Key Takeaways
- SOC 2 is the detailed, NDA protected report that enterprise security teams request during vendor assessments, while SOC 3 is a short public summary primarily used for marketing purposes on your website and in sales materials.
- For B2B SaaS startups handling customer data, SOC 2 almost always comes first because it is what procurement and security teams actually review before approving vendors.
- Both SOC 2 and SOC 3 rely on the same trust services criteria and the same underlying audit work performed by certified public accountants, but they differ significantly in level of detail and who can access them.
- SOC 3 reports cannot be issued without completing SOC 2 Type II work first, meaning there is no shortcut to getting only a SOC 3 for marketing.
- The decision between SOC 2 vs SOC 3 should be driven by customer requirements and business stage rather than assumptions about difficulty or prestige.
Introduction: Why SOC 2 vs SOC 3 Matters For SaaS Startups Now
If you run a SaaS company selling to businesses, you have probably noticed something shift in how prospects evaluate your product. Security questionnaires have become longer, more detailed, and increasingly specific about what documentation they expect. The question “Do you have a SOC 2 report?” now appears in nearly every enterprise security review.
Imagine this scenario:
Your Series A SaaS company is in late stage conversations with an enterprise prospect in 2026. The deal is worth six figures annually. Then their procurement team sends over a security questionnaire that specifically asks for a current SOC 2 Type II report covering the last 12 months. Without it, the deal stalls. This is not a hypothetical situation for most growing startups. It is the reality of selling into mid market and enterprise accounts today.
SOC 2 and SOC 3 are both defined by the AICPA and built on the trust services criteria, but they serve very different audiences and purposes. Understanding the key difference between these reports is essential for startup CEOs and CTOs who need to allocate limited resources wisely while still closing deals.
This article will compare SOC 2 vs SOC 3, walk through real world workflows, and give you a step by step path for what an early stage startup should do in its first 12 to 18 months. SecureLeap focuses on helping seed to Series B companies get audit ready for SOC 2 and decide whether a SOC 3 makes sense based on pipeline and customer pressure.
Quick Answer: Do I Need SOC 2 or SOC 3?
If you want the direct answer without reading further:
Almost every B2B SaaS startup that handles customer data needs SOC 2 first. Buyers, security teams, and procurement cannot rely only on a SOC 3 summary because it lacks the detailed information they need to evaluate your organization’s security controls.
SOC 3 is optional and is typically produced after a SOC 2 Type II audit, often in the second year of a security program when the company wants a public badge for its website. Think of SOC 3 as a marketing asset, not a sales requirement.
Here is a simple decision rule: if your largest prospects in 2025 and 2026 are asking for NDAs and detailed controls documentation, you need SOC 2. If they only want public proof of compliance for marketing purposes, SOC 3 is a nice to have that can come later.
SecureLeap offers short consultations to review your existing customer security requirements and help you decide if SOC 2, SOC 3, or both are needed in the next two quarters.
Foundations: What Are SOC 2 and SOC 3 Reports?
Both SOC 2 and SOC 3 are attestation reports under SSAE 18 issued by independent CPA firms. They focus on how well a service organization protects its systems and data. The service auditor evaluates whether the organization controls relevant to security actually work as described.
The core distinction lies in presentation. A SOC 2 report is a detailed description of systems, controls, tests, and results. It includes the auditor’s opinion, management’s assertion, a comprehensive system description, and complete documentation of testing procedures and test results.
A SOC 3 report is a brief high level overview designed for public distribution that excludes sensitive details about specific controls and exceptions.
Both reports assess service organizations against the five trust services criteria:
These criteria were updated in the 2017 TSC framework and remain in active use in 2026. For most cloud based startups, only the Security criterion is mandatory. The others are scoped in based on customer expectations and the nature of your product.
Neither SOC 2 nor SOC 3 is a legal requirement like HIPAA or PCI DSS can be for specific industries. However, they have effectively become commercial requirements for selling into mid market and enterprise prospective customers who need assurance about your company’s security practices.

SOC 2 Explained For SaaS Startups
A SOC 2 report is a restricted use report that describes your system, the control environment, the tests performed by the auditor, and any exceptions found. Unlike SOC 3 reports, it contains granular information about how your security controls function and whether they controls operated effectively during the examination period.
SOC 2 comes in two formats: Type I and Type II. For a growing SaaS company trying to sell to Fortune 500 customers, SOC 2 Type II is usually what security teams expect by the second or third year of sales. Type II reports demonstrate operational effectiveness over time, which gives customers expect confidence that your controls actually work consistently.
For startups in 2025 and 2026, common controls included in SOC 2 examinations include:
- Enforced SSO through Okta or Google Workspace
- MFA for all production access
- Quarterly vulnerability scans and annual penetration testing
- Formal incident response runbooks
- Access control policies with regular access reviews
- Encrypted data protection at rest and in transit
- Vendor oversight and third party risk management
CEOs and CTOs can use SOC 2 during enterprise deals by sharing the report under a non disclosure agreement with customer security teams. You can walk them through sections that relate to identity management, encryption, and vendor risk. The detailed descriptions in a SOC 2 report give customer CISOs and auditors what they need to complete their vendor assessment.
Five Step Workflow To Prepare For SOC 2
- Scope your systems: Define which applications, infrastructure, and business operations are in scope for the audit evaluates
- Select trust services criteria: Choose Security as your baseline, then add Availability, Confidentiality, Processing Integrity, or Privacy based on customer expectations
- Build policies: Document security policies, incident response procedures, and internal processes
- Implement monitoring tools: Deploy compliance automation platforms such as Drata, Vanta, or Secureframe to streamline evidence collection
- Run an internal readiness review: Identify gaps before the CPA audit begins
SOC 2 Type I vs SOC 2 Type II
The difference between these type ii reports is fundamentally about time. A SOC 2 Type I is a point in time assessment that evaluates whether your controls were designed correctly on a specific date. A SOC 2 Type II covers 3 to 12 months of operating history and tests whether those controls actually functioned throughout that period.
Many seed or early Series A companies start with a Type I to satisfy initial customer due diligence in as little as 8 to 12 weeks. This gives you something to share with prospects while you build toward the more comprehensive Type II.
Here is an example timeline for a startup targeting SOC 2 in 2026:
Type II is more valuable because it shows that controls actually ran over time. Evidence of recurring tasks such as quarterly access reviews, continuous logging, and regular vulnerability scanning is what procurement teams increasingly insist on. User entities and their auditors want proof that your company’s systems maintain security status consistently.
Make a deliberate plan for when to upgrade from Type I to Type II rather than waiting for a large prospect to demand it late in the sales cycle. That scramble costs more time and money than proactive planning.
SOC 3 Explained And How It Relates To SOC 2
A SOC 3 report is a general use report that relies on the same underlying audit work as SOC 2 but strips away sensitive details like individual control descriptions, testing procedures, and specific exceptions. It excludes sensitive details that could expose your security architecture to unnecessary risk if made public.
SOC 3 reports are designed to be shared publicly. You can post them as a downloadable PDF on your company website, attach them to marketing collateral, or include them in early stage sales conversations before NDAs are signed. This makes SOC 3 useful for marketing purposes and demonstrating compliance to non technical stakeholders.
To issue a SOC 3, the auditor still evaluates controls against the trust services criteria. In practice, most SOC 3 reports are associated with a SOC 2 Type II examination completed for the same period. You cannot get a meaningful SOC 3 without doing the SOC 2 level work first.
The typical content of a SOC 3 report includes:
- Management’s assertion about the service organization’s controls
- The auditor’s opinion on whether criteria were met
- A high level system description
- A statement that security (and possibly other categories) criteria were satisfied during the period
In 2025 and 2026, startups commonly use SOC 3 in several ways:
- Putting a SOC 3 badge in the website footer
- Linking the report from a Trust Center page
- Including it in early stage sales conversations before NDAs are signed
- Sharing in investor materials to signal operational maturity
Direct Comparison: SOC 2 vs SOC 3 For Startups
This section provides a head to head comparison tailored to a CEO or CTO deciding how to present security posture to customers in the coming two to four quarters.
The difference in intended audience drives everything else. SOC 2 is written for knowledgeable readers who need to assess whether the service organization’s internal controls adequately protect their financial data, client data, and sensitive data. SOC 3 targets prospective customers and the general public who want reassurance without technical depth.
From a workload perspective, SOC 3 does not usually require a separate audit project. It repackages the SOC 2 results into a public format. The main investment decision is whether to pursue SOC 2 in the first place.
When SOC 2 Is The Better Choice
SOC 2 should be your priority if any of these conditions apply:
- You sell a SaaS platform that stores PII or financial data
- Your target customers are enterprise or regulated industries
- Prospects send you 100+ question security questionnaires
- Master service agreements or security addenda specifically reference SOC 2
- You process payroll processing, financial reporting, or other sensitive business operations
Consider a fintech startup processing payment instructions that needs to convince banks to integrate. SOC 2 covering Security and Availability becomes essential. Or a healthtech vendor integrating with EHR systems needs SOC 2 controls aligned with HIPAA expectations to pass customer security reviews.
SOC 2 is frequently treated as table stakes by procurement teams in 2025 and 2026. Rather than viewing it as a compliance cost, treat it as a revenue enabler. A single six figure enterprise deal can more than pay back the audit and preparation effort.
SecureLeap can run a short readiness assessment to estimate how many controls are already in place and what incremental effort is required to reach SOC 2 audit readiness.
When SOC 3 Adds Real Value
SOC 3 is most useful once a company already has a solid SOC 2 program and wants to showcase its maturity to a wider audience without constantly gating the report behind NDAs.
Examples where SOC 3 provides clear value:
- A Series B SaaS company embeds a SOC 3 link in its Trust Center, marketing site, and investor materials
- Sales teams can quickly answer “what security certifications do you hold” with a public link
- Early stage conversations move faster because basic reassurance questions are already answered
- Marketing content can reference independent verification without complex approval workflows
SOC 3 will not satisfy the due diligence needs of a rigorous customer security team. But it can speed early conversations and reduce friction at the top of the sales funnel.
Once you see repeated inbound questions asking about your security certifications, consider adding SOC 3 as a one click answer you can safely share with anyone. SecureLeap can help design a simple workflow where sales uses SOC 3 for unauthenticated prospects and keeps SOC 2 reserved for late stage opportunities with NDAs signed.
Startup Playbook: How To Decide Between SOC 2 and SOC 3 In Practice
Deciding between SOC 2 vs SOC 3 comes down to practical business considerations, not abstract security debates. Here is a simple mental model for founders juggling many priorities.
Three Question Framework
- What do my top ten target customers expect? Review your recent security questionnaires. If they ask for detailed information about controls, you need SOC 2.
- How soon do I need to close enterprise deals? If major deals are expected in the next 6 to 12 months, start SOC 2 preparation immediately.
- How much internal capacity do I have for implementing and operating controls? Lean teams may need external support from a vCISO or consultant to manage the project.
Phased Roadmap By Company Stage
Example: Fictional SaaS Startup Journey
DataFlow Analytics was founded in 2023 as a B2B analytics platform. In their first year, they focused on product development with minimal formal security documentation. By late 2024, enterprise prospects started asking about compliance. The founders implemented baseline policies and selected Drata for evidence collection in early 2025.
By April 2025, they completed a SOC 2 Type I, which was enough to close their first enterprise deal worth $60,000 annually. They ran their Type II observation period from May through October 2025 and received their final SOC 2 Type II report in December.
In January 2026, they asked their CPA firm to issue a SOC 3 for the same period. Now their website features a public compliance badge, their sales team has a document to share before NDAs, and their full SOC 2 Type II satisfies the detailed requirements of enterprise security reviews.
Explicitly map SOC 2 and SOC 3 investments to revenue objectives and board expectations. These are not purely technical compliance projects. They are commercial enablers.
Step By Step: Typical SOC 2 First, SOC 3 Later Workflow
Here is a realistic workflow from initial assessment to both reports being available for use:
- Run a readiness assessment: Evaluate current security controls, identify gaps, and estimate effort to reach audit readiness
- Select trust services criteria: Choose Security as baseline, add Availability or Confidentiality based on customer requirements
- Deploy compliance automation: Configure tools like Drata, Vanta, or Secureframe to collect evidence automatically
- Formalize security policies: Document access control policies, incident response, vendor management, and data protection practices
- Implement missing controls: Close gaps identified in the readiness assessment
- Collect evidence for Type II: Run controls consistently for 3 to 12 months while the platform logs activity
- Complete the SOC 2 audit: Work with your CPA firm to review evidence, test controls, and finalize the soc 2 report
- Request SOC 3 for the same period: Instruct the auditor to produce a public summary based on the completed examination
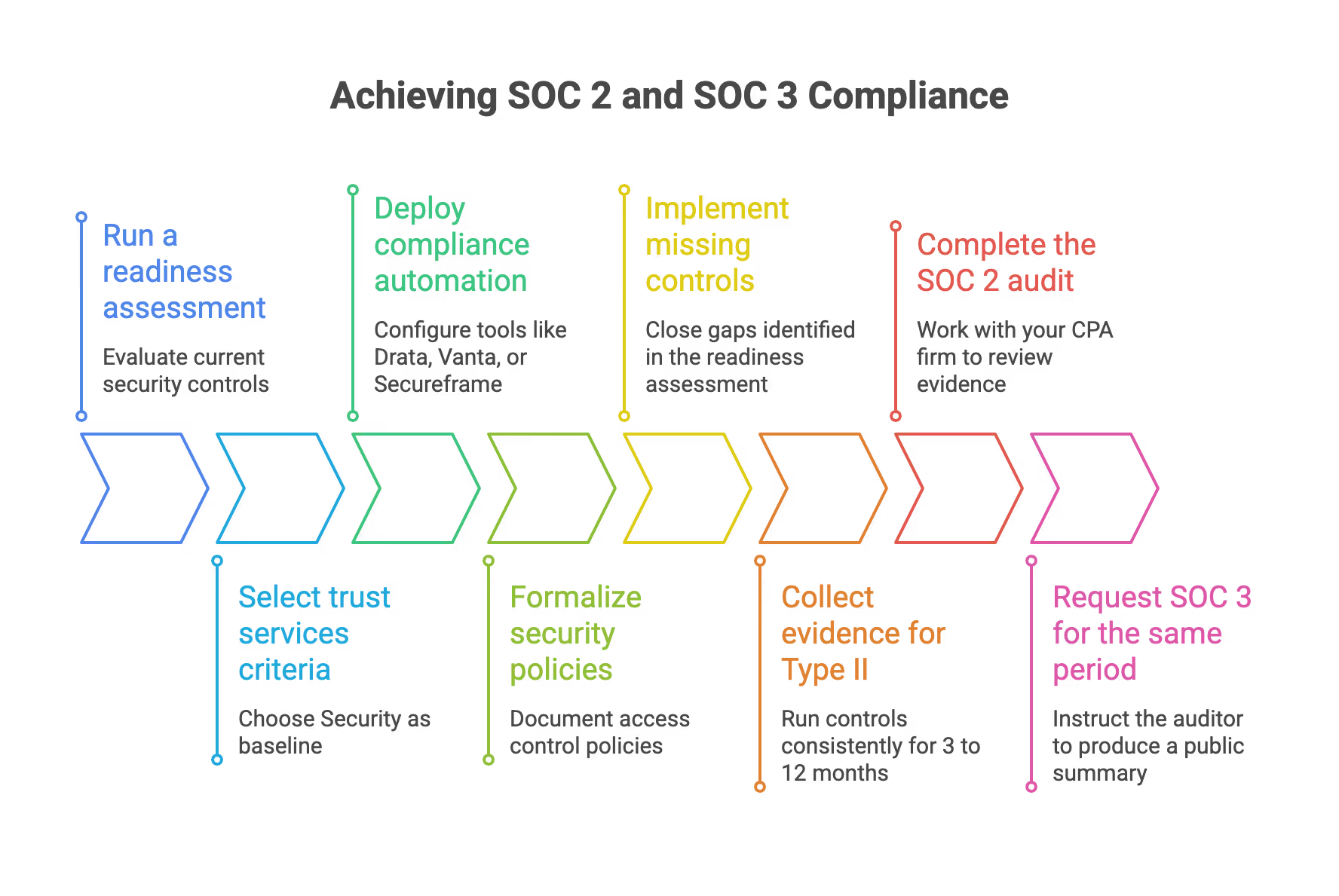
Key timeframes to plan for:
- Preparation: 2 to 3 months for a small but organized startup
- Type II observation: 3 to 12 months
- Report finalization: 2 to 4 weeks after fieldwork
Organize internal ownership by assigning clear responsibilities:
Using a virtual CISO or external advisor from SecureLeap keeps the project on schedule and translates auditor language into practical tasks for your internal team.
How SecureLeap Helps Startups With SOC 2 and SOC 3
SecureLeap focuses specifically on startups and small businesses rather than large enterprises. Our experience spans SaaS, fintech, and healthtech clients between pre seed and Series B stages, which means we understand the constraints you face.
Our approach combines advisory services, vCISO leadership, and implementation support for compliance automation tools such as Drata, Vanta, and Secureframe. This combination streamlines evidence collection and keeps internal teams focused on product delivery.
A typical engagement with SecureLeap includes:
- Running a SOC 2 readiness review to assess current state
- Prioritizing remediation tasks based on audit requirements and customer pressure
- Drafting security policies and operational controls
- Coordinating directly with your audit firm to reduce back and forth
- Managing the project timeline so lean engineering teams stay productive
SecureLeap can also design a combined approach where SOC 2, penetration testing, and optional SOC 3 reporting are bundled into a single security roadmap. This aligns with customer deadlines and upcoming fundraising rounds.
If you are evaluating whether SOC 2, SOC 3, or both belong on your roadmap, book a short consultation to review your pipeline, existing controls, and realistic timing without committing to a full audit immediately.
FAQ: SOC 2 vs SOC 3 For Startup Leaders
Can I skip SOC 2 and just get a SOC 3 report for marketing?
In practice, a SOC 3 without an underlying SOC 2 examination is rare and usually not enough to satisfy customer due diligence, especially for B2B SaaS selling into mid market and enterprise accounts. Auditors base SOC 3 opinions on the same control testing used for SOC 2, so a serious SOC 3 program almost always implies doing the SOC 2 level work first anyway. While SOC 3 can be a helpful marketing tool, it should be viewed as a complement to SOC 2, not a substitute, for startups that need to pass vendor security assessments. The right soc report depends entirely on who will read it.
How much more effort is a SOC 2 program compared to adding a SOC 3?
The majority of the workload is in designing, implementing, and operating controls for SOC 2, including evidence collection and auditor coordination over several months. Once the SOC 2 work is complete, requesting a SOC 3 for the same period usually adds only a modest incremental cost and limited extra effort since it is largely a different format of the same criteria and findings. Plan your budget and internal time for SOC 2 as the primary project, then treat SOC 3 as an optional add on that can be enabled if there is clear marketing value for reaching prospective customers.
Will investors expect SOC 2 or SOC 3 before a Series A or Series B round?
Investors rarely require formal SOC reports as a condition of funding, but by 2025 and 2026 many venture firms strongly prefer to see at least a concrete SOC 2 roadmap if the product handles sensitive customer data. A completed SOC 2 Type I or Type II report can strengthen trust with potential investors because it demonstrates operational maturity and reduces perceived security risk in the portfolio. SOC 3 is less important for investors than SOC 2, but can still be useful when a startup wants quick public proof of its security posture during due diligence. The signal matters as much as the technical content.
How do SOC 2 and SOC 3 relate to ISO 27001, HIPAA, or PCI DSS?
SOC 2 and SOC 3 are independent attestation reports focused on controls and do not replace regulatory or certification requirements such as ISO 27001, HIPAA, or PCI DSS. However, for many startups, a SOC 2 program can be designed so that its controls map closely to ISO 27001 Annex controls or HIPAA safeguard requirements, making it easier to pursue those frameworks later if needed. SecureLeap can help design an integrated control set that supports multiple frameworks at once, so the effort spent on SOC 2 and SOC 3 also moves the company closer to other compliance goals. This approach protects your investment in information security infrastructure.
What happens if a SOC 2 report includes exceptions or issues, and will that affect my SOC 3?
It is common for SOC 2 reports to include a small number of exceptions. Auditors describe these in detail along with management responses, which can still be acceptable to many customers if well explained. SOC 3 does not list each exception in the same level of detail, but a materially adverse finding could affect the overall opinion and therefore limit the ability to claim full compliance in a public report. Handle known gaps proactively with remediation plans and work with advisors such as SecureLeap to minimize the business impact of any exceptions that appear in your first SOC 2 cycle. Customers expect transparency about how you address issues, not perfection from day one.


%20(10)%20(1).png)

%20(4)%20(1).avif)
%20(3)%20(1).avif)