testing, each offering unique insights:
Black box testing simulates an external attack, where penetration testers have no prior knowledge of your internal systems: ideal for assessing how an outsider might exploit weaknesses.
White box testing, on the other hand, gives testers full access to your code and architecture, allowing for an in-depth analysis of security vulnerabilities.
Grey box testing strikes a balance, providing limited information to testers and reflecting the kind of access a typical attacker might gain through social engineering or partial compromise.
For many startups, grey box testing offers the most realistic and cost-effective way to uncover exploitable vulnerabilities across different growth stages.
By adopting a security-first approach and integrating penetration testing into the development process, startups can build customer trust, meet regulatory requirements, and demonstrate due diligence to potential investors and partners.
Our recommendation:
- Schedule penetration testing once your product reaches a stable, functional state.
- Avoid waiting for a perfect version; integrate security early after core features are ready.
- Choose the appropriate testing approach (black box, white box, or grey box) based on your startup’s needs.
- Partner with a trusted penetration testing provider experienced in startup environments.
- Implement continuous pentesting and regular security assessments to stay ahead of threats.
Navigating Different Growth Stages
During the development phase of a product, it is most effective to wait until the first version is relatively stabilized before carrying out a full penetration test. If the code is changing every hour, the results of a test will quickly become obsolete. Startups in the early stages are especially vulnerable due to limited resources and less mature security protocols, making it crucial to implement cybersecurity measures early on.
For projects with long development cycles, it is useful to conduct smaller security checks along the way as core features are completed.
Vulnerability scanning can serve as a proactive measure during development, helping to identify known weaknesses before a full penetration test is performed. This allows you to build on a healthy foundation and prevents the accumulation of security debt that would be much harder to fix later in the process.
When your company is planning a server migration or an infrastructure overhaul, the timing becomes a matter of priority. It is generally more valuable to test the new configuration rather than an old one that is about to be decommissioned. As part of your security assessment, it is important to include testing of external networks and web applications to ensure public-facing components are secure. However, you must consider the timeframe of the migration. If the old system will remain live for several months, the exposure risk might justify a quick audit to ensure you are not leaving an open door for attackers while you wait for the new setup to be ready.
After each penetration test, future planning is essential to guide ongoing security strategies, update documentation, and create a roadmap for continuous improvement.
Actionable Steps:
- Conduct vulnerability scans regularly during long development cycles.
- Perform smaller security checks as core features are completed.
- Schedule penetration tests after major infrastructure changes or migrations.
- Include external network and web application testing in your scope.
- Use post-test reports to update security policies and plan remediation.

Balancing Budget and Business Operations Priorities
A common misconception is that a penetration test is only for companies with massive budgets. For young startups, the right time to test is often when the first external users are onboarded, even if the budget is small. You can opt for a scoped audit that focuses on the most critical parts of the application, such as the authentication system or payment gateway.
Starting small and increasing the depth of testing as the company grows allows you to manage costs while still maintaining a proactive security posture. While annual pentests and quarterly pentesting are traditional approaches, a more strategic pentesting cadence is often needed for startups and small businesses to keep up with evolving threats. Startups penetration tests are crucial for early-stage companies and other organizations to identify vulnerabilities, protect assets, and ensure compliance before attackers can exploit weaknesses.
You may also find that the right time is dictated by your sales pipeline. Many startups wait for a client to request a security report before they act. This can be a dangerous delay that stalls a major contract. By performing a pentest proactively, you can use the resulting security certificate or summary as a sales tool.
When choosing a provider, it's important to select the right partner who understands the unique needs of startups and small businesses, including experience with mobile apps and modern tech stacks.
Best practices:
- Start with a scoped penetration test focusing on critical assets like authentication and payment systems.
- Gradually increase testing scope and frequency as your startup grows.
- Align penetration testing schedules with your sales and funding milestones.
- Use penetration test reports as part of your sales and compliance documentation.
- Choose providers familiar with startup challenges and modern technologies.
The Risks of Poor Timing for Startups Penetration Test
The risk of not performing a penetration test at the right time can be catastrophic for a new company. If a breach occurs because testing was delayed, the financial impact includes not only the cost of the investigation and recovery but also potential legal penalties. For a startup, these costs can easily exceed the total capital available, leading to a premature end for the business. Delayed penetration testing also increases the risk of data loss, which can have severe consequences for business continuity and customer trust.
Another significant risk is the loss of reputation. Trust is the most valuable currency for a startup. If you suffer a data leak early in your journey, it becomes incredibly difficult to convince future customers or investors that your platform is safe. Furthermore, waiting too long to test often reveals fundamental architectural flaws that are expensive and time consuming to fix. Cybersecurity assessments, including penetration testing for vulnerabilities like SQL injection, can help catch these issues early and identify weaknesses in web applications and APIs before they are exploited.
Catching these issues early ensures that your developers can spend their time building new features rather than rewriting old ones to patch security holes that should have been identified months prior.
Our recommendation:
- Schedule penetration testing early to avoid costly breaches and legal penalties.
- Prioritize testing to protect critical data and business continuity.
- Use penetration testing to identify architectural flaws before they escalate.
- Address vulnerabilities like SQL injection and API weaknesses proactively.
- Maintain customer trust by demonstrating a strong security posture from the start.
FAQ About Pentesting
When is the right time to perform a penetration test?
The right time is when your application or infrastructure reaches a stable state, ideally before moving to production. For startups, this means finding the balance between product maturity and business milestones.
Should startups wait for a perfect version of software before testing?
No, waiting for a perfect version is often a mistake. Security should be integrated once core features are operational but before real user data is at risk.
How can startups manage penetration testing on a small budget?
Startups can opt for a scoped audit focusing on critical areas like authentication or payment gateways. You can then increase the depth of testing as the company grows.
What are the risks of delaying a penetration test?
Delayed testing increases the risk of data breaches, legal penalties, and reputation loss. It may also reveal fundamental architectural flaws that are expensive to fix later.
Can a penetration test help with the sales process?
Yes, performing a pentest proactively allows you to use the security certificate as a sales tool. This helps meet client requests early and avoids stalling major contracts.
SecureLeap Penetration Testing Services for Startups
At SecureLeap, we understand the unique challenges startups face when it comes to cybersecurity. Our penetration testing services are specifically designed to meet the needs of seed-to-Series B startups and SMBs, providing comprehensive security assessments that align with your growth stage and resource constraints.
Whether you are preparing for SOC 2, ISO 27001, HIPAA, or PCI DSS compliance, our expert team delivers actionable insights to help you identify vulnerabilities, strengthen your security posture, and protect your critical data and intellectual property.
Our startup-focused pentest service includes:
- Tailored testing scopes that prioritize your most critical assets, such as authentication systems, payment gateways, and APIs.
- Flexible engagement models that fit your budget and timeline, allowing you to start small and scale testing efforts as your company grows.
- Integration with compliance goals to support audit readiness and demonstrate due diligence to potential investors and enterprise clients.
- Detailed, easy-to-understand reports that highlight exploitable vulnerabilities along with clear remediation guidance.
- Ongoing support and consultation to help you plan future security improvements and maintain a security-first culture.
By partnering with SecureLeap, startups gain access to seasoned penetration testers who combine technical expertise with a deep understanding of startup environments. Our goal is to empower you with the confidence and security needed to accelerate your business growth without compromising on compliance or customer trust.
Ready to secure your startup’s future? Schedule a free consultation with SecureLeap today and take the first step towards a stronger, more resilient security posture.


%20(16)%20(1).png)

%20(13)%20(1).avif)
%20(7)%20(1).avif)