A SOC 2 Type 2 report is not just a certificate; it is a lengthy, detailed narrative and a scorecard of your company’s internal controls over a specified period, typically 6 to 12 months. The subject matter covered in the report includes the specific controls, processes, and areas evaluated during the audit. Unlike a Type 1 report, which takes a snapshot of a single day, a Type 2 report covering a specified period demonstrates ongoing compliance by assessing how your controls operated throughout that duration.
This guide will break down the SOC 2 Type 2 report section by section, explain why it matters to your customers, and outline the best practices to ensure your startup gets that coveted “Unqualified Opinion.”
The Anatomy of the Report
A standard SOC 2 report is generally divided into four or five main sections. While the formatting may vary slightly depending on the auditing firm, the structure remains consistent.
One key section is the system description, which provides a detailed overview of the service organization's system, including its services, infrastructure, and internal control processes.
This section is essential for understanding the scope of the SOC 2 Type 2 report and assessing both the design and operating effectiveness of controls over a specified period.
Section I: The Independent Service Auditor’s Report
This is the very first thing your potential customers will read. It is the executive summary and the verdict. This section is a letter from the auditing firm directly to your management and your customers, attesting to the design and operating effectiveness of your controls.
The Opinion
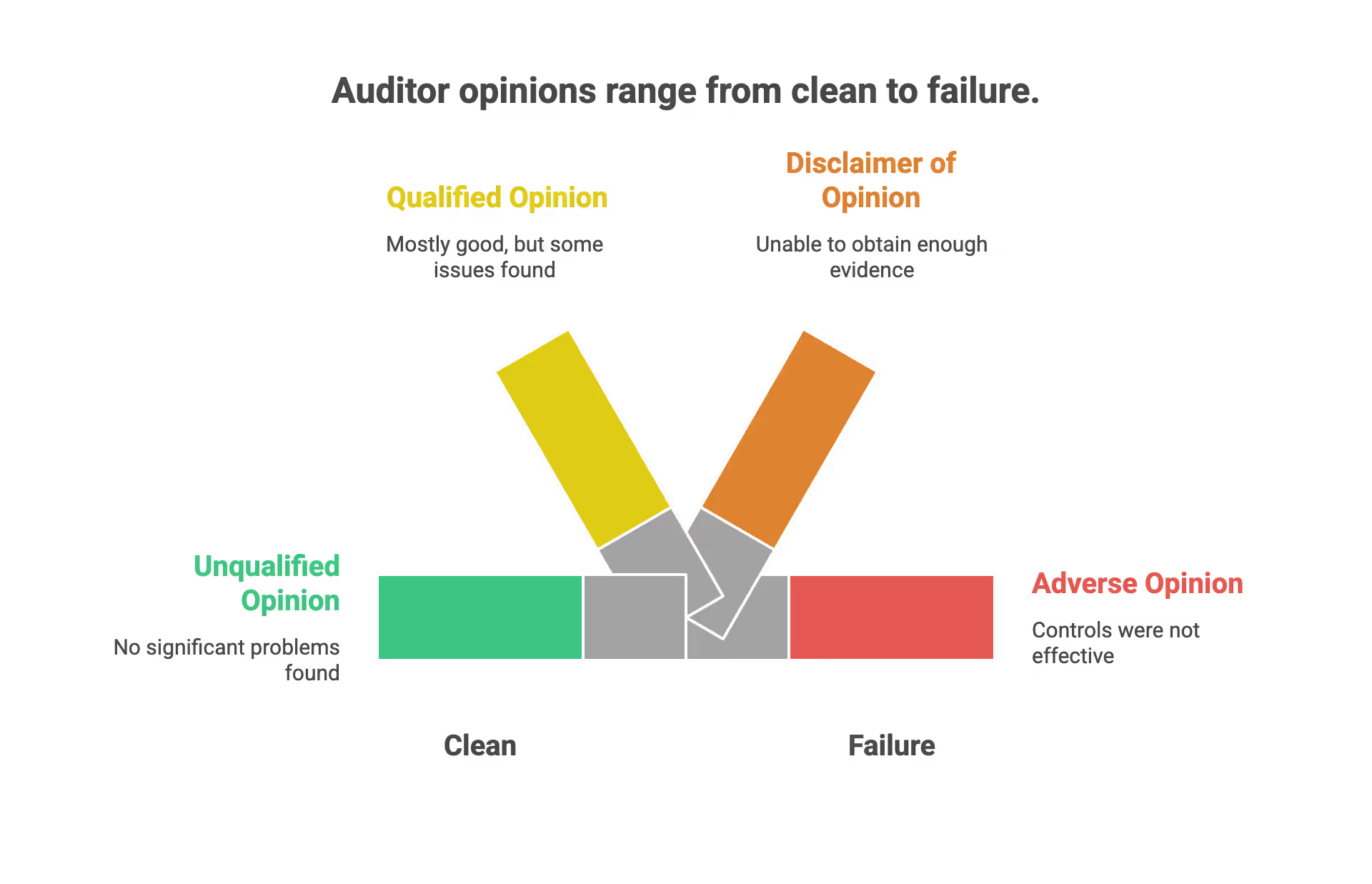
The most critical component here is the "Auditor's Opinion." This is the pass/fail grade. You are looking for specific terminology here.
- Unqualified Opinion
This is what you want. It sounds counter-intuitive, but "Unqualified" means "Clean." It means the auditor found no significant problems. Your controls were designed effectively and operated effectively during the audit period. - Qualified Opinion
This means "mostly good, but..." The auditor found issues (exceptions) that were significant enough that they could not give a fully clean report, but not bad enough to fail you entirely. - Adverse Opinion
This is a failure. The auditor found that your controls were not effective. Startups rarely release these reports; they usually fix the issues and re-audit. - Disclaimer of Opinion
The auditor was unable to obtain enough evidence to form an opinion. This is functionally a failure to report.
Key Takeaway for Startups
When sharing your SOC 2 with a prospect, they will scroll to Section I immediately. If they see "Unqualified Opinion," they often skip the rest of the details. If they see "Qualified," they will dig deep to see what you messed up.
Section II: Management Assertion
This section is written by you (the startup), not the auditor. It is a formal letter where the management of the company asserts that the description of the system is accurate and that the controls were suitable. As part of this assertion, management is also responsible for maintaining the organization's control environment to ensure that controls operate effectively and align with SOC 2 Type 2 requirements.
What It Contains
- Confirmation of Scope
You state exactly what systems were audited. For a SaaS startup, this usually includes your application production environment and the supporting tools (GitHub, AWS, Google Workspace). - Confirmation of Timeframe
You assert that the controls were operating during the specific dates listed (e.g., January 1st to December 31st). - Acknowledgement of Responsibility
You formally accept that it is your job to maintain security, not the auditor's job to fix it for you.
This section is largely legal boilerplate, but it is necessary to establish accountability.
Section III: Description of the System
This is the narrative section. It describes who you are, what you do, the environment in which you operate, and outlines the service organization's controls. This is often the most readable part of the report for non-technical stakeholders.
A typical system description includes:
- Infrastructure: The physical and virtual resources supporting your services, such as servers, networks, and devices. This includes data centers with physical and environmental security measures, as well as the use of cloud services to enhance operational efficiency and security.
- Software: The applications and systems used to deliver your services.
- People: The roles and responsibilities of staff involved in operating and securing the system. This also covers how you select and oversee service providers who may process, store, or transmit sensitive data on your behalf.
- Procedures: The processes and policies in place to ensure security, availability, processing integrity, confidentiality, and privacy. This includes controls applied during system development and when outsourcing, as well as how you manage relationships with service providers.
- Data: The types of information processed and stored, and how you manage customer data and process users data securely to maintain confidentiality and integrity.
The system description also documents the internal control environment, detailing how controls are designed, implemented, and monitored to manage risk and ensure compliance with SOC 2 requirements.

The Components of the System Description
The AICPA (the body governing SOC 2) requires you to describe your system across five categories:
- Infrastructure
This details the physical and virtual hardware. For 99% of startups, you will state that you have no physical data center and rely on cloud providers like AWS, Azure, or GCP. - Software
This lists the programs used to process information. This includes your actual product code, your database software, and operating systems. - People
Who manages the system? You will describe your organizational structure here. You don't list names, but you list titles: CTO, DevOps Engineers, Customer Support Leads. - Procedures
How does work get done? This summarizes your policies for changing code, granting access, and handling incidents. - Data
What kind of data do you hold? You verify if you are holding PII (Personally Identifiable Information), PHI (Health Information), or just generic business data.
The Concept of Subservice Organizations
This is crucial for modern startups. You rely on vendors like AWS or Heroku. In this section, you will use the "Carve-out Method."
- The Carve-out
You tell the reader: "We use AWS for hosting. We are not auditing AWS’s internal physical security because they do that themselves. We are only auditing our configuration of AWS." - Vendor Management
You simply reference that you check AWS’s SOC 2 report annually to ensure they are doing their job.
Section IV: Relevant Aspects of the Control Environment
This is the “meat” of the report. It is usually the longest section and consists of giant tables. This is where the rubber meets the road.
The introductory paragraph typically outlines the scope of the SOC 2 Type 2 report and highlights the importance of testing controls to verify their effectiveness over the audit period. This ensures that controls are not only designed properly but are also operating as intended.
The tables are structured to show each control activity, mapped to the relevant Trust Services Criteria. These tables detail controls related to security, availability, processing integrity, confidentiality, and privacy, providing a comprehensive view of the organization’s compliance posture.
Each control activity is described, including the objective, the process, and the evidence collected. It is essential to ensure appropriate controls are in place to meet industry standards and achieve the required trust service criteria.
The results section summarizes the auditor’s evaluation of the organization’s controls, including whether the same controls were maintained and operated effectively throughout the audit period. This demonstrates consistency and reliability in the control environment, which is critical for SOC 2 Type 2 compliance.
The Table Structure
The tables in Section IV generally follow a three-column format:
- Control Objective / Criteria
This references the specific SOC 2 requirement (e.g., "The entity restricts access to confidential information"). - Control Activity
This is what your startup actually does.- Example: "Access to the production database is restricted to the Engineering Lead and is reviewed quarterly."
- Test Applied and Results
This is what the auditor did to prove you aren't lying.- Example: "Sampled 5 new hires and verified that background checks were completed prior to access. No exceptions noted."
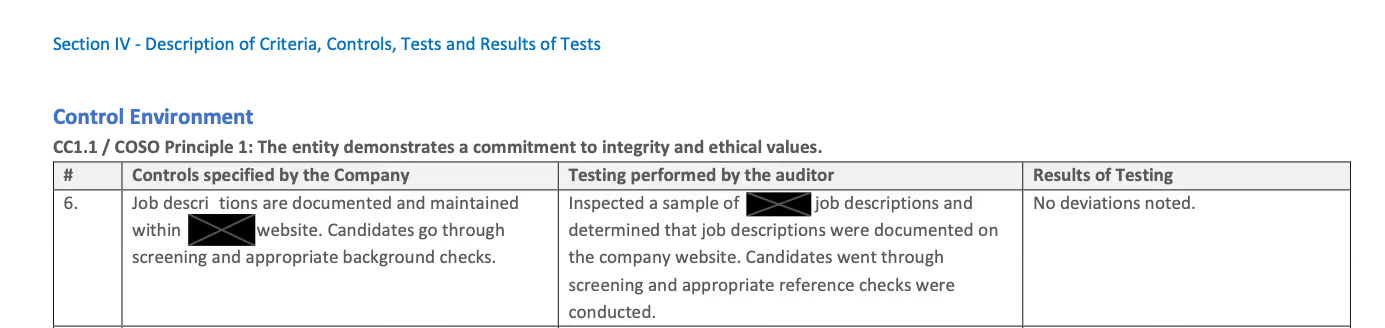
Reading the Results
- No Exceptions Noted
The auditor tested it, and it worked perfectly. - Exception Noted
The auditor tested it, and you failed that specific instance.- Example: You said you do performance reviews annually, but the auditor found one employee who didn't get one.
- Significance: One exception usually won't ruin your "Unqualified Opinion" (Section I), but a pattern of exceptions will.
Section V: Other Information (Optional)
This section is not audited. Startups often leave this blank, but you can use it to explain away a bad result.
- Management Response to Exceptions
If the auditor found an exception in Section IV, you can write a rebuttal here.- Example: "We missed a quarterly access review in Q2 due to a change in management, but we implemented an automated tool in Q3 to prevent recurrence."
Organization Controls and Compliance
For service organizations pursuing SOC 2, establishing strong organization controls and compliance practices is non-negotiable. Internal controls are the backbone of your security program. They’re the policies, procedures, and technical safeguards that ensure customer data is handled securely and with integrity. These controls must be carefully designed to align with the Trust Services Criteria and must be operating effectively throughout the audit period.
The Trust Services Criteria (TSC)
When building your report, you don’t just “do security.” You select the relevant Trust Services Criteria,formally known as the AICPA's Trust Services Criteria, for your audit. These criteria include Security (also referred to as the security criteria within the Trust Services Criteria), Availability, Processing Integrity, Confidentiality, and Privacy.
1. Security (Common Criteria)
- Status: Mandatory.
- Focus: Protection against unauthorized access.
- Startup Relevance: Every SOC 2 report includes this. It covers firewalls, 2FA, background checks, and code reviews.
2. Availability
- Status: Optional (but highly recommended for SaaS).
- Focus: Uptime and disaster recovery.
- Startup Relevance: If you have an SLA (Service Level Agreement) with enterprise clients promising 99.9% uptime, you should include this criteria.
3. Confidentiality
- Status: Optional.
- Focus: Protecting data restricted to a specific set of people, with a key emphasis on safeguarding confidential data through proper data classification, encryption, and secure handling policies.
- Startup Relevance: If you handle sensitive IP or business logic that isn’t public, include this. Most B2B SaaS companies include this.
4. Processing Integrity
- Status: Optional (and rare for general SaaS).
- Focus: System processing is complete, valid, accurate, and timely.
- Startup Relevance: Usually reserved for Fintech or transaction processing. If you are just storing data, you probably don't need this.
5. Privacy
- Status: Optional.
- Focus: Handling of personal data (GDPR/CCPA alignment).
- Startup Relevance: If you are B2C or handle sensitive PII (Social Security Numbers, health data), you need this. If you are B2B and only store business emails, "Confidentiality" is usually sufficient.
Best Practices for Startups Seeking SOC 2
Before starting the SOC 2 process, conduct a gap analysis and a readiness assessment to identify any deficiencies and ensure your controls are audit-ready.
Achieving a clean Type 2 report is an operational challenge. Here are the best practices to ensure success without burning out your engineering team.
Start by implementing controls that meet SOC 2 requirements and address any gaps found during your readiness assessment. Focus on building strong internal controls, as these are critical for a successful audit and demonstrate your organization’s commitment to security and operational integrity.
Throughout the process, ensure regulatory compliance with relevant data protection and privacy standards, which is essential for meeting both SOC 2 and broader industry requirements.
1. Scope Minimization
Don't audit everything.
- Isolate Production: Ensure your "Dev" and "Staging" environments are clearly separated from "Production."
- The Audit Boundary: Only include the Production environment in the audit scope. You do not want to fail your audit because a developer had weak security settings in a sandbox environment.
2. The "Bridge Letter" Strategy
A Type 2 report covers a past period (e.g., Jan 1 to June 30). What happens if a customer asks for your report in September?
- The Gap: Your report is 3 months old.
- The Solution: You issue a "Bridge Letter" (or Gap Letter). This is a short letter stating that since the audit ended on June 30, there have been no material changes to your security posture. This satisfies most enterprise buyers.
3. Standardize Onboarding and Offboarding
The number one source of "Exceptions" in startup reports is HR.
- Onboarding: Ensure background checks and policy acknowledgments happen before access is granted.
- Offboarding: When someone leaves, revoke access immediately (within 24 hours). Auditors love to catch startups who left a terminated contractor's GitHub account active for a week.
4. Vendor Management (Subprocessors)
You are responsible for the tools you buy.
- Annual Review: Set a calendar reminder to download the SOC 2 reports of your critical vendors (AWS, Slack, etc.) once a year.
- Review Documentation: When reviewing, ensure the SOC 2 report is service organization relevant—meaning it covers controls and trust service criteria that directly impact your operations. Keep a simple log stating, “Reviewed AWS SOC 2 on [Date], no issues noted.” This simple log is a required piece of evidence.
Maintaining a Strong Security Posture
Achieving SOC 2 compliance is only the beginning, maintaining a strong security posture is an ongoing commitment for service organizations. This means continuously monitoring your internal controls, conducting regular gap analyses, and performing readiness assessments to identify and address any weaknesses before they become issues. Leveraging security tools such as firewalls, intrusion detection systems, and encryption technologies is essential to defend against data breaches and security incidents that could compromise customer data.
Proactive security management, including timely updates and incident response planning, helps ensure your organization’s controls remain effective as your business evolves. By prioritizing security and demonstrating a culture of compliance, service organizations not only protect sensitive data but also build lasting trust with customers and partners. In today’s competitive landscape, a strong security posture is a key differentiator that can help your company win deals and maintain a stellar reputation.
Common Issues and Pitfalls to Avoid
Startups often stumble in specific areas. Avoiding these pitfalls can save you from a "Qualified Opinion."
1. The "Set and Forget" Trap
- The Issue: A startup configures their cloud security perfectly in January. They ignore it until December.
- The Reality: In July, a developer opened a port on the firewall for testing and forgot to close it.
- The Result: The auditor sees that the port was open for 4 months. That is a failure.
- The Fix: Use automated monitoring to catch configuration drift instantly.
2. Treating Policies as "Paper Only"
- The Issue: You download a template policy that says "We review access logs daily."
- The Reality: You are a 10-person startup. You do not have time to review logs daily.
- The Result: The auditor asks for proof of daily reviews. You don't have it. You get an exception.
- The Fix: rewrite policies to match reality. Change "Daily" to "Quarterly" or "Upon Alert." Only promise what you actually do.
3. Ignoring Physical Security (Even if Remote)
- The Issue: The company is fully remote, so you think physical security doesn't apply.
- The Reality: Auditors still care about company laptops.
- The Fix: You must prove that all company computers have hard drive encryption (FileVault/BitLocker) enabled. You need an MDM (Mobile Device Management) solution like Kandji or Jamf to enforce this.
4. Change Management Failures
- The Issue: Pushing code directly to production without review.
- The Requirement: SOC 2 requires that one person writes the code and a different person approves it.
- The Fix: Enforce "Branch Protection Rules" in GitHub. Require at least one approval before merging to the main branch. This is an automatic pass for this control.
5. The Evidence Scramble
- The Issue: Waiting until the audit begins to look for screenshots from 6 months ago.
- The Reality: You cannot generate a screenshot of a setting from the past. If you didn't capture it then, it's gone.
- The Fix: Again, automation platforms solve this. If you are doing it manually, you must take screenshots throughout the year, not at the end.
Summary: How to Read the Report Like a Buyer
To truly understand the value of the report, you should view it through the eyes of the Enterprise Procurement Manager who will critique it.
When they open your PDF, they are scanning for:
- Section I: Does it say “Unqualified Opinion”?
- Section III: Does the software architecture make sense? (e.g., Is the data encrypted at rest and in transit?)
- Section IV: Are there any exceptions in the table? If there are exceptions, did the company respond logically in Section V? Buyers will also assess the effectiveness of the company's internal controls described in this section.
- The Period: Is the report recent? If it’s more than 12 months old, they will demand a new one.
Buyers from financial institutions may also be interested in controls related to financial reporting, especially if your services impact sensitive financial data.
Why This Document Matters for Startups
Before diving into the pages, it is vital to understand the utility of this document. For a startup, this report serves three specific functions:
- Sales Acceleration
Enterprise buyers have vendor risk management teams. These teams will not let their company buy your software until they verify you will not leak their data. This report bypasses months of security questionnaires. - Trust Validation
It proves you do what you say you do. It moves your security posture from “trust us, we use AWS” to “here is independent verification that we configure AWS correctly.” This assurance is provided through an independent audit, which evaluates the effectiveness of your security controls and adds credibility to your security claims. - Operational Maturity
Going through the process forces your startup to document processes (HR, Engineering, IT). It inevitably makes your company run smoother and safer.
User entities, such as enterprise buyers and their risk management teams, rely on the SOC 2 Type 2 report to assess your company's controls and gain assurance about your security, privacy, and data management practices.
FAQ SOC2 Type 2 Report
What is a SOC 2 Type 2 report?
A SOC 2 Type 2 report is a detailed scorecard of internal controls for a company over a period of 6 to 12 months. It demonstrates ongoing compliance by assessing how effectively your security controls operated during that time.
What does an unqualified opinion mean in a SOC 2 report?
An unqualified opinion means the auditor found no significant problems with your security posture. It proves your controls were designed and operated effectively during the entire audit period.
What are the five Trust Services Criteria for SOC 2?
The five criteria include Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is mandatory for all reports while the others are optional based on your business needs.
What is a SOC 2 bridge letter?
A bridge letter is a document stating there have been no material changes to your security posture since your last audit ended. It helps satisfy enterprise buyers when your original report is several months old.
Why do startups need a SOC 2 Type 2 report?
Startups need this report to bypass lengthy security questionnaires and accelerate enterprise sales. It provides independent verification that your company handles customer data securely and maintains operational maturity.


%20(4)%20(1).avif)

%20(3)%20(1).avif)